Why Every Organization Needs A Robust Email Security Framework

Email remains a cornerstone of communication for businesses worldwide. This reliance, however, makes it a vulnerable entry point for cyberattacks. Simple spam filters are inadequate against today's sophisticated threats. A robust email security framework, founded on a strong email security policy template, is now crucial for protecting sensitive information and maintaining a strong security posture.
The Power of a Proactive Policy
An effective email security policy template provides a blueprint for secure email practices. It guides employees on acceptable email use and outlines incident response procedures. This shared understanding of responsibilities minimizes human error, a major factor in security breaches.
For instance, a clear policy outlines procedures for identifying and reporting phishing attempts. It also establishes accountability, ensuring adherence to security protocols.
Real-World Protection, Template-Based Efficiency
Implementing an email security policy template leads to measurable security enhancements. Organizations using these frameworks often see a significant reduction in successful email attacks. The template offers a structured approach to security, covering critical areas like password management, data handling, and incident response.
This standardized approach helps plug common security gaps. Using a template also streamlines implementation, bringing enterprise-grade security within reach of smaller businesses.
Market Growth and Investment in Email Security
The growing importance of email security is reflected in market trends. In 2024, the global email security market was valued at $18.5 billion. Projections indicate it will reach $24 billion by 2030, growing at a CAGR of 4.4%. This growth is fueled by the increasing frequency of cyberattacks, including phishing and ransomware. These threats are pushing organizations to invest in advanced email security solutions. For a deeper dive into these statistics, check out this resource: Email Security Market Growth
Adapting to the Evolving Threat Landscape
The cybersecurity landscape is in constant flux, with new threats constantly appearing. Consequently, email security policies must be living documents, regularly reviewed and updated. A robust framework offers the flexibility to adapt to new challenges and integrate emerging best practices.
Staying proactive is key to maintaining an effective defense against evolving cyber threats. For some actionable insights, consider these best practices: 8 Email Security Best Practices To Implement Now. This proactive approach is essential for mitigating risks and safeguarding against cyberattacks.
Understanding Today's Email Security Threat Landscape
Before creating an email security policy template, it's essential to grasp the current threat landscape. Cybercriminals are constantly refining their methods to circumvent traditional security measures. We're no longer dealing with just simple phishing emails; these are complex, multi-stage campaigns aimed at specific organizations.
Beyond Phishing: The Evolution of Email Threats
Phishing continues to be a substantial threat, but attackers are increasingly employing more advanced techniques. Business Email Compromise (BEC) attacks, for instance, frequently involve impersonating executives or trusted vendors to initiate fraudulent wire transfers or gain access to confidential data. These attacks prey on human psychology and established trust, which makes them very successful.
Attackers also combine technical exploits with social engineering. They might leverage a known software vulnerability for initial access and then utilize carefully crafted phishing emails to move deeper within a network. This multi-pronged strategy makes these attacks more difficult to detect and stop.
The Human Element: Exploiting Psychology in Email Attacks
Cybercriminals know that humans are often the weakest point in security. They use psychological tactics such as invoking urgency, fear, and curiosity to manipulate individuals into clicking malicious links or disclosing sensitive data. For example, a phishing email might warn of an imminent account suspension unless the recipient acts quickly, creating a sense of urgency that overrides careful behavior.
Attackers also personalize their emails with publicly available data, increasing their apparent credibility. This targeted approach, known as spear phishing, can be very effective even against security-conscious people. Understanding these tactics is essential for developing an email security policy template that tackles the human factor in security.
Identifying Your Organization's Specific Risks
Each organization has unique email security risks depending on its industry, size, and online presence. A financial institution, for example, might be a primary target for BEC attacks, while a healthcare provider might be more susceptible to ransomware attacks aimed at patient data. Assessing your organization's specific vulnerabilities and adjusting your email security policy accordingly is critical. This involves identifying the types of data you manage, the communication channels you use, and the potential consequences of a successful attack.
