Level Up Your Inbox Defenses
Email is essential for communication, but it's vulnerable to attack. This listicle presents eight email security best practices to protect your data and minimize risk. Learn how to implement critical safeguards, from multi-factor authentication and encryption to advanced email filtering techniques like DMARC, SPF, and DKIM. Strengthen your defenses and keep your communications secure by following these essential email security best practices.
1. Multi-Factor Authentication (MFA)
Multi-Factor Authentication (MFA) is a cornerstone of email security best practices and stands as the first line of defense against unauthorized access. It's a security mechanism requiring users to provide two or more verification factors to access their email accounts. These factors typically fall into three categories: something you know (like a password), something you have (like a mobile device or security token), and something you are (like a fingerprint or facial recognition). MFA significantly reduces the risk of unauthorized access, even if your password is compromised. This added layer of security makes it drastically harder for attackers to gain entry, even if they manage to obtain your password through phishing or other malicious means.

MFA works by requiring additional verification beyond just a username and password. This could involve receiving a one-time code via SMS, using an authenticator app that generates time-based codes, utilizing a hardware token like a YubiKey, or even employing biometric verification. This layered defense mechanism ensures that even if one factor is compromised, the attacker still needs to breach another, making successful attacks far less likely. Modern email systems often offer configurable MFA strength levels based on risk profiles, allowing administrators to tailor the level of security to specific users or groups.
Features of MFA include the use of multiple forms of identification, the flexibility of various second-factor options (SMS codes, authenticator apps, hardware tokens, biometrics), and the provision of a layered defense mechanism. This makes MFA a powerful tool against a wide range of threats.
Pros:
- Dramatically reduces account takeover risks: MFA makes it exponentially harder for attackers to gain access, even with a compromised password.
- Mitigates the impact of phishing attacks: Even if a user falls victim to a phishing scam and reveals their password, MFA prevents the attacker from accessing the account.
- Relatively easy to implement: Most modern email providers offer built-in MFA options that are easy to configure.
- Highly effective: Microsoft reports a 99.9% reduction in automated attacks with MFA enabled.
Cons:
- User friction: Requiring multiple steps for login can sometimes be inconvenient for users.
- Lockout potential: Losing access to a second factor can temporarily lock legitimate users out of their accounts.
- SMS vulnerability: SMS-based MFA can be susceptible to SIM swapping attacks.
- Requires planning and education: Successful implementation necessitates careful planning, user training, and clear backup procedures.
Examples of Successful Implementation:
- Google Workspace saw a significant reduction in account takeovers after implementing mandatory 2-Step Verification.
- Microsoft reported a 99.9% reduction in account compromise rates after implementing MFA.
- Dropbox effectively eliminated successful phishing attacks by implementing Universal 2nd Factor (U2F) keys.
Tips for Implementation:
- Prioritize high-privilege accounts: Start by implementing MFA for administrators and users with access to sensitive data.
- Offer multiple second-factor options: Provide users with choices to improve user experience and accommodate different needs.
- Prioritize authenticator apps: Authenticator apps are generally more secure than SMS.
- Establish backup procedures: Ensure users have clear instructions for recovering access if they lose their second factor.
- Educate users: Explain the importance of MFA and provide real-world examples of how it protects their accounts.
Popular MFA Solutions: Google Authenticator, Microsoft Authenticator, Duo Security (Cisco), YubiKey (Yubico), and Okta.
MFA deserves its top spot in this list of email security best practices because it provides the most impactful protection against unauthorized access. In today’s threat landscape, a strong password alone is simply not enough. MFA is a crucial step towards ensuring the confidentiality and integrity of your email communications. It’s an essential security measure for everyone from privacy-conscious individuals to large organizations.
2. Email Encryption
Email encryption is a cornerstone of email security best practices, crucial for protecting sensitive information from unauthorized access. It transforms readable email content into an unreadable format, effectively disguising the message from prying eyes. This process uses sophisticated encryption algorithms and keys. Only the intended recipient, possessing the correct decryption key, can decipher and read the message. This ensures that even if intercepted during transmission, the email remains unintelligible to malicious actors.

Several methods and features facilitate email encryption. End-to-end encryption provides the highest level of security, safeguarding message content throughout its journey from the sender's device to the recipient's inbox. Transport Layer Security (TLS) encrypts emails while they are in transit between email servers, adding a layer of protection against eavesdropping. For more robust cryptographic security, options like S/MIME (Secure/Multipurpose Internet Mail Extensions) and PGP/GPG (Pretty Good Privacy/GNU Privacy Guard) are available. Modern encryption solutions can encrypt both the email body and any attached files, offering comprehensive protection. Furthermore, encryption can be transparent, happening automatically in the background, or user-initiated, giving users granular control over when to encrypt their messages.
