When your inbox feels like it's under siege, the most powerful weapon you have is surprisingly simple: the "Mark as Spam" button. While advanced email security is crucial, the single most effective thing you can do right now is to start aggressively teaching your email provider what you consider junk, enhancing your personal email privacy.
Your First Line of Defense Against Spam

Before diving into advanced settings, let's focus on the basics. Reclaiming your inbox isn't about just deleting unwanted messages; it’s about proactive training that strengthens your email security. Every time you mark an email as spam, you’re feeding valuable information to your email service's algorithm, helping it get smarter about what to block in the future.
The scale of the problem is staggering. In 2025, experts predict a mind-boggling 376.4 billion emails will be sent every day. Nearly 47% of that traffic is pure spam. That breaks down to about 176 billion junk messages flooding servers daily, each one a potential threat to your email privacy and security.
Develop Strong Email Habits
Think of your primary email address as a key to your digital life—guard it carefully to protect your privacy. How you interact with your inbox day-to-day can either invite a flood of spam or build a solid defense against it.
Here are a few essential habits to start today:
- Don't Engage with Spam. Period. Never reply, click a link, or even open an email that looks suspicious. Opening a message can trigger tracking pixels, confirming your address is active and compromising your email privacy. That's an open invitation for more junk.
- Use a "Burner" Email Address. Set up a secondary email for online shopping, forum sign-ups, and newsletters. This keeps your main inbox—the one for private correspondence and important business—clean and secure.
- Be Relentless with the 'Mark as Spam' Button. This is your best tool. It does more than just move a message. It reports the sender and helps your email provider improve its global filters, bolstering security for everyone. It's the most direct feedback loop you have.
Every time you report junk, you're not just tidying up your own space. You're contributing to a smarter, safer email environment for millions. Think of it as a vote for better email security.
To give you a clear starting point, here are the most effective actions you can take right now.
Immediate Actions to Reduce Spam
| Action | Why It Works | Impact Level |
|---|---|---|
| Mark as Spam (Don't Delete) | Trains your email provider's algorithm to recognize and block similar threats in the future. | High |
| Use a Secondary Email | Protects your primary email's privacy and prevents it from landing on spam lists. | High |
| Never Click or Reply | Any interaction confirms your email is active, making you a target for more spam and phishing. | High |
| Unsubscribe Carefully | Only use the unsubscribe link on emails from trusted, known senders to avoid security traps. | Medium |
| Review App Permissions | Check which third-party apps have access to your email account and revoke unnecessary ones to secure your data. | Medium |
Taking these five steps consistently will make a noticeable difference almost immediately, setting the foundation for a much more private and secure inbox.
The Power of Proactive Filtering
Beyond these manual habits, your email platform has powerful tools built-in. By combining smart practices with the intelligent features of your email client, you can create a truly formidable barrier.
Later, we'll discuss why a hosted email platform offers superior protection, but for now, just know that leveraging the right tools is key. Understanding the best email spam filters available can give you a major head start. These initial actions are what set the stage for a private, secure, and spam-free inbox.
Put Your Email Client's Tools to Work

While flagging junk mail helps your email provider learn, it's a purely reactive move. To truly get a handle on spam, you need to be proactive with your email security. This is where your email client—whether it's Gmail, Outlook, or Apple Mail—steps in as your best line of defense. Think of it as your inbox's personal security guard.
These platforms are packed with features that go way beyond a simple spam folder. They let you build a custom defense system that automatically spots, sorts, and deletes unwanted messages. It’s like setting up a series of digital tripwires; when a spam email triggers one, it’s handled instantly, protecting you from potential security threats.
Create Smart Filters and Rules
Filters (or "rules" in some apps) are your secret weapon for automating inbox security. You can tell your email service exactly what to do with messages that contain specific words, come from unverified senders, or have other sketchy characteristics.
For instance, a classic spammer trick is to use fake urgency or obvious misspellings in the subject line to sneak past basic filters. You can fight back by setting up a filter that looks for these exact patterns.
Here’s how that might look in the real world:
- The Problem: You’re getting flooded with emails that have subjects like "URGENT ACTION Requirred" or "Your_Account_Is_Locked!"
- The Solution: Build a filter that scans for keywords like "requirred," "locked," or "suspended." You can even add specific emojis that spammers love to use.
- The Action: Set the rule to automatically send these messages straight to the trash. You won't even have to see these potential security risks.
This simple shift turns your inbox from a passive mailbox into an active, intelligent gatekeeper. You stop waiting for spam to show up and start neutralizing it on sight.
