Staying Ahead of Phishing Attacks
Phishing attacks threaten your data and systems. This listicle presents eight leading anti-phishing programs to strengthen your defenses. Learn how these tools combat phishing tactics, from employee training to advanced threat detection and response. We'll cover Cofense PhishMe, KnowBe4, Mimecast, Proofpoint, ESET, Barracuda, Cisco, and Microsoft Defender, providing valuable resources for individuals, businesses, and IT professionals. Bolster your security against phishing attacks with these powerful anti-phishing programs and consider secure email hosting for enhanced protection.
1. Cofense PhishMe
Cofense PhishMe is a leading anti-phishing program designed for enterprises seeking a robust human-driven defense against sophisticated phishing attacks. Instead of solely relying on technical filters, Cofense PhishMe focuses on educating and empowering employees to identify and report suspicious emails, effectively transforming them into an active line of defense. This approach is crucial in today's threat landscape where highly targeted "spear-phishing" attacks often bypass traditional security measures. The platform achieves this through a combination of realistic simulated phishing campaigns and engaging security awareness training modules. This allows organizations to proactively assess their vulnerability to phishing attacks and reinforce best practices for email security.
Cofense PhishMe offers a range of features to facilitate effective anti-phishing training and response. These include customizable phishing simulations that mimic real-world threats, from credential harvesting attempts to malware delivery. The interactive training modules reinforce key concepts and provide practical guidance on recognizing phishing indicators. A real-time analytics and reporting dashboard provides valuable insights into employee susceptibility and campaign effectiveness, enabling security teams to track progress and identify areas for improvement. Furthermore, integration with major security platforms and SIEM solutions allows for seamless incident response and threat intelligence sharing. A crucial feature is the "reporter button," a plugin that allows employees to easily flag suspicious emails directly to the security team for analysis. This facilitates rapid response to potential threats and helps refine the accuracy of phishing detection systems.
Pros:
- Highly Customizable Simulations: Leverage current threat intelligence to craft highly realistic and relevant phishing simulations.
- Human-Firewall: Turns employees into an active layer of defense, significantly reducing the risk of successful phishing attacks.
- Detailed Metrics & Benchmarking: Provides comprehensive reporting and allows comparison with industry peers to gauge effectiveness.
- Responsive Support: Offers dedicated customer support and implementation assistance for a smooth onboarding experience.
Cons:
- Premium Pricing: The robust feature set comes at a premium price point, which may not be suitable for smaller organizations with limited budgets.
- Time Investment: Full platform deployment and configuration requires a significant time investment for optimal effectiveness.
- Learning Curve: Advanced features and customization options can have a steeper learning curve for administrators.
- False Positives: The reporter button, while valuable, can occasionally generate false positives, requiring additional investigation by security teams.
Website: https://cofense.com/product-services/phishme/
Cofense PhishMe earns its place on this list due to its comprehensive approach to anti-phishing. By focusing on human-driven defense, it addresses a critical vulnerability that traditional security tools often miss. While the price point may be a barrier for some, the platform's robust features, customizable simulations, and detailed analytics make it a valuable investment for organizations prioritizing a strong security posture against phishing attacks. For organizations seeking a proactive and engaging approach to anti-phishing training, Cofense PhishMe is a powerful solution. Implementation tips include starting with a pilot program to assess employee susceptibility and refine training content, integrating the platform with existing security infrastructure, and regularly updating simulations to reflect the evolving threat landscape. While alternatives like KnowBe4 offer similar functionality, Cofense PhishMe stands out with its focus on enterprise-grade features and advanced customization options.
2. KnowBe4
KnowBe4 stands out as a leading anti-phishing program, focusing on the human element of security. Recognizing that employees are often the weakest link in an organization's defenses, KnowBe4 takes a proactive approach by training users to identify and avoid phishing attacks. This makes it a powerful tool for bolstering your cybersecurity posture and mitigating the risk of successful phishing attempts. Instead of solely relying on technical solutions, KnowBe4 educates your workforce to become a robust first line of defense. This approach is crucial in today's threat landscape, where sophisticated phishing techniques can bypass even the most advanced filters. For businesses seeking a comprehensive anti-phishing solution that empowers employees, KnowBe4 is a compelling option.
One of KnowBe4's core strengths lies in its simulated phishing campaigns. With thousands of customizable templates available, administrators can create realistic phishing scenarios to test employee awareness and identify vulnerabilities. These simulated attacks, combined with a vast library of training content covering a wide range of security topics, provide a practical and engaging learning experience. Beyond basic phishing awareness, the training modules also cover topics such as password security, social media safety, and physical security best practices. This breadth of coverage makes KnowBe4 a versatile platform for enhancing overall security awareness within an organization.
