Scheduling an email sounds straightforward, right? You write your message, find the "send later" option, and pick a time. It’s a great way to make sure your email hits an inbox at just the right moment.
But there’s a crucial detail most people overlook: where that email sits and waits, and how its privacy and security are handled during that time.
Why Secure Email Scheduling Is Non-Negotiable

When you schedule an email, you're not just delaying its delivery—you're storing sensitive information. This is where the real privacy and security risks creep in, often without you even realizing it.
Many people use handy browser plugins or the built-in scheduling tools in standard email clients. The problem? These often save your scheduled messages—and sometimes your account password—directly on your computer or a third-party server with questionable privacy policies. This is what we call client-side scheduling, and it's a huge weak spot. If your laptop gets stolen or hacked, all your pending emails are an open book.
The Problem with Client-Side Scheduling
This is where a privacy-focused, hosted email platform like Typewire completely changes the game. Instead of parking your data on your personal device, your scheduled messages are kept on heavily encrypted, dedicated servers. This server-side approach adds a powerful layer of protection.
Let's break down why this difference is so important for your security and privacy:
- Centralized Security: Your emails are guarded by professional, enterprise-grade security systems, not just whatever antivirus you have running on your machine.
- Enhanced Privacy: Your login details and the content of your emails aren't just sitting in a browser cache or a local file, waiting for a breach. Hosted platforms protect your data from snooping.
- Reliable Delivery: The send is handled by a robust, secure server. It doesn't matter if your computer is off or disconnected—the email will go out on time, every time.
The real goal isn't just to send an email later. It's to ensure the message stays private and intact from the moment you hit "schedule" until it's delivered. True email security means protecting your data at every single stage.
Getting a handle on the bigger picture of email protection is essential. I always recommend that businesses explore comprehensive email security solutions to understand all their options.
And if you want to dig deeper into what makes an email genuinely private, check out this excellent resource on what is a secure email and why is it crucial for your privacy. For now, let’s focus on how Typewire’s secure, hosted approach puts you back in control.
Building a Secure Foundation on a Hosted Platform

Before you even think about scheduling your first email, let's talk about security and privacy. They are the bedrock of everything you'll do on a hosted email platform like Typewire. Setting up your account is just the beginning; true peace of mind comes from building layers of defense to protect your sensitive communications.
The single most important step you can take is enabling two-factor authentication (2FA). Think of it as a double-lock on your digital front door. Even if a bad actor steals your password, they can't access your account without the second code from your phone. It’s a simple move that drastically reduces the risk of unauthorized access.
Why Hosted Platforms Are a Security and Privacy Game-Changer
One of the best things about using a hosted email platform like Typewire is its secure infrastructure. When you schedule an email, that message isn't just sitting in a folder on your laptop, vulnerable to malware or physical theft. Instead, it’s stored securely on Typewire’s own private servers until it's time to send.
This server-side approach has massive advantages for your email security:
- Data Encryption at Rest: Your scheduled messages are encrypted while they wait, making them unreadable to intruders.
- No Device Dependency: Your email goes out on time, whether your computer is on, off, or halfway across the world.
- Centralized Protection: Your data is guarded by industrial-strength security measures, which go far beyond your personal antivirus software.
The core idea here is that your email's security shouldn't hinge on your personal device's safety. A hosted email platform moves that responsibility to a dedicated, purpose-built environment designed for privacy and protection.
I always recommend taking a few minutes to read up on Typewire's security features. It helps you appreciate the architecture working behind the scenes to keep your communications safe from the moment you start typing.
Getting this right isn't just about security, either—it's about impact. For instance, in B2B campaigns, simply adjusting your send times to match your recipient's work hours can boost engagement rates by 8.5%. It's a clear reminder that smart, secure scheduling really pays off. If you're curious, you can discover more B2B email marketing statistics that drive home the importance of timing.
Sending Your First Timed Email
Alright, let's put this into action. Scheduling a secure email on a hosted platform like Typewire isn't a complicated technical task—it's actually quite simple once you see it. We'll walk through a common scenario to get you started.
Picture this: you've just finished a critical project update, but your lead developer is in a different time zone. You want that email to be the first thing they see when they start their day at 9:00 AM, not buried under a pile of overnight messages. This is the perfect job for a scheduled send.
Writing and Scheduling Your Email
You'll start by writing your message just as you normally would. The magic happens right before you send it. Instead of clicking the big "Send" button, look for a "Schedule Send" option or a little clock icon. This is standard in most modern email platforms, especially those focused on security.
This is your control panel for timing. Clicking it reveals the options to dictate exactly when your message arrives.
Here’s what the Typewire composer looks like. It’s a clean slate, designed to keep you focused on your message without any of the usual digital clutter.
Nailing the Delivery Time
Once you're in the scheduling menu, you can pick a specific date and time. For our cross-time-zone scenario, you'd choose the date and set the time to 9:00 AM. Here’s a crucial detail: a good hosted email platform lets you select the recipient's time zone. This simple feature eliminates all the mental math and guesswork, ensuring your timing is perfect.
