Reclaim Your Inbox: Stop the Flood of Unwanted Emails
Drowning in unwanted emails? This listicle provides seven practical strategies to stop unwanted emails and reclaim control of your inbox. Learn how to implement techniques like unsubscribe links, filtering rules, and email address aliasing to minimize spam and focus on important messages. These skills are crucial for effective email management in 2025, protecting your privacy and boosting productivity. From simple unsubscribes to advanced email compartmentalization, this guide offers solutions for everyone looking to stop unwanted emails.
1. Unsubscribe Using Built-in Links
One of the most straightforward methods to stop unwanted emails is to utilize the built-in unsubscribe links found in most legitimate marketing emails. This strategy involves systematically identifying and clicking these links, effectively removing yourself from mailing lists you no longer wish to receive communications from. This approach leverages existing mechanisms within email marketing best practices and legal requirements to manage your subscriptions.
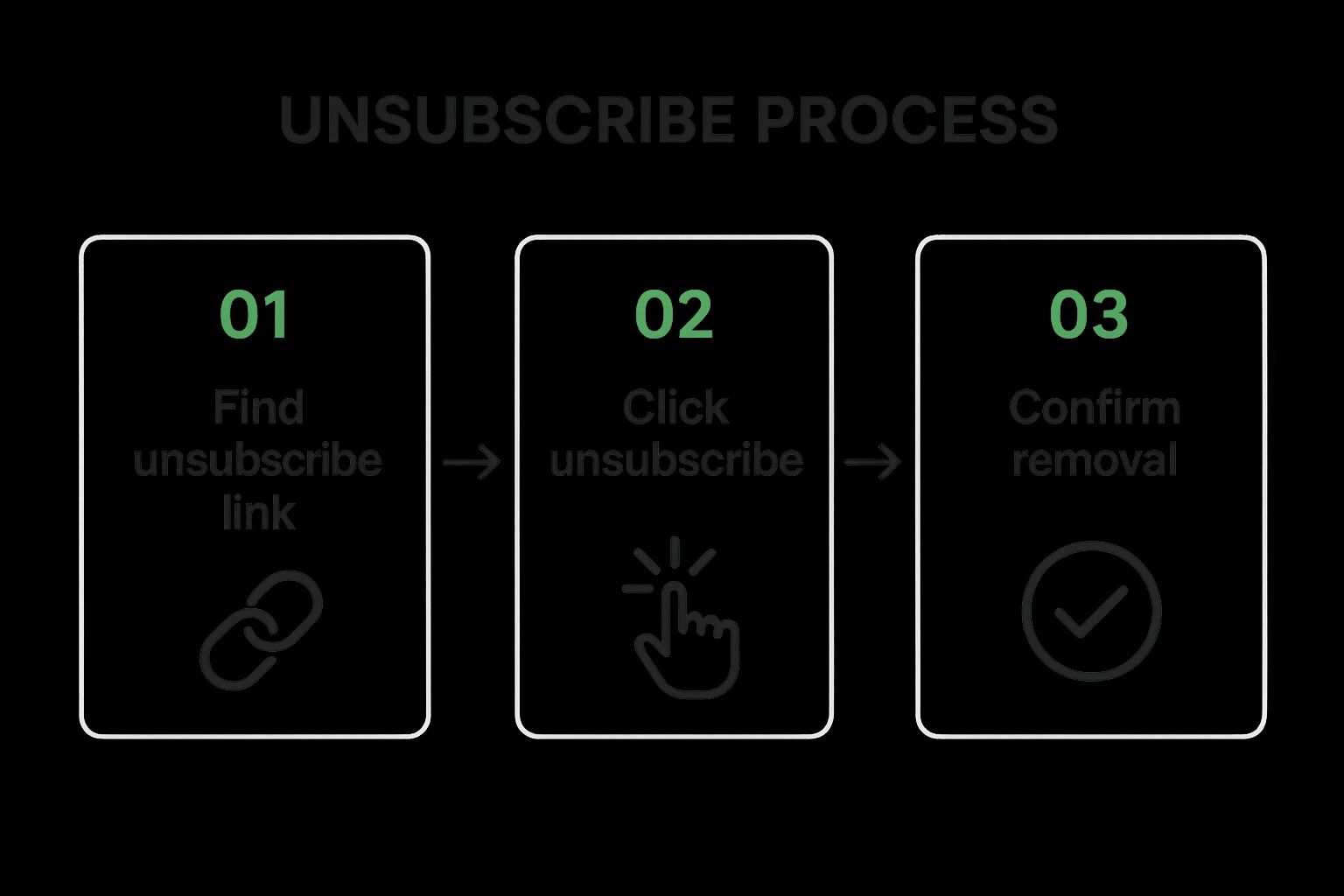
The infographic above visualizes the typical unsubscribe process. It starts with identifying the unsubscribe link, often located in the email footer. Clicking this link usually leads to a confirmation page where you may need to verify your request, sometimes by clicking another button or selecting a reason for unsubscribing. In some cases, the unsubscribe process might involve logging into your account with the sender or managing your preferences within a dedicated portal.