Email encryption earns its place as a top email security best practice due to its powerful ability to protect confidential and sensitive information. This protection extends to compliance with regulatory requirements such as HIPAA (Health Insurance Portability and Accountability Act), GDPR (General Data Protection Regulation), and others, which mandate the protection of sensitive data. Encryption also effectively guards against man-in-the-middle attacks, where an attacker intercepts and potentially alters communications between two parties. Moreover, it provides verification of message integrity, assuring recipients that the message hasn't been tampered with during transmission.
Pros:
- Protects confidential and sensitive information
- Ensures compliance with regulatory requirements (HIPAA, GDPR, etc.)
- Guards against man-in-the-middle attacks
- Provides verification of message integrity
Cons:
- Can be complex to implement across organizations
- Key management can be challenging
- May require recipient to have compatible systems
- Some solutions may impact searchability of emails
- Can add complexity for end users
Examples of Successful Implementation:
- ProtonMail: Offers user-friendly end-to-end encryption for consumers.
- Virtru: Used by healthcare providers and other industries to maintain HIPAA compliance.
- Tutanota: Another popular end-to-end encrypted email provider.
- Cisco Email Security: Provides gateway-based encryption solutions for businesses.
- Financial Institutions: Commonly implement S/MIME for secure client communications.
- Government Agencies: Utilize encryption gateways like Voltage SecureMail.
Tips for Implementation:
- Start with TLS: Implement TLS encryption as a baseline minimum for all email communications.
- Automate for Sensitive Data: Consider automatic encryption for emails containing sensitive data patterns (e.g., credit card numbers, social security numbers).
- User Training: Train users on the proper handling of encryption keys and best practices for secure email communication.
- Balance Security and Usability: Choose an encryption solution that balances strong security with ease of use for your organization.
- Consider Gateway Solutions: Use gateway-based solutions for transparent encryption whenever possible to minimize user interaction.
By following these tips and understanding the different encryption options available, you can significantly enhance your email security posture and protect your valuable information.
3. Phishing Awareness Training
Phishing attacks are a persistent and evolving threat to email security best practices. These attacks exploit human vulnerability, tricking individuals into revealing sensitive information like passwords, credit card details, or internal data. Phishing awareness training is a crucial defense mechanism, educating users to identify and respond appropriately to these deceptive attempts. This training empowers employees to become the first line of defense against cyberattacks, significantly reducing the risk of successful breaches. It works by equipping individuals with the knowledge and skills to recognize suspicious emails, understand common phishing tactics (like spoofing, social engineering, and malicious links), and follow established reporting procedures when a potential threat is detected.

Phishing awareness training often incorporates interactive simulations of real-world phishing scenarios, regular testing with mock phishing emails, and metrics reporting on user susceptibility. These features allow organizations to tailor training programs based on user roles, access levels, and identified vulnerabilities. Continuous education on emerging threats is also essential, as phishing techniques constantly evolve. For example, training might cover new trends like spear-phishing (targeted attacks against specific individuals) or whaling (phishing attacks targeting high-level executives).
Successful Implementations:
Several organizations have demonstrated the effectiveness of robust phishing awareness training programs. Mastercard, for instance, reduced phishing susceptibility from 25% to under 5% through their comprehensive training. The U.S. Department of Defense also saw a dramatic reduction in successful attacks on military personnel after implementing similar training. ING, a global financial institution, uses gamified security training to engage employees and has reported measurable improvements in phishing detection rates. These examples highlight the substantial impact of well-executed training initiatives.
Actionable Tips for Implementation:
- Use Real-World Examples: Incorporate relevant examples from your organization or industry to make the training more impactful.
- Baseline Testing: Conduct testing before implementing training to identify areas of weakness and tailor the training accordingly.
- Variety in Simulations: Vary the sophistication and style of your phishing simulations to keep users on their toes and challenge their ability to recognize different attack vectors.
- Positive Reinforcement: Reward positive security behaviors rather than solely punishing failures. Acknowledge and appreciate employees who report suspicious emails.
- Short and Frequent Training: Short, frequent training sessions are more effective than long, infrequent ones. Microlearning modules can be particularly impactful.
- Customize Training: Tailor training to department-specific threats and user roles. For example, employees with access to financial systems might require more in-depth training on financial phishing scams.
Why Phishing Awareness Training Deserves Its Place on the List:
Phishing remains a primary entry point for cyberattacks, making awareness training an indispensable component of any robust email security strategy. It’s a cost-effective solution compared to the significant financial and reputational damage of a data breach. By empowering employees to identify and report phishing attempts, organizations establish a human firewall, strengthening their overall security posture.
Pros:
- Reduces successful phishing attacks significantly.
- Fosters a security-conscious culture within the organization.
- Cost-effective compared to breach remediation.
- Empowers employees to actively participate in security.
