If you feel like you're constantly digging through a mountain of junk mail just to find the messages that actually matter, you're definitely not alone. Spam isn't just a minor annoyance; it's a huge drain on productivity and a serious security risk. The first step to taking back control of your inbox is understanding why it’s overflowing in the first place.
Why Your Inbox Is Full of Spam

Spam piles up for a few key reasons, and most of them boil down to your email address getting out "in the wild." This happens all the time—through data breaches, when data brokers sell lists, or when bots scrape your address from public websites and social media profiles. Once your email is on one spam list, it’s usually sold and circulated to countless others.
The scale of the problem is pretty mind-boggling. In 2025, spam emails made up over 45% of all email traffic worldwide. Think about that. On a personal level, the average user gets about five spam messages every day, which contributes to a staggering 14.5 billion junk emails sent globally on a daily basis.
From Annoying to Dangerous
It’s also important to remember that not all spam is created equal. Knowing the difference helps you figure out what to delete and what to be truly wary of.
- Marketing Lists: You often sign up for these, maybe without realizing it. They’re usually from legitimate companies you’ve bought from or interacted with, but the sheer volume can quickly become junk.
- Unsolicited Commercial Email (UCE): This is your classic spam. It’s the random, out-of-the-blue junk mail with unsolicited offers from senders you’ve never heard of.
- Phishing Scams: This is the dangerous stuff. These emails are designed to look like they’re from legitimate companies (like your bank or a delivery service) to trick you into giving up sensitive info like passwords or credit card details.
The real goal isn't just to clean your inbox—it's to protect your digital identity. Deleting spam is a great habit, but learning to spot and report malicious emails is a critical skill.
While deleting spam gives you immediate relief, the long-term solution involves being proactive. For a deeper dive into prevention, check out our guide on how to reduce spam email.
Tackling Spam Manually in Gmail and Outlook