This simple process, typically requiring just one or two clicks, is a legal requirement in many jurisdictions, including the CAN-SPAM Act in the US and GDPR in the EU. This ensures businesses provide a clear and accessible way for recipients to opt out of their marketing communications. Furthermore, many legitimate senders offer options to adjust your email frequency or customize the types of emails you receive, providing more control over your inbox without completely unsubscribing.
This method deserves its place on this list due to its simplicity, legality, and effectiveness for managing legitimate subscriptions. It's a readily available tool that requires no specialized software or technical expertise.
Features and Benefits:
- Usually requires only 1-2 clicks
- Legally required in many jurisdictions (CAN-SPAM Act in US, GDPR in EU)
- Often includes options to adjust email frequency rather than completely unsubscribing
- Permanent solution for legitimate senders
Pros:
- Legal and straightforward approach
- Works well for legitimate business communications
- No specialized tools required
Cons:
- May not work for spam emails (can actually confirm your address is active)
- Process can be time-consuming if dealing with many emails
- Some unsubscribe processes require multiple steps or login
- May take up to 10 business days to take effect under CAN-SPAM Act
Examples:
- Gmail's automatic unsubscribe button that appears at the top of some promotional emails provides a convenient one-click solution.
- Reputable companies like Amazon and Netflix typically offer clear and easy-to-use unsubscribe links.
- Many organizations have email preference centers that allow you to customize what types of emails you receive, offering greater control over your subscriptions.
Tips for Stopping Unwanted Emails Using Unsubscribe Links:
- Check the Footer: Always look for an unsubscribe link at the bottom of emails before deleting them.
- Be Patient: If unsubscribing doesn't work after 10 business days, consider reporting the sender to your email provider or the relevant authorities.
- Customize Preferences: Consider using 'update preferences' options to reduce email frequency rather than unsubscribing completely if you still want to receive some communications.
- Avoid Spam Links: Never click unsubscribe links in obvious spam emails, as this can confirm your email address is active and lead to more unwanted messages.
Using unsubscribe links is a crucial first step in taking control of your inbox and stopping unwanted emails. While this method effectively manages legitimate subscriptions, it's essential to be aware of its limitations and exercise caution when dealing with potential spam. This approach is particularly beneficial for privacy-conscious individuals, business owners, IT professionals, and anyone overwhelmed by unwanted email, offering a simple, legal, and effective way to manage subscriptions and reduce clutter.
2. Email Filtering Rules
Tired of sifting through countless unwanted emails to find the important ones? Email filtering rules offer a powerful, proactive solution to stop unwanted emails and reclaim control of your inbox. This method involves setting up customized filters within your email client to automatically sort, categorize, or even delete unwanted emails based on specific criteria. These rules act as gatekeepers, processing incoming messages before they reach your inbox and taking action according to your predefined instructions. This makes filtering a crucial tool for anyone serious about managing their email effectively and stopping unwanted emails before they become a distraction.
The power of email filtering lies in its flexibility. You can create rules based on a multitude of criteria, including the sender's address, keywords in the subject line, or even specific content patterns within the email body. For example, you could create a filter that automatically moves all newsletters from a particular sender to a designated "Newsletters" folder, or one that deletes any email with "Free Offer" in the subject line. These rules can also be combined with labels or tags for even better organization. Most major email clients, such as Gmail, Outlook, and Apple Mail, offer robust filtering capabilities, allowing you to tailor your inbox management to your specific needs.