How to Build an Effective Spam Filter
A truly robust filtering system isn’t about one "magic" filter—it’s about layering several smart rules that work together to create a powerful net for your email security.
Here are a few strategies I've found incredibly effective:
- Filter by Sender: Noticing junk from weird domains like .xyz or .info? Create a rule that automatically trashes any message from senders using that domain.
- Filter by Keywords: Is your inbox full of fake lottery wins or crypto scams? Set up a filter for phrases like "congratulations you've won," "bitcoin bonus," or "claim your prize." Just be specific so you don’t accidentally catch legitimate emails.
- Filter for Missing Info: Real companies almost always send emails from a person or department name. Create a rule that scrutinizes emails where the "From" field is just an email address with no name attached—a common sign of spoofing.
The point of a filter isn't just to delete junk. It's to automate your defenses, freeing up your mental energy and lowering the odds you'll accidentally click a malicious link. A solid set of rules is one of the best answers for how to get spam emails to stop for good.
Train Your Provider’s AI
Every time you hit "Mark as Spam" or "Report Phishing," you’re doing more than just cleaning out your inbox. You're feeding valuable data back to your email provider's AI, contributing to a global security network.
Think of it like teaching a smart assistant. It might get things wrong at first, but the more you correct it, the better it gets at protecting your privacy. When you report an email, the system analyzes everything about it—the content, sender reputation, malicious links—to identify patterns. This collective intelligence helps block billions of spam messages every single day.
By consistently using these built-in tools, you’re creating a personalized shield that adapts over time. Your email client learns what you consider a threat, making its automatic filtering far more accurate for your specific security needs.
The Unsubscribe Dilemma: When to Click and When to Just Delete
We’ve all been there. Staring at an annoying email, your cursor hovers over that little "unsubscribe" link at the bottom. It feels like the right move—a quick, satisfying click to reclaim your inbox privacy. But hold on. Clicking that link can sometimes be the worst thing you can do for your email security.
With legitimate marketing emails from companies you know and trust, unsubscribing works perfectly. They follow regulations like the CAN-SPAM Act. The problem is, spammers have turned this feature into a weapon.
When you click an unsubscribe link in a junk email, you’re not opting out. You're essentially confirming to the sender that your address is active. Your address instantly becomes more valuable, marked as "live," which means you're about to get more spam, not less. This action compromises your email privacy by validating your data for shady operators.
Legitimate Unsubscribe vs. a Spammer's Trap
So, how do you tell a safe unsubscribe from a security trap? It comes down to a bit of digital detective work. Once you know what to look for, spotting the fakes gets a lot easier.
A legitimate email from a reputable company almost always has a few tell-tale signs of safety.
- A Professional Footer: Look for a physical mailing address and other company details near the unsubscribe link. Real businesses are required to include this.
- A Recognizable Sender: Is the "From" address what you’d expect? Think
newsletter@wellknownbrand.com, not something bizarre likeofferZ@b8x9-deals.xyz. - Familiarity: This is the big one. Is it from a store you've shopped at or a newsletter you actually remember signing up for? If it feels familiar, it's likely safe to unsubscribe.
Here's the golden rule: If you have no idea who the sender is or why they're emailing you, do not click unsubscribe. Just mark it as spam and delete it. This is the safest move for your email security.
Red Flags That Scream "Delete Me Now"
On the flip side, spam emails are often full of obvious security red flags. The unsubscribe link in these emails is just bait, often leading to a phishing site or a malware download.
Keep an eye out for these classic warning signs:
- Vague Greetings: If it starts with "Dear Customer" or "Hello Friend" instead of your actual name, be suspicious.
- Fake Urgency: Spammers love to create panic. Watch out for subject lines like "Your Account Is At Risk" or "Immediate Action Required."
- Sketchy Links: Before you even think about clicking, hover your mouse over the link. Does the URL preview look totally random or completely different from the sender's name? That’s a massive security risk.
- Typos and Bad Grammar: Big companies have editors. Emails that look like they were written by a robot are almost always junk.
Learning to pause and quickly vet that unsubscribe link is a huge step in protecting your email privacy. When you're not sure, the safest bet is always to hit "Mark as Spam." It denies the spammers the validation they're after and helps your email provider learn what to block in the future.
Diving Into Advanced Email Security Protocols
Once you've tightened up your own inbox habits, the real heavy lifting against spam happens at the server level. This is where advanced security protocols work behind the scenes, acting as an invisible shield to protect your email privacy by verifying that senders are who they say they are.