Phishing remains a constant challenge. In 2025, 47% of IT decision-makers cited phishing as a major threat, underscoring its continued impact on data security. Despite this, global implementation of essential security measures like DMARC is still low, with only around 8% of companies having a valid DMARC record. Learn more about these statistics: Find more detailed statistics here. This highlights the urgent need for comprehensive email security policies that proactively address phishing and other evolving threats.
Building a Proactive Defense Through Policy
A robust email security policy template should address both current and future threats. By staying current on emerging attack vectors and integrating best practices, you can establish a proactive defense that safeguards your organization from the constantly changing email threat landscape. Combining this proactive approach with regular training and awareness programs is vital for maintaining strong security.
Building Your Email Security Policy Template Foundation
Creating an effective email security policy template isn't about simply copying and pasting best practices. It's about understanding why certain policies work and how to adapt them to your organization's specific needs. This requires a structured approach that balances robust security with practical, everyday usability. A successful email security policy template serves as both a protective shield against threats and a clear roadmap for employees to follow.
Core Components of an Effective Policy
A strong email security policy template hinges on a few core components. These elements work together to create a secure email environment for everyone.
-
Acceptable Use Guidelines: These guidelines clearly define appropriate email usage within the organization. This covers sending and receiving emails, acceptable content, and any restrictions on using company email for personal communication. For instance, the policy should specify whether personal email use is allowed and, if so, to what extent.
-
Password Management: Strong passwords are the first line of defense against unauthorized access. Your policy should mandate strong password requirements and encourage regular password updates. Consider implementing a password manager to help employees generate and manage complex passwords.
-
Data Handling Procedures: How should employees handle sensitive information in emails? Your policy needs to detail procedures for encrypting confidential data. It should also emphasize minimizing the inclusion of sensitive data in emails unless absolutely necessary.
-
Incident Response Plan: This plan outlines the steps to take when an email security incident occurs. It should include procedures for reporting suspected phishing attempts or malware infections. This ensures a swift and coordinated response to any potential threats.
To further illustrate how these components contribute to overall email security, let's take a look at the following table:
Core Components Of Email Security Policy Templates
Essential sections and requirements that should be included in every comprehensive email security policy template
| Policy Component | Purpose | Key Requirements | Implementation Priority |
|---|---|---|---|
| Acceptable Use Guidelines | Defines appropriate email usage | Guidelines for sending/receiving emails, content restrictions, personal email usage rules | High |
| Password Management | Prevents unauthorized access | Strong password requirements, regular password changes, multi-factor authentication (MFA) | High |
| Data Handling Procedures | Protects sensitive data | Encryption protocols, data minimization guidelines, secure file sharing procedures | High |
| Incident Response Plan | Ensures prompt reaction to security breaches | Reporting procedures, contact information, investigation and remediation steps | High |
This table highlights the crucial role each policy component plays and the high priority they should be given during implementation. Addressing these areas creates a foundation for a robust email security posture.
The infographic below visually represents how different policy elements, when combined, mitigate threats.