The PhishER tool, a key component of the platform, streamlines the process of managing reported phishing emails. It allows employees to easily report suspicious emails, which are then analyzed and categorized. This facilitates quick incident response and helps security teams identify emerging threats. The Security Awareness Proficiency Assessment further enhances the platform’s effectiveness by measuring employee knowledge and identifying areas needing improvement. Smart Groups allow for targeted training, ensuring that employees receive the most relevant instruction based on their roles and previous performance in simulated phishing tests.
Features:
- Automated phishing security tests with thousands of templates
- Extensive security awareness training library with videos and interactive modules
- PhishER tool for managing reported phishing emails
- Security Awareness Proficiency Assessment
- Smart Groups for targeted training based on user behavior
Pros:
- User-friendly interface that requires minimal technical expertise
- Regular content updates that reflect current phishing tactics
- Flexible scheduling options for training and phishing simulations
- Detailed reporting that tracks improvement over time
Cons:
- Can become expensive as organization size increases
- Some users report occasional template rendering issues in certain email clients
- The wealth of content can be overwhelming for administrators to navigate
- Advanced customization may require premium tier subscription
While pricing isn't publicly available, it's generally based on the number of users. Contact KnowBe4 directly for a customized quote. Implementation is straightforward, with minimal technical requirements. KnowBe4 integrates with most email platforms and offers comprehensive documentation and support.
Compared to other anti-phishing programs, KnowBe4's focus on security awareness training sets it apart. While other tools may prioritize technical solutions like email filtering and threat detection, KnowBe4 complements these measures by empowering employees to make informed decisions about security. This human-centric approach makes it a valuable addition to any organization's anti-phishing strategy.
Implementation Tip: Start with a baseline phishing test to assess your organization's current vulnerability. Then, use the results to tailor training campaigns to address specific weaknesses.
3. Mimecast Email Security with Targeted Threat Protection
For organizations seeking a robust, cloud-based solution against sophisticated phishing attacks, Mimecast Email Security with Targeted Threat Protection deserves serious consideration among the best anti-phishing programs. This comprehensive platform goes beyond basic email filtering and offers multi-layered defenses to protect your business from various phishing vectors.
Mimecast's strength lies in its proactive approach to threat detection. Instead of simply reacting to known threats, it employs advanced techniques like URL scanning with on-click protection. This means that even if a user clicks a malicious link in an email, Mimecast analyzes the destination in real-time before allowing access, preventing the user from landing on a phishing site. Attachment sandboxing further bolsters this protection by isolating and analyzing potentially harmful files in a secure environment before they can reach users' inboxes. This is crucial in mitigating threats from malware often delivered via email attachments. Furthermore, its impersonation protection leverages AI and threat intelligence to identify and block emails from spoofed senders, a common tactic used in phishing campaigns.
Beyond technical capabilities, Mimecast recognizes the importance of human awareness in the fight against phishing. The platform includes built-in employee awareness training modules to educate users about phishing tactics and best practices. These modules can significantly reduce the risk of successful phishing attacks by empowering employees to identify and report suspicious emails. Furthermore, end-user email security notifications and reporting tools offer transparency and allow users to actively participate in maintaining a secure email environment.
Key Features and Benefits:
- Real-time URL Scanning with On-Click Protection: Protects users even if they click on a malicious link.
- Attachment Sandboxing and Conversion: Neutralizes malicious attachments by converting them to safe formats.
- Impersonation Protection: Uses AI and threat intelligence to identify and block email spoofing attempts.
- Employee Awareness Training: Educates users about phishing threats and best practices.
- End-User Reporting Tools: Empowers users to report suspicious emails, enhancing security.
- Seamless Integration: Works with major email providers like Microsoft 365 and Google Workspace.
Pros:
- Comprehensive Protection: Covers multiple phishing vectors, offering a robust defense.
- Seamless Integration: Easily integrates with existing email infrastructure.
- Minimal False Positives: Reduces disruptions caused by legitimate emails being flagged incorrectly.
- Continuous Threat Intelligence Updates: Stays ahead of evolving phishing techniques.
Cons:
- Complex Administrative Interface: Requires dedicated time and effort to master.
- Higher Cost: More expensive than standalone anti-phishing solutions. (Pricing is not publicly available and requires contacting Mimecast directly).
- Additional Modules: Some advanced features require separate modules at extra cost.
- Mobile Experience: Mobile interface is not as feature-rich as the desktop version.
Implementation and Setup Tips:
While Mimecast offers robust protection, proper implementation is key. Working with a Mimecast partner or leveraging their professional services can streamline the setup and configuration process, especially for larger organizations. Focus on customizing the platform to your specific needs, including configuring policies for URL scanning, attachment handling, and impersonation protection. Thoroughly test the integration with your existing email infrastructure and educate your users about the new security features and reporting mechanisms.