- Adaptable to specific organizational threats.
Cons:
- Requires ongoing commitment and resources.
- Effectiveness diminishes without regular reinforcement.
- Can create anxiety or resentment if poorly implemented.
- Not all users respond equally to the same training approaches.
- Maintaining high engagement levels over time can be challenging.
Popularized By: KnowBe4, Cofense (formerly PhishMe), Proofpoint Security Awareness Training, SANS Security Awareness, Wombat Security (acquired by Proofpoint).
4. Secure Email Gateway Implementation
A crucial element of any robust email security strategy, Secure Email Gateway (SEG) implementation, deserves its place among the best practices. A SEG acts as a vigilant gatekeeper, scrutinizing all incoming and outgoing email traffic to intercept threats before they infiltrate your network. This proactive approach significantly bolsters your defenses against a wide range of email-borne attacks, contributing to a more secure email environment and aligning with broader email security best practices.
How it Works:
SEGs operate by filtering email traffic based on pre-defined rules and advanced threat detection techniques. Incoming emails are scanned for malicious content such as malware, phishing URLs, and spam. Suspicious attachments are detonated in a sandboxed environment to analyze their behavior before reaching user inboxes. Outgoing emails are also inspected to prevent data leaks and ensure compliance with internal policies. This multi-layered inspection process minimizes the risk of malicious emails reaching their intended targets and sensitive data leaving the organization.
Features and Benefits:
SEGs are packed with powerful features designed to enhance email security best practices:
- Advanced Threat Protection: Combats malware, phishing, and spam using signature-based detection, heuristic analysis, and machine learning algorithms.
- URL Filtering and Sandboxing: Analyzes suspicious links and executes attachments in a safe environment to identify malicious behavior.
- Data Loss Prevention (DLP) Integration: Prevents sensitive data from leaving the organization via email.
- Content Filtering: Allows customization of filtering rules based on keywords, sender reputation, and other criteria.
- Quarantine Management: Provides a centralized location to manage suspicious emails and release legitimate messages.
These features translate into significant benefits:
- Reduced Risk: Blocks a substantial portion of malicious emails before they reach users, significantly reducing the risk of infection or compromise.
- Centralized Management: Simplifies email security administration with a single platform for policy enforcement and reporting.
- Improved Compliance: Helps organizations meet regulatory requirements for data protection and email security.
- Enhanced Productivity: Reduces the burden on end-users by filtering out spam and unwanted emails.
When and Why to Use a SEG:
Implementing a SEG is highly recommended for organizations of all sizes that prioritize email security best practices. It's particularly crucial for businesses handling sensitive data, operating in regulated industries, or facing frequent email-borne threats.
Pros and Cons:
While SEGs offer robust protection, it's essential to weigh the pros and cons:
Pros:
- Blocks a high percentage of malicious emails.
- Reduces burden on end-user security awareness.
- Provides centralized email security management.
- Offers detailed threat intelligence and reporting.
- Can enforce regulatory compliance requirements.
- Scalable for organizations of all sizes.
Cons:
- Significant implementation and maintenance costs.
- Potential for false positives (blocking legitimate emails).
- Requires skilled personnel for optimal configuration and maintenance.
- Cannot guarantee 100% protection against sophisticated phishing attacks.
- Can introduce latency to email delivery.
Examples of Successful Implementation:
- A global financial services firm implemented Cisco's SEG and reduced malware incidents by 95%.
- A healthcare provider using Proofpoint's solution blocked over 2.5 million malicious emails in one year.
- A manufacturing company using Mimecast prevented a Business Email Compromise (BEC) attack that could have resulted in a $4.7M wire fraud.
Actionable Tips for Implementation:
- Regularly update SEG rules and signatures: Ensure your SEG stays ahead of evolving threats.
- Implement both inbound and outbound filtering: Protect against both incoming threats and outgoing data leaks.
- Configure granular policies: Tailor policies based on user groups and data sensitivity.
- Enable URL rewriting: Protect against delayed URL exploitation.
- Establish clear quarantine review procedures: Ensure legitimate emails are released promptly.
- Integrate with other security tools: Create a comprehensive security ecosystem for holistic protection.
Popular SEG Providers:
- Proofpoint
- Mimecast
- Cisco Secure Email
- Barracuda Email Protection
- Trend Micro Email Security
- FortiMail (Fortinet)
By implementing a SEG and adhering to these email security best practices, organizations can significantly strengthen their defenses against the ever-evolving landscape of email-borne threats. A SEG provides an essential layer of protection, ensuring business continuity, safeguarding sensitive data, and promoting user trust.