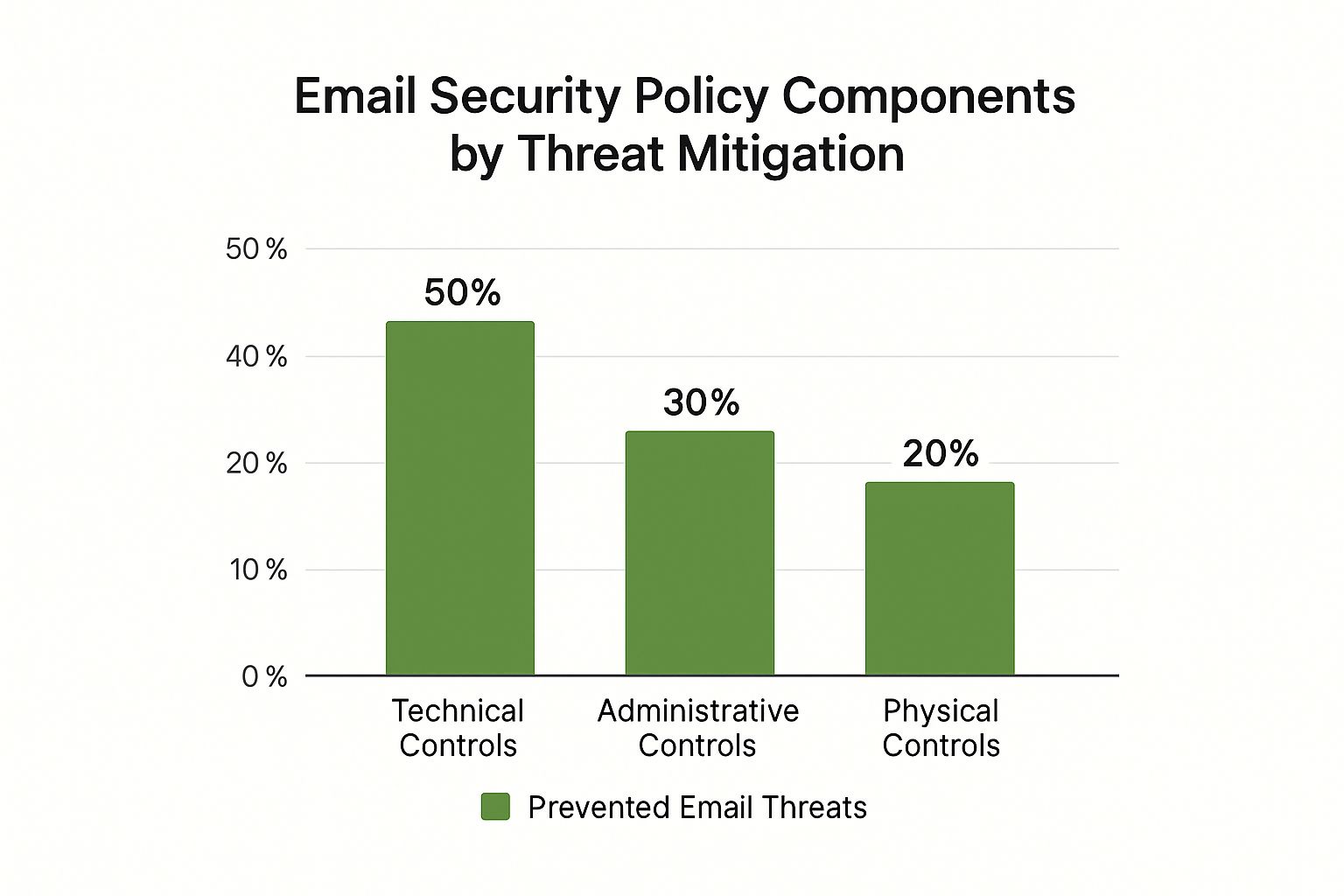
As the infographic illustrates, Technical Controls such as spam filters and antivirus software block 50% of email threats. Administrative Controls, including policies and training, address 30%, while Physical Controls like access restrictions handle the remaining 20%. This emphasizes the need for a multi-layered approach, combining technical measures, clear policies, and regular employee training. These controls are interconnected, strengthening the overall security of your organization.
Structuring Your Template for Clarity and Compliance
A well-structured template is easier to understand and encourages better compliance. Organize the policy content logically using clear headings, subheadings, and bullet points. Use simple, concise language, avoiding technical jargon that could confuse non-technical staff. This ensures everyone in the organization can easily understand the policy.
Including real-world examples can help illustrate key concepts and demonstrate the importance of following the policy. Showing the potential consequences of policy violations with specific scenarios helps employees understand the risks involved.