Comparison with Similar Tools:
Compared to standalone anti-phishing solutions, Mimecast offers a more comprehensive approach by combining multiple layers of protection with employee training and awareness features. While solutions like Proofpoint and IronScales also offer advanced threat protection, Mimecast differentiates itself through its targeted threat protection modules and focus on seamless integration with existing email platforms.
Who should consider Mimecast?
Mimecast is a strong choice for organizations of all sizes, but particularly well-suited for medium to large businesses and enterprises with complex email security needs. Smaller businesses may find the cost and complexity a barrier, but the robust protection offered makes it a valuable investment for those who prioritize strong email security. If your organization requires advanced protection against sophisticated phishing attacks, seamless integration with existing email infrastructure, and values comprehensive employee awareness training, then Mimecast is worth exploring.
Visit Mimecast
4. Proofpoint Email Protection
Proofpoint Email Protection stands as a robust anti-phishing program designed for enterprise-level organizations seeking comprehensive email security. It goes beyond basic spam filtering, offering advanced threat protection against sophisticated phishing attacks, malware, and other email-borne threats. This is achieved through a multi-layered approach incorporating multiple detection engines, behavioral analysis, and machine learning to identify and neutralize threats before they infiltrate user inboxes. Its focus on preemptive security makes it a powerful tool in preventing data breaches, financial losses, and reputational damage. For organizations prioritizing a proactive defense against evolving email threats, Proofpoint Email Protection is a strong contender.
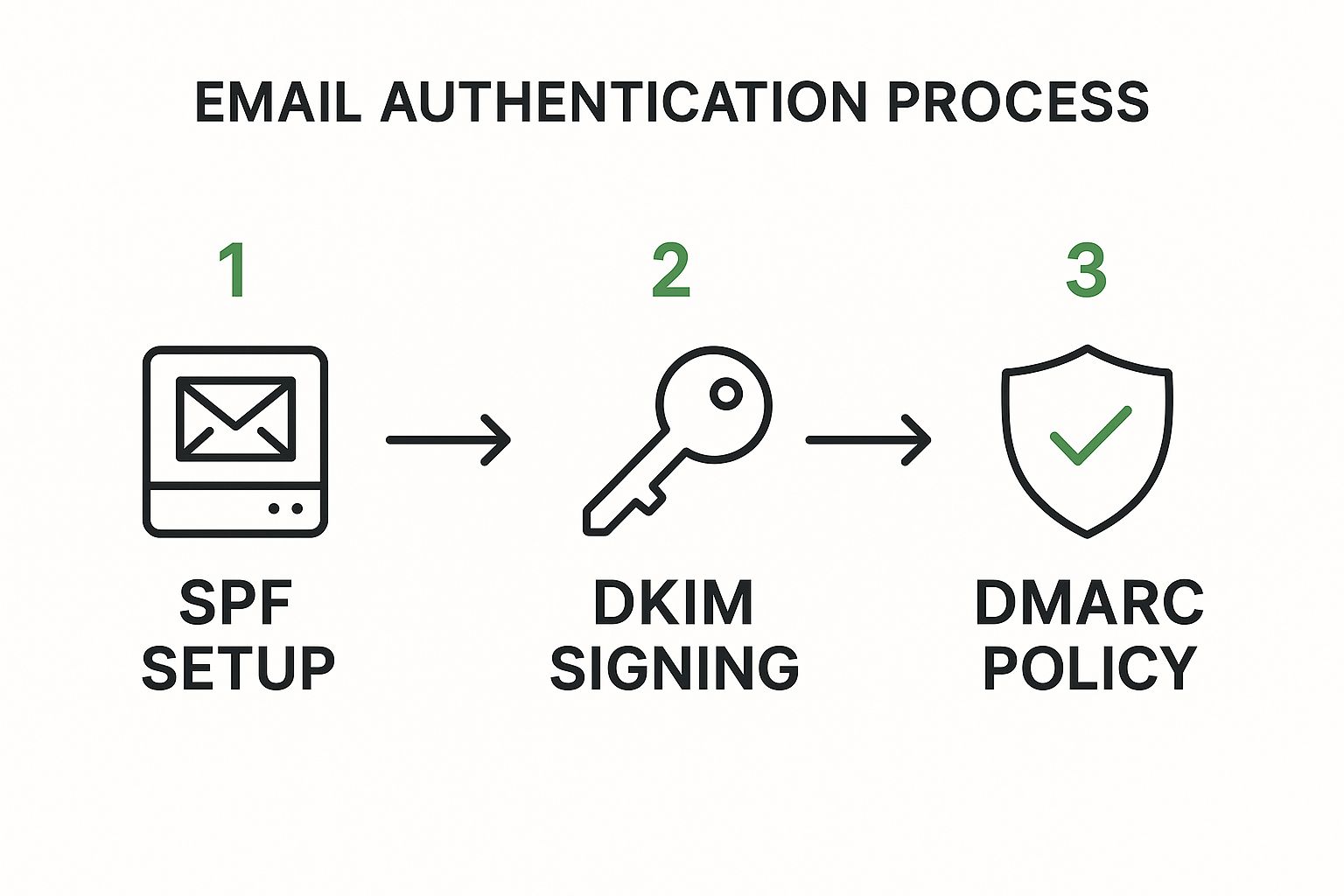
Proofpoint's strength lies in its advanced threat detection capabilities. It uses a combination of signature-based detection, anomaly detection, and dynamic malware analysis to identify both known and zero-day threats. Furthermore, its Business Email Compromise (BEC) protection specifically targets socially engineered attacks that often bypass traditional security measures. The platform also provides comprehensive email authentication management (DMARC, SPF, DKIM) to verify sender identity and prevent spoofing attacks. This multi-pronged approach to anti-phishing makes Proofpoint a valuable asset for organizations handling sensitive data and requiring robust protection.