After you've locked in the time, just confirm the schedule. The email is then securely whisked away from your computer to Typewire's servers. It waits there, fully encrypted, until the precise moment it's set to be delivered. You can shut down your laptop and go about your day; the secure server takes care of the rest.
This is where a hosted email platform really shines. The moment you schedule the email, it's no longer sitting on your local device. It’s already protected within a secure, dedicated environment designed for privacy.
As you get more comfortable with scheduling, think about how timing can make your messages more effective. There's a real art to crafting effective timed emails, like sending a follow-up right after a meeting or event. It’s not just about security; it’s about making an impact.
Going Beyond the Basics: Advanced Scheduling and Privacy in Typewire
Once you get the hang of basic scheduling, you're ready to explore some of Typewire's more powerful tools. This is where you move from just sending emails later to gaining real control over your communications, all while keeping your data private and secure.
For example, think about automating those repetitive tasks. You can set up a weekly project summary to go out like clockwork every Friday at 4:00 PM. Set it once, and you’re done. Typewire takes care of the rest from its secure, hosted environment, which means no more last-minute scrambles to send routine updates.
This whole process is designed to be simple and secure, from composition to delivery.
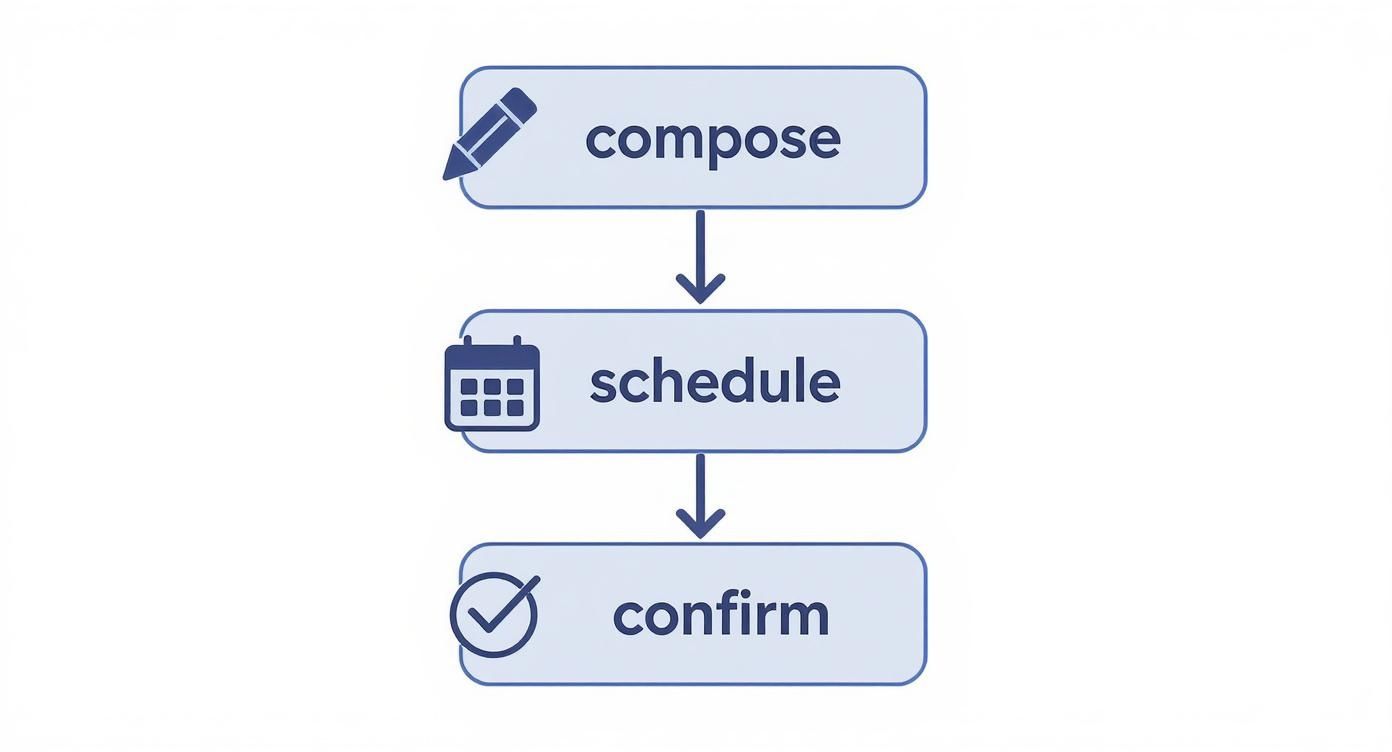
The crucial difference here is that every scheduled email is confirmed and stored on Typewire’s secure servers. It's not just sitting on your computer, waiting for you to be online and creating a privacy risk.
Taking Control with Advanced Privacy
True control isn't just about automation; it's about protecting the message itself. This is where a hosted platform like Typewire really shines. You can schedule emails with self-destruct timers, which adds an essential layer of privacy for sensitive information.
Imagine sending a confidential contract proposal that you’ve timed to arrive tomorrow morning. With this feature, you can also set it to automatically delete from the recipient's inbox 24 hours after they've read it. The information is there when they need it, and gone when they don't, enhancing your data security.