Email filtering is highly beneficial for several reasons. It offers a proactive approach, preventing unwanted emails from cluttering your inbox in the first place. This high level of customization allows you to finely tune your filters to match your individual priorities. Critically, it works even with senders who persistently ignore unsubscribe requests. Once set up, these filters continuously work in the background, providing ongoing benefits with minimal maintenance.
However, setting up effective filtering rules requires an initial time investment to configure them correctly. There's also the risk of accidentally filtering out wanted emails (false positives), especially when using complex rules. Furthermore, filters may require periodic maintenance and updating as spammers change their tactics. Advanced filtering may also necessitate learning the specifics of your email client's rule system.
Examples of Successful Implementation:
- Gmail's filters: Gmail allows you to create filters directly from search results, making it easy to target specific senders or keywords.
- Outlook's Rules Wizard: Outlook provides a powerful Rules Wizard that allows for complex conditional filtering based on multiple criteria.
- Apple Mail's rules: Apple Mail's rules system allows for efficient routing of messages to designated folders.
Actionable Tips for Stopping Unwanted Emails with Filters:
- Start simple: Begin with basic rules based on sender or subject and gradually increase complexity as needed.
- Test your filters: Before applying a new filter to your incoming mail, test it on existing emails to ensure it works as intended and avoid false positives.
- Create a "Possibly Important" folder: Instead of immediately deleting filtered emails, route them to a separate folder so you can review them periodically for anything important that might have been mistakenly filtered.
- Use common spam keywords: Incorporate keywords commonly found in spam email subjects (e.g., "free," "urgent," "limited time offer") to create effective spam filters.
- Regular review: Periodically review your filtered messages and refine your rules as necessary to maintain their effectiveness.
Email filtering rules deserve a prominent place on this list because they offer a proactive, customizable, and highly effective solution to stop unwanted emails. They empower users to take control of their inbox and minimize distractions, making email management significantly more efficient. Features like the ability to combine rules with labels and tags further enhance organization, making it easier than ever to find the information you need quickly. This method is particularly beneficial for busy professionals, privacy-conscious individuals, and anyone overwhelmed by the sheer volume of email they receive. By investing a little time upfront to configure effective filtering rules, you can save countless hours in the long run and enjoy a cleaner, more organized inbox.
3. Third-Party Email Management Services
Drowning in unwanted emails? If unsubscribing one-by-one feels like an uphill battle, third-party email management services offer a powerful arsenal to help you reclaim your inbox and stop unwanted emails. These dedicated services go beyond the basic filtering capabilities of standard email clients, providing automated tools to identify subscriptions, offer bulk unsubscribe options, and give you granular control over your incoming mail.
These services work by connecting to your email account (after your explicit permission, of course) and analyzing your inbox. They intelligently categorize emails, identify recurring subscriptions you might have forgotten about, and offer a streamlined way to unsubscribe from multiple senders at once. Many also provide advanced filtering rules and email digests, condensing less important messages into summaries so you can focus on what truly matters.
For example, Unroll.me provides a visual dashboard of all your subscriptions, allowing you to unsubscribe with a single click. Clean Email goes a step further, enabling you to create complex rules to block unwanted senders and manage entire email lists. SaneBox specializes in smart filtering, automatically prioritizing important emails and moving less critical messages to a separate folder.
Features and Benefits:
- Batch unsubscribe capabilities: Say goodbye to tedious individual unsubscribes. These services let you unsubscribe from multiple senders simultaneously, significantly reducing inbox clutter.
- Visual dashboard of email subscriptions: Gain a clear overview of all your active subscriptions, making it easier to identify and manage them.
- AI-powered categorization of emails: Intelligent algorithms categorize your emails, helping you quickly find what you're looking for and filter out noise.
- Integration with major email providers: Most services seamlessly integrate with popular email platforms like Gmail, Outlook, and Yahoo.
- Email digests and summaries: Condense less important messages into digestible summaries, saving you time and minimizing distractions. This can be particularly helpful if your business relies heavily on Microsoft Teams for internal communication, and you can streamline your workflow by using Microsoft Teams for customer support.
Pros:
- Significantly more powerful than built-in email tools: Offers advanced features that standard email clients lack.