For IT administrators and security professionals, Proofpoint offers granular policy controls, allowing customization based on specific user groups and risk profiles. Its integrated threat response and remediation capabilities streamline incident management, while user-centric risk scoring and targeted training empower employees to make informed decisions about email security. The platform also integrates seamlessly with other security tools and platforms, creating a unified security ecosystem. This level of control and integration allows organizations to tailor their anti-phishing strategies to their specific needs and security posture.
While Proofpoint offers exceptional protection, it's important to consider its potential drawbacks. The premium pricing structure may not be suitable for all budgets, particularly smaller organizations. Deployment and configuration can be complex, often requiring specialized IT expertise. Some users have reported occasional message delivery delays, a factor to consider for businesses requiring real-time communication. Finally, maximizing Proofpoint's effectiveness necessitates dedicated management resources for ongoing monitoring and optimization.
Features:
- Advanced threat detection using multiple analysis techniques
- Business Email Compromise (BEC) protection
- Email authentication (DMARC, SPF, DKIM) management
- Integrated threat response and remediation
- User-centric risk scoring and targeted training
Pros:
- Exceptional detection rates for sophisticated phishing attempts
- Granular policy controls for different user groups
- Strong integration with other security tools and platforms
- Regular updates based on current threat landscape
Cons:
- Premium pricing may not fit all budgets
- Deployment and configuration can be complex
- Some users report occasional message delivery delays
- Requires dedicated management resources to maximize effectiveness
Website: https://www.proofpoint.com/us/products/email-security-and-protection
Proofpoint Email Protection earns its place on this list due to its comprehensive and advanced approach to email security. While the cost and complexity may be a barrier for some, its robust features and high detection rates make it an ideal anti-phishing program for organizations prioritizing advanced threat protection and needing a powerful solution to combat increasingly sophisticated email-based attacks. For those managing large or high-risk environments, the investment in Proofpoint can offer significant peace of mind.
5. ESET Mail Security
ESET Mail Security earns its spot on this list of top anti-phishing programs thanks to its robust multi-layered approach to email security, combining machine learning with other detection technologies to effectively combat phishing threats. This makes it an excellent choice for businesses and organizations prioritizing strong email protection without excessive resource consumption. If you're looking for reliable protection against sophisticated phishing attacks without bogging down your mail server, ESET is worth considering.
This program goes beyond simply filtering spam; it actively protects against malware and phishing attempts embedded within emails, attachments, and links. For privacy-conscious individuals and businesses, this offers crucial protection against data breaches and other cyber threats commonly delivered via email. IT administrators will appreciate the flexible deployment options, catering to diverse environments, from on-premises Exchange and Domino servers to cloud-based Linux mail systems.
Key Features and Benefits:
- Multi-Layered Anti-Phishing: ESET utilizes a combination of advanced machine learning models, reputation checks, and heuristic analysis to identify and block phishing emails before they reach user inboxes. This comprehensive approach helps to catch even the most sophisticated phishing attacks that might slip past simpler filters.
- Real-time Scanning: All email components, including attachments and embedded links, are scanned in real-time, ensuring immediate protection against threats. This is crucial for preventing users from accidentally clicking malicious links or opening infected attachments.
- High Accuracy with Low False Positives: ESET boasts high detection rates while minimizing the chances of legitimate emails being flagged as spam or phishing attempts. This helps maintain smooth email flow and reduces the administrative burden of reviewing quarantined messages.
- Flexible Deployment: Whether you're running Microsoft Exchange, IBM Domino, a Linux mail server, or a cloud-based email platform, ESET offers flexible deployment options to suit your specific environment.
- Centralized Management Console: The comprehensive management console provides IT administrators with tools to monitor email traffic, review security events, and customize filtering rules. This centralized control simplifies management and enhances overall security posture.
Pros:
- Low System Resource Requirements: Compared to some competitors, ESET Mail Security has a relatively light footprint, minimizing the impact on server performance.