Balancing Security and Usability
While thorough security is paramount, the policy also needs to be user-friendly and practical. Overly restrictive policies can hinder productivity and frustrate employees. The goal is to strike a balance that safeguards the organization without unnecessarily disrupting daily workflow.
Gathering feedback from employees during the policy development process is crucial. This collaborative approach promotes buy-in and increases the chances of successful implementation. Their feedback can help refine the policy and address any potential usability issues before it's rolled out. A balanced policy ensures security measures are integrated smoothly into daily operations. This proactive approach is key to maintaining a robust and effective email security posture.
Navigating Compliance Requirements For Email Security Policies

Compliance with email security regulations is crucial for a strong security posture. This section explains the various regulatory requirements impacting email security policies, ranging from industry-specific rules to global standards. Creating an effective email security policy template starts with understanding these requirements.
Understanding The Regulatory Landscape
A range of regulations govern how organizations handle email security. These often overlap, creating challenges for businesses striving for compliance. For instance, the Health Insurance Portability and Accountability Act (HIPAA) in the US demands strict protection for health information sent via email. The European General Data Protection Regulation (GDPR) sets stringent rules for processing personal data, including data transmitted through email. Successfully navigating this requires a thorough grasp of the specific requirements affecting your organization.
You might be interested in: GDPR Compliance Checklist: Ensure Your Data Privacy Success
Addressing Multiple Frameworks Simultaneously
Organizations can simplify compliance by designing email security policies that satisfy multiple regulatory frameworks at once. This approach reduces the risk of oversight. Identifying common requirements across different frameworks allows for a unified policy that addresses multiple regulations, saving time and resources. This also allows for a stronger focus on essential security practices.
Documenting Compliance and Establishing Audit Trails
Compliance is not just about following the rules, but also demonstrating adherence. Clear documentation is essential. A detailed audit trail of email security activities is vital for demonstrating compliance during regulatory reviews. This should log actions such as security awareness training, policy updates, and incident responses. Thorough documentation proves compliance and facilitates ongoing improvement.
Furthermore, regulations are constantly evolving, particularly regarding Business Email Compromise (BEC) attacks. For example, PCI DSS v4.0 in the US mandates DMARC implementation by March 31, 2025 to avoid penalties. The EU NIS2 Directive and DORA Regulation require reporting of major cybersecurity incidents, including BEC attacks, and demand stronger security for third-party communications. Learn more about BEC statistics.
Adapting To Evolving Requirements
Regulations change over time. An adaptable email security policy template is therefore essential. This involves incorporating flexibility into the policy to facilitate updates without major revisions. Staying informed about regulatory changes and consulting with compliance experts helps organizations anticipate and adapt. This proactive approach ensures continuous compliance and minimizes the risk of penalties. Adaptable policies and continuous improvement are key to navigating the changing landscape of email security compliance.
Your Step-By-Step Email Security Policy Implementation Roadmap
Implementing a robust email security policy isn't just about creating a document. It's about building a culture of security throughout your organization. This roadmap provides practical steps for effectively deploying your email security policy.
Securing Buy-In and Building a Coalition for Change
Start by engaging key stakeholders. This includes representatives from leadership, IT, legal, and various departments. Explain the policy's importance, highlighting its benefits: reduced cyberattack risks, sensitive data protection, and regulatory compliance. Early leadership buy-in is crucial. It ensures the resources and authority needed for a successful rollout are available.
Phased Rollout for Smooth Adoption
A phased rollout minimizes disruptions and allows adjustments based on feedback. Begin with a pilot group, such as a specific department or team. Implement the policy within this group, gather feedback, and refine it based on their experiences. This pilot phase provides valuable insights and helps address unforeseen issues before a wider launch.
Next, expand implementation to other departments or teams. Clearly communicate the policy’s purpose and provide training on new procedures. Consistent communication and training are essential throughout this process. This ensures everyone understands their responsibilities and is comfortable with the new security measures.