This capability also works seamlessly with encrypted messages. You can schedule an end-to-end encrypted email for a future date, confident that it remains completely unreadable—even to us—while it's waiting to be sent. If you're curious about how that works, you can learn more about what end-to-end encryption is in simple terms. It’s peace of mind for your most important communications.
The real power of a hosted email platform isn't just sending emails later; it's the ability to apply advanced security protocols to those future messages, giving you complete control over your data's lifespan and accessibility.
How you schedule your emails makes a huge difference in security. A dedicated platform like Typewire provides advantages that common email client plugins just can't match.
Here’s a look at how they stack up.
Typewire Hosted Scheduling vs. Standard Client Plugins
Many people use plugins for their email clients, but a dedicated, hosted email platform offers a fundamentally different—and more secure—approach.
| Feature | Typewire (Hosted Platform) | Standard Client Plugins |
|---|---|---|
| Security | Emails are encrypted and stored on secure, private servers until the send time. Your device doesn't need to be involved. | Emails and credentials might be stored locally on your device or a third-party server, creating potential vulnerabilities. |
| Reliability | Delivery is guaranteed whether your computer is on, off, or offline. Once scheduled, it’s set. | Sending depends entirely on your device being powered on and connected to the internet at the scheduled time. |
| Privacy | Your data and message content are protected within a privacy-first infrastructure. Your info isn't the product. | Your data could be exposed to the plugin developer or other third-party services, creating significant privacy risks. |
Ultimately, plugins can be convenient, but they often operate as a "middleman" that introduces new security and reliability concerns. A hosted system like Typewire handles everything on its own secure servers, ensuring your scheduled messages are safe and sent on time, every time.
How to Manage and Troubleshoot Scheduled Emails
https://www.youtube.com/embed/-6aOf-aGNUg
So, you've scheduled your email and can cross it off your to-do list. But what happens when plans change? A last-minute update, a new piece of data, or even just a typo you spot after the fact.
Luckily, managing your pending messages in a secure, hosted email platform like Typewire is simple. It gives you complete control right up until the scheduled send time.
Making Changes on the Fly
Everything you’ve scheduled lives in a dedicated “Scheduled” folder right in your Typewire dashboard. Think of this as your command center for future communications.
From here, you can click into any email to tweak the content, adjust the send time, or just cancel it altogether. This is a huge advantage of using a server-side, hosted platform—your control isn't tied to your own device being online.
Responding to Real-World Scenarios
Let's say you've lined up a weekly report to go out every Friday, but a key attachment needs a last-minute revision. Or maybe you've scheduled a big proposal for tomorrow morning and suddenly realize you need to update a few figures.
No sweat. With Typewire, you just:
- Head to the "Scheduled" folder and find the email.
- Open it up and make your edits—correcting text, swapping attachments, you name it.
- Resave the schedule. The updated version is now securely queued up on the server, ready to go at the original time.
This centralized control means you can rest easy knowing an outdated or incorrect message won't slip through the cracks, all while maintaining the privacy of your data.
A question I get a lot is, "What if my email didn't send?" With a hosted platform, this is pretty rare since delivery doesn't depend on your computer being on. If you suspect an issue, the first place to check is your "Sent" folder. More often than not, it went out just fine.
With the number of global email users expected to hit 5.61 billion by 2030, the inbox is more crowded than ever. Properly managing your scheduled sends is a small but critical step to ensure every message you send is polished, professional, and secure.
If you're curious about where things are headed, you can read the full report on email trends to get a better sense of why precise, secure communication is becoming so important.
Answering Your Top Questions About Secure Email Scheduling
Diving into a secure, hosted email platform for scheduling emails for the first time usually brings up a few questions. It’s a different way of thinking about your workflow, moving security from your own computer to a protected server. So, let's tackle some of the most common things people ask.
The biggest one I hear is whether a platform like Typewire is actually safer than a simple browser extension. The answer is a resounding yes. Most browser plugins handle your data on your local device or bounce it through various third-party servers, which can open up security holes and privacy issues. A dedicated, hosted platform keeps everything inside its own encrypted environment, so your account login and the email itself are never exposed.
Can I Still Edit My Emails? And What About Encryption?
People also worry about losing flexibility. What if you need to change something after you’ve scheduled an email? Not a problem. On a hosted platform like Typewire, all your queued-up messages live in a "Scheduled" folder.
You can pop in there anytime to:
- Tweak the body text
- Swap out an attachment
- Change the recipient list
- Adjust the send time
You have full control right up until the moment it goes out the door.
The most important question for anyone serious about privacy is about encryption. Does scheduling an email somehow compromise its security? Absolutely not. Your email is encrypted before it even gets stored on the server, and it stays locked down the entire time it's waiting to be sent.
It’s only decrypted when your recipient opens it, giving you true end-to-end protection. This means your message is safe while you write it, while it waits on a secure server, and all the way to its final destination. You never have to trade security for the convenience of scheduling.
Ready to get a handle on your email timing and privacy? Typewire gives you a secure, hosted platform built to protect your conversations without cutting corners. Start your free 7-day trial today and see for yourself.