- High Detection Rates: The multi-layered detection engine provides excellent protection against phishing and malware with minimal false positives.
- Flexible Deployment Options: Supports various mail server platforms and deployment models (on-premises and cloud).
- Comprehensive Management Console: Provides centralized control over email security settings and reporting.
Cons:
- User Interface: While functional, the user interface is not as intuitive as some competing solutions and may require a slightly steeper learning curve.
- Reporting Features: While adequate for basic reporting, the reporting features may not be as robust as those offered by dedicated anti-phishing platforms.
- Limited End-User Training: ESET Mail Security focuses primarily on server-side protection and offers limited resources for end-user training and awareness, which is a crucial aspect of a comprehensive anti-phishing strategy.
- Advanced Features and Licensing: Some advanced features, such as sandboxing, might require additional licenses.
Pricing and Technical Requirements: Pricing for ESET Mail Security varies depending on the number of mailboxes and chosen deployment model. Detailed technical requirements and pricing information can be found on the ESET website.
Implementation Tips:
- Customize Filtering Rules: Tailor the filtering rules to your specific needs and environment to maximize effectiveness and minimize false positives.
- Whitelist Trusted Senders: Whitelisting trusted senders ensures that legitimate emails are not mistakenly flagged as spam or phishing attempts.
- Regularly Update Software: Keeping the software updated ensures that you have the latest protection against emerging threats.
Website: https://www.eset.com/us/business/mail-security/
By incorporating ESET Mail Security into your organization's cybersecurity strategy, you significantly enhance your defenses against increasingly sophisticated phishing attacks and other email-borne threats. It’s a valuable tool in the fight against phishing, offering a robust and efficient solution for securing your email communications. However, remember that no single solution is foolproof, and supplementing ESET Mail Security with regular security awareness training for your users is critical for building a truly comprehensive defense against phishing.
6. Barracuda PhishLine
Barracuda PhishLine is a robust anti-phishing program designed to transform your employees from security vulnerabilities into proactive defenders. It achieves this through a combination of simulated phishing attacks, comprehensive training content, and detailed reporting tools, making it a valuable addition to any organization's cybersecurity arsenal. Instead of simply reacting to phishing attacks, PhishLine helps you proactively prepare your workforce to identify and avoid them, strengthening your overall security posture against one of the most common cyber threats. This makes it a worthy contender amongst the best anti-phishing programs available.

PhishLine shines in its ability to create highly targeted simulations. With thousands of pre-built templates and extensive customization options, security teams can craft phishing scenarios that closely mimic real-world threats specific to their industry. For example, a financial institution could simulate phishing attacks related to wire transfers, while a healthcare provider might focus on scenarios involving patient data. This targeted approach ensures the training remains relevant and impactful for each user group.
The platform also offers computer-based training modules with gamification elements, making the learning process more engaging and encouraging active participation. Automated campaign scheduling and detailed analytics dashboards streamline the administrative workload, allowing security professionals to efficiently manage large-scale training programs and identify vulnerable users or departments. This data-driven approach empowers organizations to prioritize training efforts where they're needed most.
Features:
- Thousands of phishing templates and training modules
- Computer-based training with gamification elements
- Campaign automation and scheduling tools
- Detailed analytics and reporting dashboards
- Integration with Barracuda's email security ecosystem
Pros:
- Highly customizable phishing simulations
- Engaging training content that drives behavioral change
- Strong analytics for identifying vulnerable user groups
- Good value for organizations already using Barracuda products
Cons:
- Interface can feel dated compared to newer competitors
- Initial setup and configuration require significant time investment
- Some users report inconsistent rendering of templates across email clients
- Support response times occasionally cited as slower than expected
Website: https://www.barracuda.com/products/phishline
Pricing and Technical Requirements: Pricing information for Barracuda PhishLine isn't publicly available and typically requires contacting sales. Technical requirements vary depending on the deployment method (cloud-based or on-premises) and the size of the organization. Contacting Barracuda directly is recommended for detailed specifications.
Implementation Tips:
- Start with a pilot program targeting a small group of users to test and refine your phishing simulations and training content.
- Leverage the reporting tools to identify areas where employees are most susceptible to phishing attacks.
- Regularly update your phishing templates and training materials to stay ahead of evolving threats.
- Consider integrating PhishLine with other security awareness training initiatives to create a holistic approach to cybersecurity education.
Comparison with similar tools: While KnowBe4 is known for its vast library of content and user-friendly interface, and Proofpoint offers strong integration with its broader security platform, Barracuda PhishLine stands out with its robust customization options and particularly strong value proposition for organizations already invested in the Barracuda ecosystem. Its focus on targeted simulations and data-driven insights allows organizations to tailor their anti-phishing programs to their specific needs and effectively measure their impact.