5. DMARC, SPF, and DKIM Implementation
Implementing DMARC, SPF, and DKIM is a crucial email security best practice that significantly bolsters your defenses against spoofing and phishing attacks. These three email authentication protocols work together to verify the legitimacy of emails sent from your domain, ensuring that only authorized senders are reaching your recipients' inboxes. This drastically reduces the risk of business email compromise and protects your brand reputation. This layered approach to authentication confirms that emails genuinely originate from your domain and haven't been tampered with during transit.
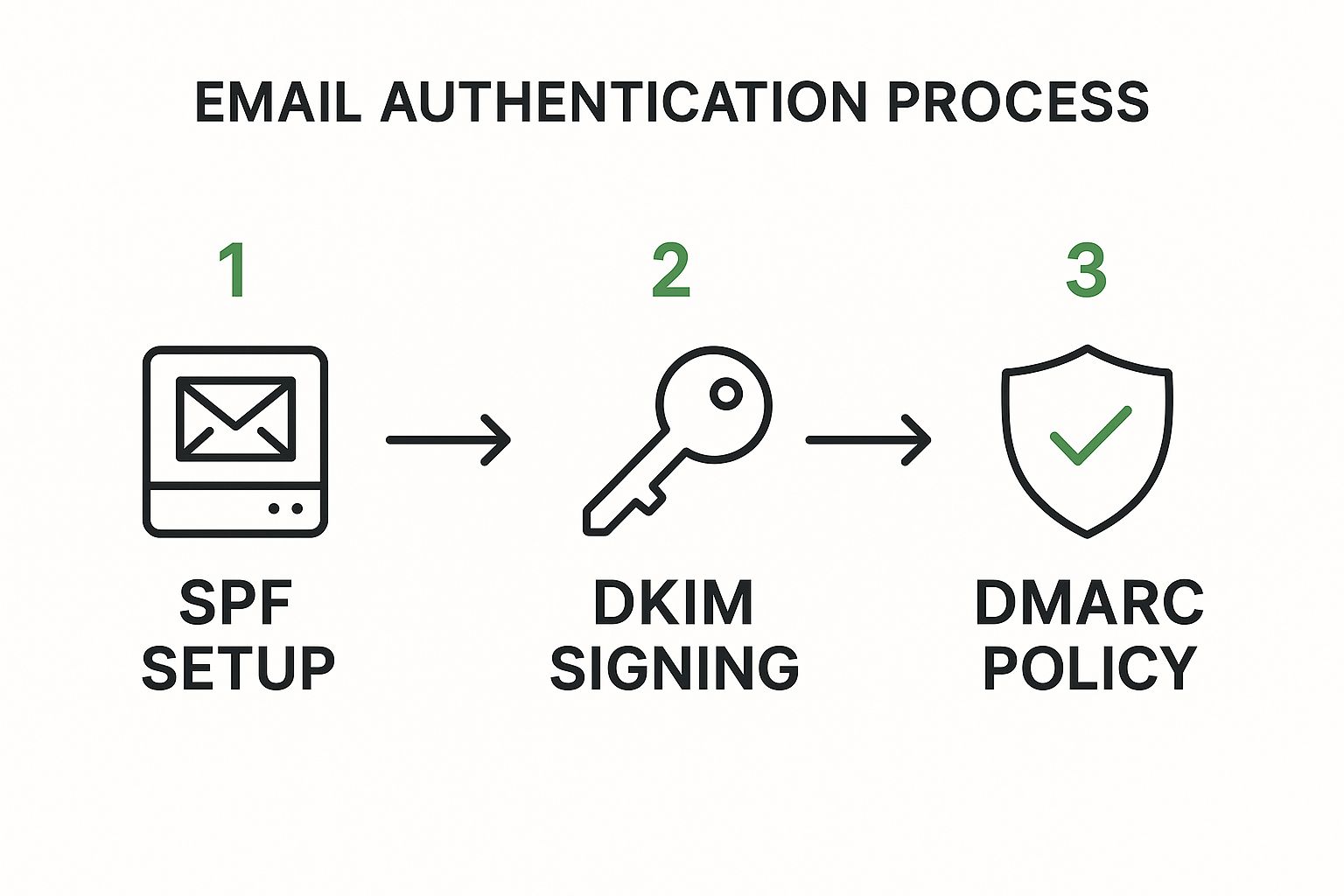
The infographic illustrates the process flow of an email being checked against SPF, DKIM, and finally DMARC. The process begins with an email being sent from a purported sender from your domain. The receiving mail server then checks the SPF record to verify if the sending server is authorized to send emails on behalf of your domain. Next, the DKIM signature is verified to ensure the message integrity hasn't been compromised. Finally, DMARC evaluates the results of both SPF and DKIM checks against your pre-defined policy (none, quarantine, or reject) to determine how the email should be handled. The sequence is crucial as DMARC relies on the results of SPF and DKIM to make its final decision.