- Can identify subscriptions you didn't realize you had: Helps you uncover and unsubscribe from forgotten subscriptions.
- Saves time through automation and batch processing: Streamlines email management and reduces manual effort.
- Often includes analytics on email patterns: Provides insights into your email habits and helps you identify areas for improvement.
Cons:
- Many services require access to your email account: This raises privacy concerns for some users.
- Premium features usually require subscription fees: While some basic features are free, advanced functionality often comes at a cost.
- Privacy concerns with third-party email access: Carefully research the privacy policy before granting any service access to your inbox.
- May not work with all email providers: Compatibility can vary, so ensure the service supports your email platform.
Tips for Choosing an Email Management Service:
- Research the privacy policy before granting access to your inbox: Ensure you understand how the service handles your data.
- Start with a free tier to test effectiveness before subscribing: This allows you to evaluate the features and determine if it meets your needs.
- Look for services that offer both unsubscribing and filtering: A combination of these features provides comprehensive inbox control.
- Consider services that work across multiple email accounts: This is particularly useful if you manage multiple email addresses.
Popular Services: Unroll.me, Clean Email, SaneBox, Cleanfox
By leveraging the power of third-party email management services, you can take control of your inbox, stop unwanted emails effectively, and reclaim valuable time. Remember to weigh the pros and cons and choose a service that aligns with your privacy preferences and email management needs.
4. Email Address Aliasing
Email address aliasing is a powerful technique to stop unwanted emails and regain control over your inbox. It involves creating unique, disposable email addresses that forward to your main email account. Instead of giving out your primary email address every time you sign up for a newsletter, online service, or make an online purchase, you use a unique alias. This allows you to effectively compartmentalize your online activities and easily pinpoint the source of unwanted emails. This method lets you enjoy the convenience of receiving all your emails in one central inbox while significantly improving your online privacy and security.

This approach deserves a place on this list because it offers a proactive solution to stop unwanted emails before they even reach your inbox. Rather than reacting to spam after the fact, you're preemptively blocking its potential sources. It provides a level of granular control over your inbox that traditional methods like unsubscribing or spam filters simply can't match.
Here's how it works: an alias acts like a forwarding address. When an email is sent to an alias, it's automatically redirected to your primary inbox. You still receive the message, but the sender only sees the alias, not your real email address.
Features and Benefits:
- Unique Identifiable Addresses: Create distinct aliases for each service (e.g.,
youremail+amazon@gmail.com,youremail+netflix@gmail.com). This instantly reveals which service is responsible for unwanted emails or data breaches. - Centralized Inbox: All emails from your various aliases still arrive in your main inbox for easy access.
- Selective Blocking: Disable specific aliases without affecting others. If one alias starts receiving spam, simply turn it off to stop the influx of unwanted emails without disrupting other services.
- Enhanced Privacy: Masks your real email address, reducing your digital footprint and protecting your privacy.
Pros:
- Easy Identification of Leaks: Instantly identify which company sold or shared your email when spam arrives at a specific alias.
- Granular Control: Block specific services by disabling their associated alias.
- Improved Security: Compartmentalizing online accounts limits the impact of data breaches. If one alias is compromised, your main email and other aliases remain safe.
- Reduced Spam: Significantly reduce the amount of spam reaching your primary inbox.
Cons:
- Potential Cost: Advanced aliasing services like SimpleLogin and AnonAddy may require a paid subscription for full functionality.
- Domain Blocking: Some websites block known disposable email domains, making alias creation impossible.
- Management Overhead: Managing multiple aliases can become complex without proper organization.
- Limited Native Support: Not all email providers offer built-in aliasing capabilities.
Examples:
- Apple's Hide My Email: Creates random, unique email addresses that forward to your iCloud account.
- Firefox Relay: Provides masked email addresses to protect your real email.
- Gmail's Plus Addressing: Allows creating aliases by adding a "+" and a suffix to your Gmail address (e.g.,
youremail+service@gmail.com). - SimpleLogin/AnonAddy: Offer advanced alias management features, including custom domains and detailed control.
Tips for Using Email Aliases:
- Descriptive Suffixes: Use descriptive suffixes to easily identify the service associated with each alias (e.g.,
email+amazon@gmail.com). - Keep Records: Maintain a list of which alias is used with which service.