7. Cisco Email Security
Cisco Email Security (formerly IronPort) is a robust anti-phishing program designed to safeguard organizations from sophisticated email threats, including phishing, business email compromise (BEC), and malware. Its multi-layered approach combines the power of Cisco Talos threat intelligence, machine learning, and behavioral analysis to identify and neutralize malicious emails before they reach user inboxes. This comprehensive protection makes it a strong contender for businesses seeking enterprise-grade email security. Cisco Email Security caters to a diverse audience including privacy-conscious individuals, SMBs, IT professionals, remote teams, and anyone seeking advanced protection against email threats.
Its features are extensive, encompassing advanced threat defense powered by Cisco Talos intelligence, URL filtering and time-of-click protection to prevent users from accessing malicious websites, graymail detection and safe unsubscribe options to manage unwanted newsletters and marketing emails, Advanced Malware Protection (AMP) for attachments to scan and block malicious files, and outbound email filtering to prevent data loss. For example, a company handling sensitive financial data can leverage Cisco Email Security to block phishing attempts targeting employee credentials and prevent the exfiltration of confidential information through outbound email filtering. Similarly, a remote team can benefit from its robust protection against malware delivered via email attachments, ensuring secure collaboration and communication.
One of the key strengths of Cisco Email Security is its backing by Cisco Talos, one of the largest threat intelligence networks in the world. This provides it with up-to-the-minute information on emerging threats, enabling it to proactively block malicious emails. Compared to anti-phishing programs relying on smaller or less sophisticated threat intelligence databases, Cisco Email Security offers a significant advantage in identifying and mitigating zero-day attacks. Its seamless integration with other Cisco security products further strengthens its defense posture, providing a unified security architecture for organizations already invested in the Cisco ecosystem.
Pros:
- Backed by Cisco Talos, one of the largest threat intelligence networks
- Seamless integration with other Cisco security products
- Multiple deployment options (cloud, on-premises, hybrid)
- Strong technical support infrastructure
Cons:
- Higher price point than many competitors
- Complex management interface with a steep learning curve
- Limited built-in end-user training capabilities
- Some features require additional Cisco security products for full effectiveness
Website: https://www.cisco.com/c/en/us/products/security/email-security/index.html
While pricing information isn't readily available, Cisco Email Security is generally considered a higher-end solution suitable for larger organizations or those with complex security requirements. Implementation typically involves working with a Cisco partner or reseller to determine the best deployment model and configure the system to meet specific needs. IT administrators responsible for setup should be prepared for a learning curve due to the platform's complex management interface. Despite its complexity, Cisco Email Security's robust features and comprehensive protection make it a worthy inclusion in this list of anti-phishing programs. Its ability to leverage advanced threat intelligence and provide multi-layered protection is particularly valuable for organizations seeking the highest levels of email security.
8. Microsoft Defender for Office 365: Integrated Anti-Phishing for the Microsoft Ecosystem
Microsoft Defender for Office 365 (formerly Office 365 ATP) stands as a robust anti-phishing program deeply embedded within the Microsoft 365 environment. This makes it a particularly compelling choice for organizations already leveraging Microsoft's suite of productivity tools. Its strength lies in providing comprehensive protection against sophisticated phishing attacks and other email-borne threats, making it a valuable asset in the fight against cybercrime. This positions it as a strong contender among other anti-phishing programs.
Defender for Office 365 utilizes a multi-layered approach to threat detection. It combines machine learning, heuristics, and the vast intelligence of Microsoft's global threat network to identify and neutralize phishing attempts before they reach user inboxes. This proactive defense helps prevent devastating breaches caused by malicious emails.
Key Features and Benefits:
- Safe Links: Provides time-of-click verification of URLs, protecting users even if they click on a link that was safe at the time of delivery but has since become malicious. This real-time protection is crucial in a dynamic threat landscape.
- Safe Attachments: Scans email attachments in a secure detonation chamber, neutralizing malware before it can infect user systems. This sandboxing technique provides an added layer of security against zero-day threats.
- Anti-phishing Protection with Mailbox Intelligence: Leverages AI and mailbox-specific data to identify and block targeted phishing attacks tailored to individual users or organizations.
- Attack Simulator: Allows administrators to run realistic phishing simulations to train employees on identifying and reporting suspicious emails. This proactive training reinforces best practices and strengthens the human firewall.
- Automated Investigation and Response (AIR): Automates the investigation and remediation of security alerts, freeing up IT staff to focus on other critical tasks. This automated response accelerates threat mitigation.
Pros:
- Seamless Integration: Integrates seamlessly with the existing Office 365 environment, simplifying deployment and management for organizations already invested in the Microsoft ecosystem.
- No Additional Infrastructure: Requires no additional agents or infrastructure, reducing deployment complexity and overhead.