As the infographic demonstrates, implementing these protocols provides a robust framework for verifying email authenticity and protecting against fraudulent emails.
Here's how these protocols work individually:
- SPF (Sender Policy Framework): SPF publishes a list of authorized mail servers that are permitted to send emails on behalf of your domain. This helps prevent attackers from forging your domain in the "from" address.
- DKIM (DomainKeys Identified Mail): DKIM adds a digital signature to your outgoing emails, verifying that the message content hasn't been altered during transit. This signature is verified by the recipient's mail server.
- DMARC (Domain-based Message Authentication, Reporting, and Conformance): DMARC builds upon SPF and DKIM by providing instructions to receiving mail servers on how to handle emails that fail authentication checks. You can specify policies ranging from "none" (monitoring only) to "quarantine" (move to spam folder) or "reject" (block the email entirely). DMARC also provides valuable reporting data on email authentication results, giving you insights into potential issues and spoofing attempts.
Benefits of implementing DMARC, SPF, and DKIM:
- Significantly reduces domain spoofing attacks: By verifying the sender's legitimacy, these protocols make it much harder for attackers to impersonate your domain.
- Improves email deliverability and sender reputation: Authenticated emails are less likely to be flagged as spam, improving your inbox placement rates.
- Provides visibility into email authentication failures: DMARC reports offer valuable data on authentication issues, allowing you to identify and address potential vulnerabilities.
- Relatively low cost to implement compared to the benefits: Setting up these protocols requires some technical expertise but is generally cost-effective compared to the potential damage of a successful spoofing attack.
Challenges and Considerations:
- Complex initial setup, especially for large organizations: Configuring these protocols can be complex, particularly if you have numerous subdomains or complex email infrastructure.
- Requires careful planning to avoid disrupting legitimate email flow: Incorrectly configured policies can inadvertently block legitimate emails, so thorough planning and testing are essential.
- Full implementation typically takes months: Gradually tightening DMARC policies over time is recommended to avoid disrupting legitimate email.
Actionable Tips for Implementation:
- Start with monitoring mode (p=none): Begin by monitoring DMARC reports without enforcing any policies. This allows you to identify all legitimate email senders before implementing stricter policies.
- Identify all legitimate email senders: Before enforcing DMARC, compile a comprehensive list of all services and systems sending emails on your behalf.
- Use third-party tools to analyze DMARC reports: Several tools can help you interpret DMARC reports and identify authentication issues.
- Implement SPF and DKIM before DMARC: These are prerequisites for DMARC and should be configured correctly before implementing DMARC.
- Gradually move from p=none to p=quarantine to p=reject: Incrementally tightening your DMARC policy minimizes the risk of disrupting legitimate email flow.
- Pay special attention to third-party services sending email on your behalf: Ensure that any third-party services using your domain for email are properly authenticated.
Examples of Successful Implementation:
Organizations like PayPal, the U.S. Federal government, and major financial institutions have seen dramatic reductions in spoofing attacks and phishing attempts after implementing DMARC, demonstrating its effectiveness. PayPal reported a 70% reduction in fraudulent emails, while the U.S. Federal government achieved an 80% reduction in spoofing attempts.
Implementing DMARC, SPF, and DKIM is a vital email security best practice for any organization or individual concerned about protecting themselves and their users from email spoofing and phishing attacks. It is a cornerstone of modern email security and a worthwhile investment for any organization looking to enhance their email security posture.
6. Regular Security Patching and Updates
Maintaining robust email security requires a proactive approach, and one of the most fundamental email security best practices is regular security patching and updates. This crucial process involves systematically applying the latest security fixes to all components of your email infrastructure, including email servers, client applications, operating systems, and even security tools themselves. By diligently patching known vulnerabilities, you significantly reduce the attack surface available to malicious actors, protecting your sensitive data and ensuring the integrity of your communications.
How Patching Bolsters Email Security:
Think of security patches as digital bandages for software flaws. Cybercriminals are constantly searching for vulnerabilities in widely used software, including email platforms. When they discover a weakness, they can exploit it to gain unauthorized access, steal data, or disrupt services. Security patches address these vulnerabilities, closing the loopholes before they can be exploited. A comprehensive patch management program systematically identifies, tests, and deploys these patches, ensuring that your systems remain resilient against emerging threats. This includes not only software updates but also firmware updates for hardware components related to your email infrastructure.
Real-World Examples of Patching Success (and Failure):
The importance of patching is underscored by several high-profile incidents. The devastating WannaCry ransomware attack of 2017 exploited a vulnerability in Windows systems. Organizations that had applied the available patch were largely protected, while those that hadn't suffered significant disruptions and data loss. More recently, the Microsoft Exchange ProxyLogon vulnerabilities in 2021 demonstrated the severe consequences of delayed patching. Thousands of email servers belonging to organizations that hadn't promptly patched were compromised. Conversely, a major healthcare provider successfully avoided a significant ransomware outbreak by implementing a strict 24-hour critical patch policy, showcasing the value of proactive patching.