Overcoming Common Implementation Challenges
Resistance to change is common. Address it by emphasizing the policy's positive impact on individual employees and the organization. Frame the policy as protective, not restrictive. For instance, explain how strong passwords safeguard their personal work accounts from unauthorized access. Address concerns openly and transparently, focusing on the shared goal of improved security.
Resource constraints can also be a hurdle. Prioritize essential policy components and the most impactful changes first. Start with critical areas like strong password requirements and procedures for reporting suspicious emails. You might find this helpful: How to master your inbox with these top email management tips. Gradually implement other aspects as resources allow. This ensures core security measures are in place from the outset.
Measuring Success and Adapting Your Approach
Establish clear metrics to measure the policy’s effectiveness. Track reported phishing attempts, compliance with password requirements, and response times to security incidents. Regularly review these metrics to assess the policy’s impact and pinpoint areas for improvement. This data-driven approach allows for fine-tuning and ensures long-term effectiveness.
Practical Timelines and Checkpoints
Develop a realistic implementation timeline with specific milestones and deadlines. Communicate progress regularly to stakeholders and adjust the timeline as needed. Transparency keeps everyone informed and maintains momentum throughout the process.
Creating a clear roadmap, securing stakeholder buy-in, and proactively addressing challenges are vital for successfully deploying your email security policy and creating a secure email environment. Consistent communication, training, and regular policy reviews ensure ongoing effectiveness and adaptation to evolving threats.
Keeping Your Email Security Policy Effective Over Time

An email security policy template isn't something you can create and then forget about. Just like any other security measure, it needs regular maintenance and improvement to stay effective. This means reviewing, updating, and adapting your policy to address new threats and changes within your organization.
The Importance of Continuous Improvement
The world of online threats is constantly changing. New phishing techniques, malware, and social engineering tactics appear all the time. Your organization's needs also change. New software, updated workflows, and even company growth can affect how well your email security policy works. Because of this, you need a proactive approach to policy management. Regular reviews help ensure your policy remains relevant and follows current best practices.
Measuring Policy Effectiveness Beyond Compliance
Meeting compliance requirements is important, but a truly effective policy does more than just check the boxes. You should focus on metrics that show real-world security improvements. For example, keep track of how many phishing attempts are reported, the success rate of phishing simulations, and how long it takes to resolve security incidents. This data gives you valuable insights into how well the policy is working and highlights any areas that need improvement.
Identifying and Addressing Security Gaps
Regular reviews help you find weaknesses in your email security policy before they can be exploited. This includes analyzing security incident reports, performing vulnerability assessments, and keeping up-to-date on new threats. This proactive approach allows you to strengthen your defenses and reduce the risk of successful attacks.
For instance, an increase in successful phishing attacks might show a need for better user training or stronger technical controls. Quickly addressing these gaps is crucial for maintaining strong security.
Incorporating Employee Feedback
Your employees are the first line of defense against email security threats. Their feedback is extremely valuable for improving both the security and usability of your policy. Regularly ask for feedback through surveys, focus groups, or informal conversations. This collaborative approach can help uncover practical challenges, identify training needs, and improve how well employees follow the policy.
Version Control and Change Management
Keeping track of policy updates is essential. Everyone needs to be using the most recent guidelines. Use a system to document changes, communicate updates to employees, and keep copies of older versions.
Effective change management is also crucial. When you update your email security policy template, clearly explain the changes to all staff, the reasons for the updates, and provide any needed training. This ensures a smooth transition and minimizes disruptions.
Establishing a Feedback Loop
Set up a system for continuous feedback and improvement. This could include regular policy reviews, periodic security awareness training, and ongoing communication with employees. Encourage employees to report security concerns and offer suggestions for policy improvements. This feedback loop keeps your policy adaptable and responsive to changing needs. It also creates a culture of security awareness within your organization.