- Regular Updates: Benefits from continuous updates from Microsoft's global threat intelligence network, ensuring protection against the latest threats.
- Cost-Effective: Offers good value for organizations already subscribing to Microsoft 365 E5 or as an add-on to other plans.
Cons:
- Limited Ecosystem Reach: Effectiveness is primarily limited to the Microsoft ecosystem, offering less comprehensive protection for organizations using other email platforms.
- Advanced Features Tied to Higher Tiers: Some of the most advanced features, like AIR, require the highest subscription tiers.
- Occasional False Positives: Some users report occasional false positives, which can disrupt workflows if legitimate emails are quarantined.
- Complex Management Interface: The management interface can be complex, with settings distributed across multiple admin centers.
Pricing and Technical Requirements:
Defender for Office 365 is available as part of Microsoft 365 E5 or as an add-on to other Microsoft 365 subscriptions. Pricing varies depending on the specific plan and the number of users. Technical requirements are minimal, primarily requiring a valid Microsoft 365 subscription.
Implementation and Setup Tips:
- Configure Policies: Customize policies to match your organization's specific security needs.
- Train Users: Educate users on how to identify and report suspicious emails. Leverage the Attack Simulator for realistic training scenarios.
- Monitor Reports: Regularly review reports to identify trends and potential vulnerabilities.
Comparison with Similar Tools:
While other anti-phishing programs like Proofpoint and Mimecast offer broader cross-platform compatibility, Defender for Office 365's tight integration with the Microsoft ecosystem makes it a compelling choice for organizations heavily reliant on Microsoft 365.
Website: https://www.microsoft.com/en-us/microsoft-365/security/office-365-defender
Defender for Office 365's comprehensive features, tight integration, and continuous updates make it a valuable anti-phishing program for securing your Microsoft 365 environment. Its multi-layered approach provides robust protection against evolving email threats, making it a worthy addition to this list of anti-phishing programs.
Anti-Phishing Software Feature Comparison
| Product | Core Features & Security ★✨ | User Experience & Support ★ | Value Proposition 💰 | Target Audience 👥 | Unique Selling Points 🏆 |
|---|---|---|---|---|---|
| Cofense PhishMe | Custom phishing sims, real-time analytics ✨ | Responsive support, detailed metrics ★★★★☆ | Premium pricing, high customization 💰 | Large enterprises, security teams 👥 | Human-driven defense, reporter button 🏆 |
| KnowBe4 | Thousands of templates, extensive training ✨ | User-friendly, updated content ★★★★☆ | Flexible, becomes costly at scale 💰 | SMBs to enterprises, admins 👥 | PhishER tool, smart groups targeting 🏆 |
| Mimecast Email Security | URL/attachment scanning, AI impersonation ✨ | Seamless integration, complex UI ★★★☆☆ | Higher cost, some features extra 💰 | Enterprises using MS/Google suites 👥 | Multi-layered URL & attachment defense 🏆 |
| Proofpoint Email Protection | Multi-engine detection, BEC protection ✨ | Granular controls, strong integration ★★★★☆ | Premium pricing, complex setup 💰 | Large enterprises, security teams 👥 | Exceptional detection, risk scoring 🏆 |
| ESET Mail Security | Multi-layer phishing & malware detection ✨ | Low resource use, less intuitive UI ★★★☆☆ | Flexible deployment, moderate cost 💰 | Various mail servers, SMBs 👥 | Cloud-powered scanning, low system load 🏆 |
| Barracuda PhishLine | Phishing templates, gamified training ✨ | Engaging content, dated interface ★★★☆☆ | Good value with Barracuda ecosystem 💰 | Organizations using Barracuda 👥 | Highly customizable sims, gamification 🏆 |
| Cisco Email Security | Talos intel, URL filtering, AMP ✨ | Strong support, complex interface ★★★☆☆ | Higher price, needs more Cisco tools 💰 | Enterprises preferring multi-deploy 👥 | Largest threat intel network backing 🏆 |
| Microsoft Defender for Office 365 | Safe Links/Attachments, attack simulator ✨ | Seamless MS integration, complex admin ★★★★☆ | Cost-effective for MS365 users 💰 | Microsoft 365 environments 👥 | Deep MS integration, automated response 🏆 |
Securing Your Future with Proactive Phishing Defense
Choosing the right anti-phishing program is crucial in today's digital landscape. This article explored a range of powerful tools, from Cofense PhishMe and KnowBe4, specializing in simulated phishing attacks for training, to comprehensive email security platforms like Mimecast, Proofpoint, ESET Mail Security, and Cisco Email Security. We also looked at targeted solutions like Barracuda PhishLine and the integrated protection of Microsoft Defender for Office 365. Each offers unique features and benefits, catering to diverse needs and budgets.