Actionable Tips for Effective Patch Management:
Implementing a successful patch management program requires planning and diligence. Here are some essential tips:
- Establish a Clear Policy: Create a formal patch management policy with defined Service Level Agreements (SLAs) based on vulnerability severity. Critical vulnerabilities should be addressed immediately, while less critical ones can be scheduled.
- Test Before Deploying: Always test patches in a non-production environment before rolling them out to live systems. This allows you to identify any potential compatibility issues or unexpected behavior.
- Automate Where Possible: Utilize automated patch management tools to streamline the process, particularly in larger environments. Tools like IBM BigFix (HCL BigFix), Qualys Patch Management, and Ivanti Patch Management can help automate patch deployment and reporting.
- Maintain an Accurate Inventory: Keep a detailed inventory of all systems requiring updates, including operating systems, email clients, servers, and security software. This ensures that no system is overlooked.
- Prioritize Based on Risk: Implement a risk-based approach for prioritizing patches. Consider the severity of the vulnerability, the potential impact on your organization, and the likelihood of exploitation. Resources like the CISA Known Exploited Vulnerabilities Catalog can help inform your prioritization.
- Emergency Procedures: Develop emergency patching procedures for critical vulnerabilities that require immediate action. This might involve after-hours patching or expedited testing protocols.
- Regular Audits: Conduct regular audits to ensure patch compliance and identify any systems that may have fallen behind on updates.
Pros and Cons of Regular Patching:
While the benefits of patching are undeniable, it's essential to be aware of the potential downsides:
Pros:
- Closes known security vulnerabilities, minimizing the risk of exploitation.
- Reduces the window of opportunity for attackers.
- Often includes performance improvements alongside security fixes.
- Demonstrates compliance with security best practices.
- Relatively low cost compared to the expense of breach remediation.
Cons:
- Can occasionally introduce new problems or compatibility issues (hence the importance of testing).
- Requires maintenance windows that may briefly impact system availability.
- Resource-intensive to test and deploy across large environments.
- Requires careful planning and potentially emergency procedures.
- Legacy systems may not have available patches, necessitating alternative mitigation strategies.
Why Patching is Essential for Email Security Best Practices:
Regular security patching and updates are a non-negotiable element of any robust email security strategy. By proactively addressing vulnerabilities, you strengthen your defenses, reduce the risk of breaches, and protect the confidentiality, integrity, and availability of your email communications. This practice is so fundamental that initiatives like Microsoft's "Patch Tuesday" have become cornerstones of the IT security landscape, highlighting the ongoing need for vigilance and proactive patching. Including this practice in your overall security posture is not just recommended – it’s essential for protecting your organization from ever-evolving cyber threats.
7. Principle of Least Privilege for Email Access
The Principle of Least Privilege (PoLP) is a crucial email security best practice that significantly strengthens your defense against cyber threats. It operates on the premise that every user should have access only to the email resources and functionalities absolutely necessary for their job role. By limiting access to the bare minimum, PoLP minimizes the potential damage from compromised accounts, insider threats, and data breaches. This approach is critical for any organization striving to enhance its email security posture.
How it Works:
PoLP for email access involves configuring granular permissions for each user account. Instead of granting blanket access to all email features, administrators carefully assess each individual's job responsibilities and grant permissions accordingly. This might mean restricting access to shared mailboxes, limiting the ability to send emails on behalf of others, controlling access to mail flow rules, and tightly managing administrative privileges. Role-based access controls (RBAC) can simplify this process by grouping users with similar job functions and assigning predefined permission sets.
Features that Support PoLP:
- Granular permission settings for email accounts: Allowing administrators to fine-tune access to specific mailboxes, folders, and functionalities.
- Role-based access controls (RBAC) for administrative functions: Simplifying permission management by assigning predefined roles with specific privileges.
- Regular access reviews and privilege auditing: Ensuring that permissions remain relevant and identifying any unnecessary access.
- Separation of duties for sensitive email operations: Preventing any single user from having excessive control over critical email processes.
- Just-in-time access for administrative tasks: Granting elevated privileges only when needed and revoking them immediately afterward.
Why Implement PoLP for Email Access?
This method deserves a place in any email security best practices list because it directly addresses several key vulnerabilities:
- Minimizes the impact of compromised accounts: If an attacker gains access to a user account with limited privileges, the potential damage is significantly reduced.
- Reduces the risk of insider threats: Restricting access to sensitive information minimizes the possibility of malicious or accidental data leaks by internal actors.
- Simplifies compliance with regulatory requirements: PoLP helps organizations meet data protection regulations by demonstrating a strong security posture.