- Test Aliases: Test your aliases before using them for important accounts to ensure they function correctly.
- Consider Premium Options: For sensitive accounts like banking, consider using a premium aliasing service for enhanced security and privacy.
When and why should you use this approach? If you're serious about stopping unwanted emails, protecting your privacy, and minimizing the impact of potential data breaches, email aliasing is a powerful tool. It's particularly beneficial for privacy-conscious individuals, business owners, IT professionals, and anyone frustrated with the constant barrage of spam and unsolicited emails. By implementing email aliasing, you can take proactive control of your inbox and enjoy a cleaner, more secure online experience.
5. Report Spam and Phishing
Tired of unwanted emails clogging your inbox? One of the most effective ways to stop unwanted emails is to actively report spam and phishing attempts. This method leverages the built-in reporting mechanisms within your email client, not only removing the offending emails from your inbox but also training the email provider's filters to identify and block similar messages in the future. This contributes to a cleaner inbox for you and improves the overall email ecosystem for everyone.

Reporting spam and phishing works by feeding information back to your email provider. Every time you mark an email as spam or phishing, you're essentially teaching the system what constitutes unwanted mail. This information is then used to refine filtering algorithms, allowing the system to recognize patterns, keywords, sender addresses, and other characteristics common to spam and phishing emails. This ongoing feedback loop helps the system become increasingly accurate at identifying and blocking unwanted messages before they even reach your inbox.
This approach deserves its place on this list because it empowers users to take an active role in controlling their inbox and contributes to a global effort to combat unwanted emails. It's a proactive measure that moves beyond simply deleting emails and addresses the root of the problem by helping email providers improve their filtering capabilities.
Features and Benefits:
- One-click reporting: Most email clients offer easy, one-click buttons for reporting spam and phishing.
- Trains spam filters: Helps your email provider learn and recognize similar future messages.
- Global impact: Contributes data to global spam databases, helping to identify and block spammers across the internet.
- Automatic unsubscribing: Often includes automatic unsubscription from mailing lists associated with reported spam.
Pros:
- Improves filtering for both you and other users.
- Helps email providers take action against spammers.
- Simple and quick process.
- Reduces the likelihood of receiving similar emails in the future.
Cons:
- Not always effective against determined spammers who frequently change addresses.
- May occasionally misclassify legitimate emails as spam.
- Results are not immediate and require pattern recognition over time.
- Effectiveness can vary across different email providers.
Examples of Successful Implementation:
- Gmail: The "Report spam" and "Report phishing" buttons are prominently displayed and actively learn from user input to improve Google's spam filtering algorithms.
- Microsoft Outlook: Offers both "Junk" and "Phishing" reporting options to categorize unwanted emails and improve Microsoft Defender for Office 365's protection.
- Apple Mail: The "Move to Junk" feature helps train Apple's spam filters, while specific phishing reporting options are also often available.
Tips for Effective Spam and Phishing Reporting:
- Report, don't just delete: Use the spam reporting function instead of simply deleting suspicious emails.
- Avoid misclassification: Be careful not to report legitimate emails you signed up for.
- Use the right option: For phishing attempts, look for and use the specific "report phishing" option if available.
- Be consistent: Report spam consistently to improve the accuracy of your filter.
By actively reporting spam and phishing emails, you're taking a crucial step towards a cleaner, safer, and more productive inbox. This simple action can make a significant difference in your online experience and contributes to the ongoing fight against unwanted emails.
6. Email Address Compartmentalization: Take Control of Your Inbox
One of the most effective ways to stop unwanted emails and reclaim your digital sanity is through email address compartmentalization. This method involves creating and using multiple distinct email addresses for different online activities, effectively segregating your communications and minimizing the influx of unwanted messages into your primary inbox. This approach is highly recommended for anyone serious about regaining control of their email and enhancing their online privacy. This tactic deserves its place on this list because it offers a proactive, preemptive approach to managing email overload, unlike reactive measures like filters or unsubscribe buttons that often fail to stem the tide.
How it Works:
The concept is simple: instead of using one email address for everything, you create separate accounts dedicated to specific purposes. For example, you could have one address solely for personal communications with friends and family, another for online shopping and marketing subscriptions, a third for work-related emails, and yet another for less trusted websites and online forms.