While you don't personally configure these as a user, understanding what they do is key to knowing why a secure, hosted email platform is so important.
Think of SPF, DKIM, and DMARC as the backbone of modern email security. They function like a digital passport check, making it exponentially harder for spammers to impersonate or "spoof" legitimate domains, like your bank or a favorite online retailer.
When an email provider—especially a privacy-focused hosted email platform—implements these standards correctly, they build a formidable defense against phishing and spoofing. This technical backbone is a huge part of what separates a basic, free email account from a truly secure one.
A Breakdown of Email Authentication
Imagine a postal service that checks the ID of every single person sending a letter. That's a pretty good analogy for what these email security protocols do. Each one adds another layer of verification.
Here are the three main players in this security trio:
-
SPF (Sender Policy Framework): This is the first line of defense. A domain owner publishes a list of all the mail servers that are officially allowed to send emails for them. If an email arrives from an unapproved server, it’s an immediate security red flag.
-
DKIM (DomainKeys Identified Mail): This adds a unique digital signature to every email, like a tamper-proof seal on an envelope. The receiving server checks this signature to ensure the message wasn't altered in transit, protecting its integrity.
-
DMARC (Domain-based Message Authentication, Reporting & Conformance): DMARC is the policy that ties SPF and DKIM together. It instructs receiving servers what to do if an email fails either check—either quarantine it (send it to spam) or reject it entirely, stopping the threat before it hits your inbox.
This authentication framework is a critical component of email security and privacy.
How Global Spam Trends Impact Your Inbox
The fight against spam isn't just a technical one; it also has a geographic dimension. A massive amount of spam originates from just a few countries, which actually helps security experts create more targeted blocking strategies.
For instance, 2024-2025 data shows the United States leading with 8 billion spam emails sent daily. China is right behind at 7.6 billion, with Russia and Germany each contributing 7.3 billion.
This concentration allows security services to use tools like email blacklists to filter out up to 90% of junk mail by simply blocking IP addresses from known spam hotspots. This is another area where your choice of hosted email platform matters. A provider with a strong security posture will automatically integrate these real-time blackhole lists (RBLs), adding a powerful layer of protection you never even have to think about.
The flowchart below gives a good visual of how to think about managing the different kinds of email that make it past these filters.
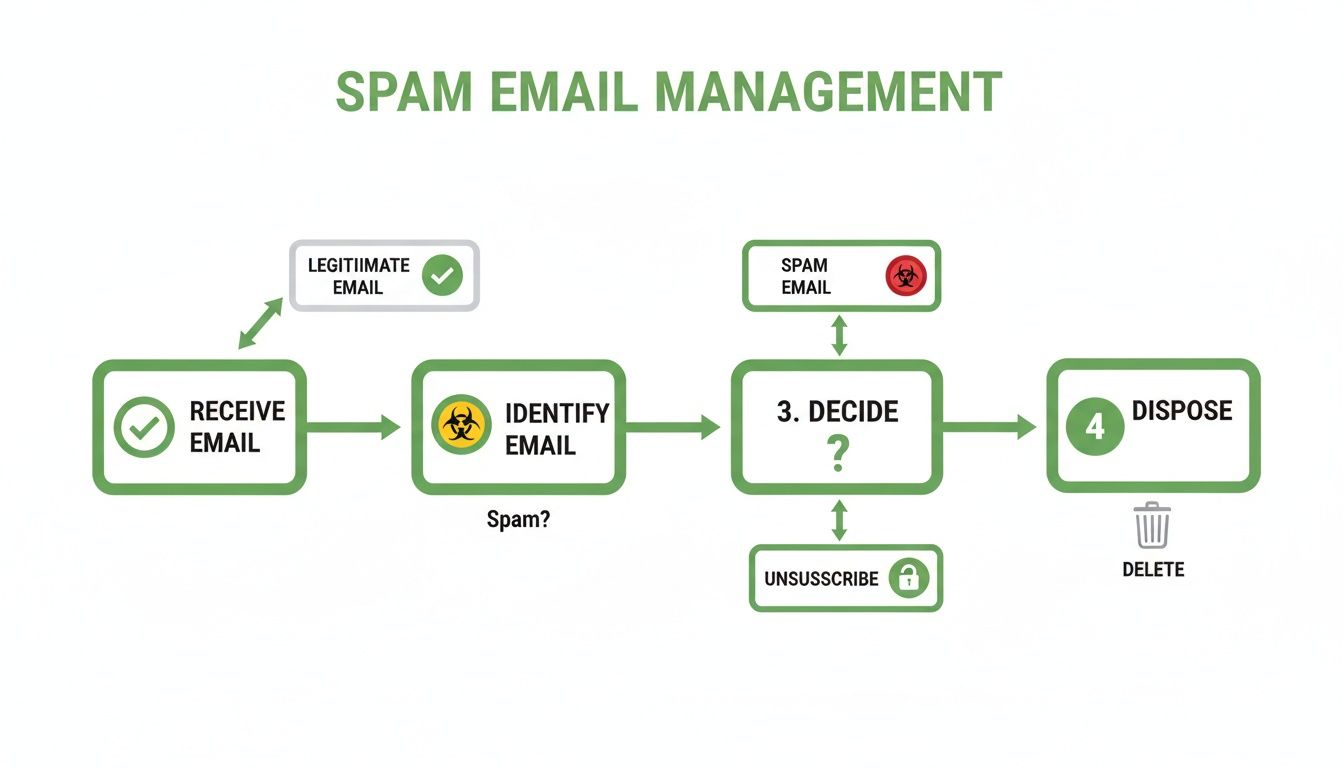
It’s all about learning to spot the difference between legitimate senders you can just unsubscribe from and malicious spam that needs to be deleted on sight.