- Makes unauthorized activities easier to detect: Limited access makes it easier to identify suspicious activity and pinpoint potential threats.
- Limits the scope of potential data breaches: Containing a breach to a smaller subset of data by limiting access to only what's necessary.
Pros and Cons:
- Pros: Enhanced security, reduced risk of breaches, improved compliance, simplified threat detection.
- Cons: Potential workflow friction if implemented too restrictively, increased administrative overhead, possible rise of shadow IT if users feel unduly constrained. These cons can be mitigated through careful planning, thorough documentation, and regular review of access privileges.
Examples of Successful Implementation:
- A manufacturing company implemented delegate access reviews and discovered 23% of permissions were no longer needed, significantly reducing their attack surface.
- A financial institution implemented just-in-time privileged access, reducing exposure of admin credentials by 85% and bolstering their security against credential theft.
- A technology company using a tiered admin model contained a breach to only 3 accounts instead of the entire domain, demonstrating the power of PoLP in limiting damage.
Actionable Tips for Implementing PoLP:
- Start with a thorough audit of current email permissions: Identify and remove any unnecessary access.
- Document clear approval processes for privilege escalation: Ensure that any requests for elevated privileges are properly vetted.
- Implement time-bound elevated permissions for special tasks: Grant temporary access for specific projects and automatically revoke it upon completion.
- Use groups rather than individual permissions where possible: Simplify management and ensure consistent application of policies.
- Conduct quarterly access reviews with department managers: Verify that permissions align with current job responsibilities.
- Consider Privileged Access Management (PAM) solutions: Automate and streamline the management of administrative accounts.
- Implement automatic revocation of access when employees change roles or leave the organization: Prevent lingering access that could be exploited.
By following these best practices and diligently implementing PoLP, organizations can significantly strengthen their email security and protect sensitive data from a wide range of threats. Solutions like Microsoft Entra ID Privileged Identity Management, CyberArk Privileged Access Management, and BeyondTrust, alongside guidance from NIST Special Publication 800-53 and Center for Internet Security (CIS) Controls, provide frameworks and tools for effectively managing privileged access within email systems.
8. Comprehensive Email Backup and Recovery
Email is a mission-critical communication tool for individuals and businesses alike. Losing access to your emails, whether due to accidental deletion, a system crash, a migration gone wrong, or a malicious attack, can have devastating consequences. This is where comprehensive email backup and recovery, a vital component of email security best practices, comes into play.
Comprehensive email backup and recovery involves systematically creating, storing, and maintaining copies of your email data. This encompasses emails themselves, attachments, and crucial metadata. This practice is essential for ensuring business continuity and compliance, allowing you to restore your valuable data when primary systems fail or are compromised. Modern email backup strategies are designed to address the evolving threat landscape, incorporating features like immutability (preventing backups from being altered or deleted, even by ransomware), versioning, and rapid recovery capabilities.
This approach goes beyond simply archiving old emails. It's about creating a robust system that allows you to restore your email environment to a specific point in time, minimizing disruption and data loss. When considering email backup and recovery, it's also crucial to maintain the integrity and professionalism in email drafts to ensure that restored emails adhere to company standards and best practices. This resource offers valuable insights into crafting professional email communications.
Features of a Robust Email Backup Solution:
- Automated, scheduled backups: Eliminates the risk of human error and ensures consistent backups.
- Point-in-time recovery: Enables restoration to a specific moment, minimizing data loss.
- Immutable storage: Protects backups from ransomware and other malicious alterations.
- Granular recovery options: Restore individual emails, folders, or entire mailboxes as needed.
- Offline/air-gapped backup copies: Provides an extra layer of security against online threats.
- Encryption of backup data: Safeguards sensitive information both in transit and at rest.
- Regular testing of restoration procedures: Verifies the reliability of your backup system.
Why Implement Comprehensive Email Backup and Recovery?
The benefits are numerous and impactful:
- Protection against data loss: Safeguards your email data from accidental deletion, corruption, hardware failures, and software glitches.
- Ransomware remediation: Allows you to recover your email data without paying a ransom.
- Support for legal hold and compliance requirements: Ensures you can meet regulatory obligations for data retention.
- Business continuity during primary system outages: Minimizes downtime and maintains communication flow.
- Facilitates migration between email platforms: Simplifies the process of switching email providers.
- Historical data access for investigations: Provides access to past email communications for audits or legal discovery.
Pros and Cons:
While the benefits are substantial, it's important to be aware of the potential drawbacks:
Pros: See "Why Implement Comprehensive Email Backup and Recovery?" above.
Cons:
- Storage resources: Can require significant storage space, especially for large organizations.
- Cost: Enterprise-grade solutions can be expensive.
- Compliance challenges: Data sovereignty regulations may impact where backups can be stored.