Features and Benefits:
- Complete Separation: Enjoy clear boundaries between different aspects of your digital life. Your work emails won't get mixed up with shopping deals, and your personal communications remain private and clutter-free.
- Granular Security: Implement different security levels for different accounts. Your primary personal email can have the strongest password and two-factor authentication, while a throwaway account for online registrations might have less stringent security.
- Prioritized Checking: Check low-priority accounts (like shopping deals or newsletters) less frequently, freeing up your time and attention.
- Damage Control: If one address is compromised in a data breach or targeted by spammers, the impact is contained. Your other accounts and communications remain unaffected.
Examples of Successful Implementation:
- Dedicated Shopping Email: Use a dedicated email address for all online shopping, newsletters, and promotional content. This keeps your primary inbox free from marketing clutter and allows you to easily unsubscribe from unwanted marketing emails without affecting other important communications.
- 'Burner' Email for Untrusted Sites: Create a 'public' or 'burner' email for filling out online forms, registering for services you don't fully trust, or participating in online communities where you prefer a degree of anonymity.
- Separate Professional Email: Maintain a professional email address strictly for work-related communications. This presents a professional image and prevents personal emails from cluttering your work inbox.
Actionable Tips:
- Email Forwarding: Consider forwarding emails from your secondary accounts to your primary inbox while maintaining separate account identities. This allows you to check all your messages in one place without sacrificing the benefits of compartmentalization.
- Password Manager: Use a reliable password manager to securely store and manage the login credentials for all your email accounts. This simplifies access while ensuring strong, unique passwords for each.
- Clear Labeling: Label each account clearly in your email client or password manager (e.g., "Shopping," "Newsletters," "Work," "Personal"). This prevents confusion and ensures you use the correct address for each purpose.
- Customized Notifications: Set up appropriate notification settings for each account based on its importance. You might want instant notifications for work emails, but only periodic checks for shopping deals.
Pros and Cons:
Pros:
- Clear boundaries between different aspects of digital life
- Significant reduction in primary inbox clutter
- Better privacy through separation
- Easier to abandon compromised addresses without disrupting important communications
Cons:
- Requires managing multiple accounts
- Can be inconvenient to check multiple inboxes
- Potential for confusion about which address was used where
- May need multiple apps or constant logging in/out
Popularized By:
The concept of email compartmentalization has been promoted by:
- Privacy advocates like the Electronic Frontier Foundation (EFF)
- Security professionals promoting 'security by compartmentalization'
- Enterprise email management best practices
By implementing email address compartmentalization, you can significantly stop unwanted emails, enhance your privacy, and take back control of your digital life. This proactive strategy offers a powerful solution to the ever-increasing challenge of email overload.
7. Disposable Temporary Email Addresses: A Powerful Weapon Against Unwanted Emails
Tired of relentless spam clogging your inbox? Disposable temporary email addresses are a powerful tool to stop unwanted emails and reclaim control of your digital life. This method involves using short-lived email addresses for one-time signups, quick verifications, or any situation where you anticipate a barrage of spam. These addresses expire automatically after a short period, effectively cutting off the flow of unwanted messages before they even reach your primary inbox.
Here's how it works: services like 10MinuteMail, Temp-mail.org, and Guerrilla Mail generate unique email addresses that are active for a specified duration – from minutes to days. You use this temporary address instead of your real one when signing up for websites, downloading free trials, or engaging with services you deem potentially spammy. Any emails sent to the temporary address are visible in a public inbox (usually without requiring a password). Once the timer runs out, the address self-destructs, taking all the incoming junk mail with it.
Why This Method Deserves Its Place on the List:
This approach is particularly effective because it tackles the root of the problem: preventing unwanted emails from ever reaching your main inbox. It's a proactive measure that eliminates the need for constant unsubscribing or filtering.
Features and Benefits:
- No Registration (Mostly): Most temporary email services require no signup. You simply visit the website and an address is generated for you.
- Anonymous Usage: Protect your privacy by avoiding revealing your real email address to potentially untrustworthy services.
- Automatic Expiration: Set the lifespan of the address and let it vanish along with the anticipated spam.