Key takeaways include the importance of layered security, combining robust anti-phishing programs with employee education. When selecting a tool, consider factors such as your organization's size, technical expertise, specific vulnerabilities, and budget. Look for features like real-time threat detection, advanced filtering, email authentication protocols, and reporting capabilities. Beyond using anti-phishing software, comprehensive security awareness training for your employees is crucial. This training empowers employees to identify and avoid phishing attempts, strengthening your overall security posture.
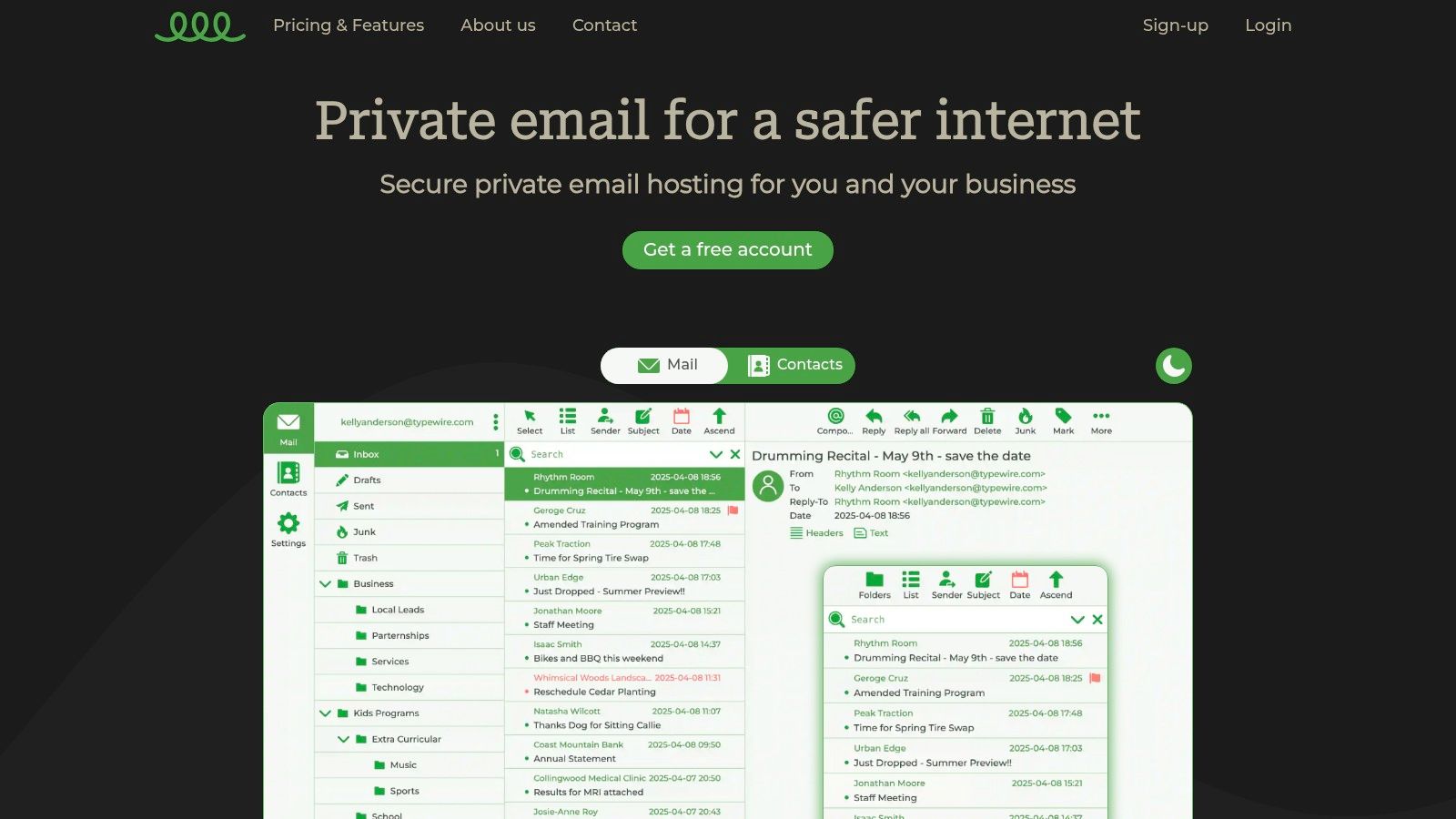
Implementing robust anti-phishing measures is a continuous process. By combining a secure email platform like Typewire with the programs highlighted above, you can significantly strengthen your organization’s defenses against phishing attacks. Regularly evaluate security practices and stay informed on emerging threats to ensure ongoing protection in the ever-evolving cybersecurity landscape. Remember, a proactive approach to cybersecurity is the best defense. Bolster your email security and protect sensitive information with Typewire, a platform designed with privacy and security in mind. Explore the benefits of a secure and private communication platform by visiting Typewire today.