- Recovery time: Restoring large datasets can be time-consuming.
- Maintenance: Requires regular testing and validation to ensure reliability.
Examples of Successful Implementations:
- A law firm recovered seven years of critical client communications after a ransomware attack by utilizing immutable backups.
- A university restored 10,000 student mailboxes within 24 hours following a cloud service disruption.
- A manufacturing company avoided paying a $2 million ransom by restoring its email systems from offline backups.
Actionable Tips for Implementing Email Backup and Recovery:
- Follow the 3-2-1 backup rule: Maintain 3 copies of your data on 2 different media types, with 1 copy stored offsite.
- Implement retention policies: Align your data retention policies with legal and compliance requirements.
- Regularly test recovery procedures: Conduct tests with realistic scenarios to ensure your system works as expected.
- Encrypt backup data: Protect your backups with strong encryption both in transit and at rest.
- Air-gapped backups: Ensure some backups are completely disconnected from your production networks.
- Document and practice the full recovery process: Develop a clear recovery plan and practice it regularly.
- Consider purpose-built backup solutions: Evaluate and select a backup solution specifically designed for your email platform.
Popular Solutions: Veeam Backup for Microsoft 365, Barracuda Email Backup, Druva inSync, Commvault, and AvePoint Cloud Backup are among the popular solutions available.
Comprehensive email backup and recovery is not a luxury but a necessity in today's digital landscape. By implementing a robust backup strategy, you can protect your valuable email data, ensure business continuity, and maintain peace of mind. This is a critical element of any comprehensive email security best practices plan.
8 Key Email Security Practices Comparison
| Practice | 🔄 Implementation Complexity | 🔧 Resource Requirements | 📊 Expected Outcomes | 🎯 Ideal Use Cases | ⭐ Key Advantages |
|---|---|---|---|---|---|
| Multi-Factor Authentication (MFA) | Medium (configuration & user education) | Moderate (authenticator apps, tokens) | Dramatic reduction in unauthorized access | Protecting high-privilege accounts | Layered defense, mitigates phishing, high effectiveness (⭐) |
| Email Encryption | High (key management & user compatibility) | High (encryption tools, training) | Strong confidentiality & regulatory compliance | Sensitive data protection & compliance | End-to-end security, guards against MITM, message integrity (⭐) |
| Phishing Awareness Training | Medium (ongoing training & simulations) | Moderate (training platforms, time) | Up to 75% reduction in phishing success (📊) | Human risk reduction & security culture | Cost-effective, builds user awareness, adaptable |
| Secure Email Gateway Implementation | High (complex setup & maintenance) | High (specialized hardware/software & expertise) | Blocks majority of malicious emails (📊) | Enterprise email threat filtering | Centralized control, advanced threat detection, scalable |
| DMARC, SPF, DKIM Implementation | Medium-High (technical DNS & email config) | Low-Moderate (DNS setup & monitoring) | Significant reduction in domain spoofing (📊) | Domains vulnerable to spoofing & phishing | Improves deliverability, low cost, visibility into failures |
| Regular Security Patching & Updates | Medium (process & automation needed) | Moderate (tools, testing environments) | Reduced vulnerability window, improved security | Maintaining secure email infrastructure | Closes known vulnerabilities, compliance support (⭐) |
| Principle of Least Privilege (PoLP) | Medium (detailed permissions audit) | Moderate (management & audits) | Limits damage from compromised accounts | Organizations needing strict access control | Minimizes insider risks, simplifies compliance |
| Comprehensive Email Backup & Recovery | Medium-High (storage & processes) | High (storage, backup software, testing) | Business continuity & data loss prevention (📊) | Data retention, ransomware recovery | Immutable backups, granular recovery, compliance support |
Secure Your Communications, Secure Your Future
Implementing robust email security best practices is no longer a luxury but a necessity in today's digital landscape. From enabling multi-factor authentication (MFA) and understanding email encryption to recognizing phishing attempts and implementing a secure email gateway, each step you take strengthens your defense against cyber threats. Regularly patching systems, employing the principle of least privilege, and ensuring comprehensive email backup and recovery further solidify your security posture. Mastering these email security best practices is crucial for individuals and businesses alike, protecting sensitive data, preserving privacy, and ensuring business continuity. Ignoring these vital measures can lead to significant financial losses, reputational damage, and legal repercussions.
The most important takeaway is that email security is an ongoing commitment. The threat landscape is constantly evolving, and your security measures must adapt in tandem. By consistently applying these best practices, you're not just protecting your inbox; you're safeguarding your future.
Ready to take control of your email security and experience the peace of mind that comes with robust protection? Typewire offers secure and private email hosting with built-in security features aligned with these email security best practices, making implementation easier than ever. Explore how Typewire can elevate your email security at Typewire and experience the difference a truly secure communication platform can make.