- Public Inbox (No Password): Access your temporary inbox directly without managing another password.
Pros:
- Eliminates Follow-Up Spam: Completely stops spam from questionable sources.
- Enhanced Privacy: Shields your real email address from data harvesting and unwanted marketing.
- Ideal for Temporary Needs: Perfect for one-time verifications and short-term access.
- No Cleanup Required: No need to unsubscribe or manage overflowing spam folders.
Cons:
- Not for Ongoing Access: Unsuitable for services requiring continuous communication.
- Domain Blocking: Some websites block known temporary email domains.
- No Security: Public inboxes are accessible to anyone.
- Short Retention Periods: Messages are only stored for a limited time.
Examples of Successful Implementation:
- 10MinuteMail: Creates email addresses that expire after 10 minutes.
- Temp-mail.org: Offers disposable addresses with customizable durations.
- Guerrilla Mail: Provides temporary addresses with attachment support.
- ThrowAwayMail: Another popular choice for generating temporary email addresses.
Actionable Tips:
- Free Trials: Use temporary emails for free trials you don't intend to continue.
- Save Verification Codes: Quickly copy any important verification codes before the address expires.
- Bookmark Multiple Services: Have backups in case one service is blocked.
- Check Blacklist Policies: Be aware that some services may block temporary email domains.
By incorporating disposable temporary email addresses into your online strategy, you can effectively stop unwanted emails and maintain a cleaner, more manageable inbox. This simple yet powerful technique offers a practical solution for those seeking enhanced privacy and a spam-free online experience.
7 Strategies to Stop Unwanted Emails
| Strategy | Implementation Complexity 🔄 | Resource Requirements ⚡ | Expected Outcomes 📊 | Ideal Use Cases 💡 | Key Advantages ⭐ |
|---|---|---|---|---|---|
| Unsubscribe Using Built-in Links | Low (1-2 clicks) | Minimal (no tools required) | Reduces legitimate marketing emails gradually | Legitimate newsletters and promotional emails | Legal, straightforward, permanent for legit senders |
| Email Filtering Rules | Medium (initial setup needed) | Moderate (time to configure) | Automatic sorting and reduced inbox clutter | Handling persistent unwanted emails and organizing | Customizable, proactive, one-time setup benefits |
| Third-Party Email Management Services | Medium-High (account setup, permissions) | Moderate-High (subscription fees possible) | Bulk unsubscribing, analytics, better inbox control | Managing multiple subscriptions, heavy inbox users | Powerful automation, time-saving, AI-based categorization |
| Email Address Aliasing | Medium | Low to Moderate (may need paid service) | Identifies sources of spam, disables specific senders | New signups, privacy-focused users | Compartmentalizes email, improves security |
| Report Spam and Phishing | Low | Minimal | Removes spam, improves global filtering | Phishing and obvious spam emails | Simple, quick, helps email providers improve filtering |
| Email Address Compartmentalization | Medium | Moderate (multiple accounts) | Segregated communication, less clutter | Users wanting clear separation of email types | Clear boundaries, privacy, easier compromise handling |
| Disposable Temporary Email Addresses | Low | Minimal (free services) | Temporary access, no long-term spam | One-time signups, anonymous usage | Eliminates follow-up spam, protects privacy |
Take Back Control of Your Inbox Today
Reclaiming your inbox from the deluge of unwanted emails is entirely within your reach. We've explored seven key strategies to stop unwanted emails, from simple steps like utilizing unsubscribe links and reporting spam, to more proactive measures like setting up robust filtering rules and leveraging third-party email management services. For more advanced control, email aliasing, compartmentalization, and using disposable temporary addresses can drastically minimize unwanted mail. These techniques, when implemented consistently, empower you to filter the noise, prioritize important communications, and protect your privacy. Mastering these methods translates directly to increased productivity, reduced stress, and a greater sense of control over your digital life. Remember, a clean inbox is more than just organization; it’s a crucial step towards better managing your time, attention, and online security.
For an even more streamlined and secure approach to stop unwanted emails from the outset, consider Typewire. Typewire provides robust anti-spam and virus protection, along with advanced privacy features, helping you maintain a clean, focused inbox. Ready to experience the difference? Visit Typewire today and discover a truly private and secure email experience.