Example Policy Management Timeline
To help you understand effective policy management, take a look at this sample timeline:
To ensure your email security policy stays effective and relevant, a structured management approach is essential. The following table outlines a recommended schedule for reviews, updates, and assessments throughout the year.
Email Security Policy Management Timeline
Recommended schedule for policy reviews, updates, and compliance assessments throughout the year
| Activity | Frequency | Responsible Party | Key Deliverables |
|---|---|---|---|
| Policy Review | Quarterly | IT Security Team | Updated policy document, gap analysis report |
| Security Awareness Training | Annually | HR/IT Security | Training completion records, employee feedback |
| Vulnerability Assessment | Bi-annually | IT Security Team | Vulnerability report, remediation plan |
| Compliance Audit | Annually | Compliance Officer | Audit report, compliance certification |
This regular review schedule helps your organization adapt to the evolving threat landscape and maintain a strong security posture. By prioritizing continuous improvement, organizations can make sure their email security policy is a powerful tool for protecting sensitive information and reducing risk.
Key Takeaways
Building a robust email security framework isn't a nice-to-have anymore; it's a necessity. This section summarizes key takeaways for creating a strong email security policy template, ensuring your organization is prepared to handle today's evolving threats.
Prioritize a Proactive and Adaptive Approach
The threat landscape is constantly shifting. Your email security policy template shouldn't be static. Instead, view it as a living document that adapts to new threats and changing business needs. Review and update your policy frequently to incorporate current best practices and address newly discovered vulnerabilities.
Understand the Human Element
Cybercriminals frequently exploit human nature to bypass even the most robust technical security. Your email security policy template should prioritize user education and awareness. Train your employees to recognize suspicious emails, avoid clicking malicious links, and report potential threats immediately. Strong passwords, multi-factor authentication, and regular security awareness training are vital to minimize human error.
Key Components of Your Email Security Policy Template
A truly effective email security policy template includes these essential elements:
-
Acceptable Use: Clearly define acceptable email usage within your company, encompassing content, personal use, and communication with external parties.
-
Data Handling: Outline specific procedures for handling sensitive information sent via email, including encryption protocols and data minimization strategies. For instance, your policy should explain how to encrypt confidential client data before sending it via email.
-
Incident Response: Develop a clear incident response plan for email security breaches. This should detail reporting procedures, contact information, investigation steps, and remediation measures. A well-defined plan ensures a swift and coordinated response to contain damage.
-
Compliance Integration: Ensure your policy aligns with relevant regulations like GDPR, HIPAA, or industry-specific requirements. This guarantees legal compliance and strengthens your overall security posture. Document all compliance measures and maintain audit trails to prove adherence.
Implementation Best Practices
Successfully rolling out your email security policy template requires careful planning and execution:
-
Stakeholder Buy-in: Get buy-in from leadership and all departments to create a culture of security awareness.
-
Phased Rollout: Implement the policy in phases, beginning with a pilot group. This allows you to gather feedback and fine-tune the process.
-
Regular Training: Provide ongoing security training and awareness programs to keep employees informed of current threats and best security practices.
-
Continuous Monitoring: Monitor key metrics like reported phishing attempts and incident response times. This data provides valuable insight into the policy's effectiveness and highlights areas for improvement.
Maintaining Momentum and Long-Term Effectiveness
Keeping your email security policy relevant requires consistent effort:
-
Regular Reviews: Conduct regular reviews of your policy to address emerging threats, incorporate feedback, and maintain alignment with evolving regulations.
-
Feedback Mechanisms: Create straightforward channels for employees to report security concerns, provide feedback, and suggest improvements to the policy.
-
Version Control: Use version control for all policy documents to make sure everyone uses the most up-to-date guidelines.
By focusing on these key takeaways, your organization can develop and implement a strong email security policy template that effectively mitigates risks, protects sensitive data, and fosters a secure email environment.
Ready to improve your email security and take control of your communications? Start your free 7-day trial of Typewire and experience the benefits of secure, private email hosting: Try Typewire Now