Your email host's commitment to implementing SPF, DKIM, and DMARC correctly is one of the most significant factors in determining how to get spam emails to stop. It’s the foundational security layer that filters out the worst offenders before they can compromise your privacy.
Why This Matters for Your Email Privacy
At the end of the day, these advanced protocols are all about establishing trust and verifying identity. They are what ensures an email from yourbank.com actually came from your bank and not from a scammer.
This validation process is a cornerstone of modern email security. When you choose a hosted email platform that truly prioritizes your privacy, you're investing in this robust infrastructure. The result is a much quieter, more secure inbox with far fewer phishing attempts and spoofed messages.
If you're curious to learn more about the technical reasons why emails go to spam, digging into the mechanics of spam filters can really highlight just how crucial these authentication protocols are.
Why Your Choice of Email Host Matters

So far, we've covered the tactics you can use to manage spam. But what if you could stop most of it before it ever reaches you? The single most impactful decision for your long-term email security and privacy is choosing the right hosted email platform.
This goes way beyond a clean interface; it's a fundamental choice about who controls your data and prioritizes your security.
Most of us start with free email services, but there's a hidden cost to "free." The business model of many free services revolves around data monetization. Your personal information, browsing habits, and even email content can become a product sold to advertisers. This creates a conflict of interest when it comes to aggressively blocking unwanted mail.
This is where privacy-focused, hosted email platforms offer a completely different philosophy. When you pay for an email service, you are the customer, not the product.
Free Services vs. Privacy-First Platforms
The difference between a standard free email service and a dedicated private, hosted email platform is night and day. Free providers use generalized algorithms to filter billions of messages. It’s effective on a massive scale, but it lacks the advanced privacy controls and robust email security of a dedicated service.
In contrast, a privacy-first hosted email platform like Typewire builds its entire infrastructure around user security and privacy. This means you get access to more advanced, proactive anti-spam technologies and a rock-solid commitment to keeping your data private. Your emails are never scanned for keywords to sell you ads, and your data is never mined for marketing profiles.
This distinction becomes critical when dealing with phishing, a massive email security threat. An astonishing 3.4 billion malicious emails are sent every single day. While major providers block millions, plenty still slip through, contributing to what experts predict will be over 80% of all cyberattacks in 2025.
You can see more of these alarming trends in Zensec's latest security report, which highlights the 1,003,924 attacks reported in just the first quarter of 2025. A secure, hosted email platform acts as your first line of defense, a powerful buffer that stops these threats cold.
Choosing a hosted email platform is the ultimate long-term solution for anyone serious about getting spam emails to stop. It shifts your strategy from constantly cleaning a messy inbox to preventing the mess from ever happening.
Comparing Free vs. Privacy-Focused Email Hosts
Let's break down the real-world differences. Moving to a paid, private hosted email platform is an investment in your digital security and privacy. You're not just getting an email address; you're getting a suite of protections designed to keep your communications safe and your inbox clean.
Here's a quick look at how the two models stack up:
| Feature | Standard Free Email (e.g., Gmail, Yahoo) | Privacy-Focused Host (e.g., Typewire) |
|---|---|---|
| Business Model | Ad-supported; user data is often monetized. | Subscription-based; focused on user privacy. |
| Email Privacy | Emails may be scanned for advertising purposes. | Strict no-scanning and no-tracking policies. |
| Email Security | Good, but generalized for a massive user base. | Advanced, multi-layered filtering with more user control. |
| Encryption | Standard transit encryption. | End-to-end encryption options for maximum security. |
| Customer Support | Often limited to community forums and help docs. | Dedicated, responsive customer support for security issues. |
Ultimately, a privacy-focused hosted email platform gives you control. You get the peace of mind that comes from knowing your provider's primary goal is to protect your communications, not monetize them. This alignment of interests is what makes it such a powerful tool in the fight to stop spam emails for good.
Frequently Asked Questions About Stopping Spam
Even when you've done everything right, a few stubborn questions about spam can linger. Getting a better handle on the finer points of email privacy, security protocols, and what your hosted email platform is doing behind the scenes can really clarify things. Let's tackle some of the most common concerns.
Can I Ever Completely Stop All Spam Emails?
Let's be realistic: getting to a 100% spam-free inbox is probably not going to happen. But you can absolutely get it down to a tiny, manageable trickle. The goal isn't an impenetrable fortress; it's to create such a smart, multi-layered defense that spammers move on to easier targets.
Think of it as building a highly effective filtration system. By consistently applying the right strategies—aggressively marking junk, creating smart filters, and, most importantly, choosing a secure hosted email platform—you can catch the overwhelming majority of unwanted messages. Each step adds another layer to your email security, making your inbox a much quieter and safer place.
Why Do I Get Spam Even If I Never Give Out My Email?
This is easily one of the most frustrating parts of dealing with spam. You guard your email address carefully, yet junk still shows up. It's usually not something you did wrong; it's a numbers game played by automated systems that threaten your email privacy.
Your address can fall into the wrong hands in a few key ways:
- Data Breaches: Your email was likely part of a data breach from a service you've used. Hackers steal these databases and sell them on the dark web.
- Website Scraping: Automated bots crawl public web pages—like forums or social media profiles—and "scrape" any email addresses they find.
- Dictionary Attacks: Spammers use software to generate millions of common email combinations (like
jane.doe@domain.com) and blast them all, hoping to find active accounts.
These covert methods are precisely why personal habits are only half the battle. You need a hosted email platform that's actively fighting on your behalf.
The hard truth is your email address is likely circulating in places you'll never know about. A top-tier, privacy-focused host acts as your security detail, filtering out threats from these hidden sources before you ever see them.
Is It Better to Delete Spam or Mark It as Junk?
Always, without a doubt, mark an email as junk or spam before you even consider deleting it. This tiny action has a huge long-term impact on your email security.
Simply deleting a spam email is a missed opportunity. Sure, it gets the message out of your sight, but it does nothing to stop the sender from trying again tomorrow. It’s like sweeping dirt under the rug—the mess is still there.
When you mark an email as spam, you're actually training your email provider's filtering algorithms. You're giving them valuable data that helps them learn to spot and block similar threats in the future. This doesn't just help you; it improves the email security for every other person using that service.
Will Using an Email Alias Really Help Reduce Spam?
Yes, absolutely. Using email aliases is one of the most powerful and underrated strategies for protecting your primary inbox and email privacy. An alias is basically a disposable forwarding address that points to your main account. Think of it as a separate key you can hand out and then discard if it falls into the wrong hands.
For instance, you could create aliases like yourname.shopping@domain.com for online stores or yourname.newsletters@domain.com for subscriptions. This gives you two massive advantages:
- Isolating the Source: If an alias starts getting spammed, you know exactly which company compromised your privacy.
- Instant Control: Instead of fighting to filter the junk, you can just delete the compromised alias. The spam stops immediately, and your real email address remains completely untouched.
How Does a Privacy-Focused Email Host Stop More Spam?
It all comes down to their business model and a fundamental commitment to email security. A privacy-focused hosted email platform is designed from the ground up to protect your communications, not to monetize your data. This core difference results in tangible security benefits that drastically reduce spam.
Unlike free services that may have a financial incentive to let certain marketing emails through, a paid, secure host has only one job: to safeguard your inbox. They pour resources into advanced, multi-layered filtering systems that use real-time blacklists, enforce strict authentication (SPF, DKIM, and DMARC), and deploy machine learning to identify new threats. This unwavering commitment to email security and privacy is the real secret to stopping spam at the source.
Ready to switch to an email provider that actually puts your privacy first? With Typewire, you get advanced anti-spam protection, a strict no-tracking policy, and the peace of mind that comes with a secure, ad-free inbox. Take control of your communications and start your free trial today.