Even with the best tools, sometimes you just need to get in there and clean house yourself. Manually clearing out spam isn't just about reclaiming your inbox; it's a chance to teach your email provider what you consider junk, making its automatic filters smarter over time.
It’s tempting to just hit the delete button and move on, but that’s a missed opportunity. Your most powerful move is to first mark the message as spam. Think of it as giving your email client a direct piece of feedback. Doing this helps its algorithm recognize and block similar unwanted emails down the road.
Use the Search Bar to Your Advantage
Deleting emails one by one is a soul-crushing task. The real secret to clearing out hundreds, or even thousands, of messages at once lies in mastering the search bar. This is the single most effective technique for dealing with spam in huge batches.
In both Gmail and Outlook, you can search for common spammy phrases like "unsubscribe," "special offer," or "claim your prize." This will instantly group together tons of promotional junk mail, making it easy to select and delete the whole lot. For anyone using Gmail, learning the fast way to delete emails in Gmail with search operators is a game-changer.
You can get even more specific with search commands:
in:spam: Pop this into the search bar to see everything in your spam folder. From there, you can select all and permanently delete them in one go.from:[sender's domain]: Getting flooded by a particular company? A search likefrom:dodgydiscounts.comwill pull up every email they've ever sent, ready for you to wipe them out.
Here's a key thing many people miss: deleting an email from your inbox just sends it to the trash. Marking it as spam moves it to the junk folder and trains the filter. That second part is what really helps you in the long run.
Desktop vs. Mobile: A Different Approach
How you tackle spam often depends on the device you're using.
On Your Desktop
Your computer is where you’ll do the heavy lifting. The desktop versions of Gmail and Outlook are built for bulk actions. Once you’ve run a search, you can click the "Select All" checkbox. If the search turns up more than a page of results, Gmail gives you a fantastic option: a little link that says, "Select all conversations that match this search." Clicking this lets you grab every single matching email—even thousands of them—for deletion.
On Your Phone
Mobile apps are more for quick clean-ups and maintenance. You can usually long-press an email to start selecting multiple messages, then tap others to add them to the batch before deleting. It’s not as efficient for a massive purge, but it’s perfect for clearing out the daily junk while you’re waiting in line for coffee. Just remember the golden rule, no matter the device: mark as spam first, then delete.
Automating Your Inbox with Smart Filters and Rules
Manually deleting junk mail offers a brief, satisfying win, but it’s a battle you'll have to fight again tomorrow. If you want a lasting solution, you need to think about automation. Setting up smart filters and rules is like hiring a bouncer for your inbox—it stops the junk before you even have to lay eyes on it.
This approach flips the script from reactive clean-up to proactive defense. Instead of constantly wading through the same old messes, you’re training your email client to handle unwanted messages automatically. You can create rules that zap emails from persistent spammers or ones that contain those classic spammy phrases, saving you a ton of time in the long run.
Sometimes, though, a few messages will inevitably slip past your defenses. This is where a quick manual cleanup comes in handy.
The real magic happens when you turn these one-off manual deletions into permanent, automated rules. Let's walk through how to do that.
Building Your First Filter in Gmail
Getting your first filter up and running in Gmail is surprisingly simple. Just think of a common annoyance you deal with—maybe it's a persistent promotional email from a store you shopped at once, five years ago.
Go find one of those emails. Click the three vertical dots next to the reply button and choose "Filter messages like these." A small window will pop up with the sender’s address already in the "From" field. Just click "Create filter" and decide what you want to happen. For pure junk, the best option is "Delete it." That’s it. Now, any future email from that sender will go straight to the trash, bypassing your inbox completely.
Creating a Powerful Rule in Outlook
Over in Outlook, the same concept is called "rules." Let's say you're getting hammered with emails all screaming "Claim Your Exclusive Prize!" in the subject line. You can build a rule to make them vanish on arrival.
Right-click on one of the spam messages, hover over "Rules," and then select "Create Rule." In the box that appears, you can set your conditions. In this case, you'd check the box for "Subject contains" and type in a key phrase like Exclusive Prize. Then, under "Do the following," just select "Move the item to folder" and pick your Deleted Items folder.
By creating rules based on common spam phrases like "limited time offer" or "final notice," you can catch entire categories of junk mail, not just single senders. This approach significantly reduces the amount of spam that ever reaches your inbox.
Quick Filter Setup for Common Spam Types
To get you started, here are a few effective filtering rules you can implement right away in either Gmail or Outlook. Think of these as your starter kit for a cleaner inbox.
| Spam Type | Filter Condition (Example) | Action to Take |
|---|---|---|
| Fake Invoices | Subject contains: "Your invoice is ready" OR "Payment confirmation" | Delete it OR Send to spam |
| Phishing Attempts | Has the words: "Verify your account" OR "Unusual sign-in activity" | Move to a "Review" folder OR Delete it |
| Unwanted Newsletters | From: *@example-newsletter.com (use the specific sender) |
Delete it OR Apply a label and archive |
| "You've Won!" Scams | Subject contains: "Congratulations" OR "You are a winner" OR "Claim your prize" | Send to spam OR Delete it |
Setting up just one or two of these can make a noticeable difference almost immediately. As you spot new types of spam, you can simply add more rules to keep your defenses strong.
Recognizing and Deleting Dangerous Phishing Emails
Not all junk mail is just annoying marketing clutter. Some of it is far more sinister—designed specifically to steal your personal information. This is called phishing, and it requires a different mindset. It's not just about cleaning your inbox; it's about actively defending it.
Think of it this way: deleting regular spam is like tossing junk mail. Identifying and removing a phishing email is like spotting a burglar casing your house and calling the police.
Phishing attacks are clever. They often masquerade as messages from brands you trust—your bank, Amazon, or even a delivery service like FedEx. They'll create a false sense of urgency, trying to rush you into making a mistake. A classic example is that email claiming "unusual sign-in activity" on your account, pushing you to click a link right now to secure it.
Spotting the Deception
Before you hit delete, take a deep breath and look for the tell-tale signs. These red flags are often subtle, but once you know what to watch for, they stick out like a sore thumb.
- Suspicious Sender Address: This is the easiest giveaway. Hover your mouse over the sender's name (don't click!). A real email from your bank isn't going to come from
bank-security-alert83@aol.com. - Generic Greetings: Scammers blast these emails out to thousands of people. If it says "Dear Valued Customer" instead of your actual name, be suspicious.
- Urgent or Threatening Language: Phrases like "Your account will be suspended" or "Immediate action required" are meant to trigger panic, so you'll act before you think.
When you come across a phishing attempt, the drill is always the same: report it, then delete it. Whatever you do, don't click any links or download attachments. That's exactly what the attackers want.
This isn't a small problem. Phishing is a massive, industrialized operation. Globally, an estimated 102 billion phishing emails are expected to be sent by Q2 2025. These attacks now account for a staggering 1.2% of all email traffic, which works out to roughly 3.4 billion phishing attempts every single day. Discover more insights about these phishing trends at SQ Magazine.
Getting good at spotting these threats is your first line of defense. To take your security to the next level, check out our guide on essential security tips to avoid phishing emails.
Advanced Strategies to Stop Spam at the Source

The best way to learn how to delete spam mail is to stop it from showing up in the first place. This means getting ahead of the problem and proactively defending your inbox, rather than just reacting to the daily junk pile.
Here's a tip I've learned the hard way: be very careful with that "unsubscribe" link. If the email is from a brand you recognize and trust, go ahead and click it. But if it's a random, unsolicited message, hitting "unsubscribe" can actually make things worse. It tells the spammers your email is active, and they'll often sell it to other lists, inviting an even bigger flood of junk. Marking it as spam is always the smarter move.
Be Strategic with Your Email Address
Start thinking of your primary email address like your home address—you wouldn't just hand it out to anyone. Protecting it is your first line of defense.
- Use Disposable Emails: I always keep a secondary email handy for signing up for newsletters, store discounts, or new apps. This keeps my main inbox clean and protects it if one of those services ever has a data breach.
- Be Mindful Where You Share: Never post your main email address on public-facing profiles like social media or online forums. Automated bots constantly crawl these sites looking for active emails to target.
Treating your primary email like a valuable asset is a powerful mindset shift. It creates a natural barrier against the constant stream of spam and makes a huge difference in keeping your inbox manageable.
It's a global issue, too. Research from EmailToolTester on global spam sources shows just how widespread the problem is, with China alone having over 771,000 IP addresses sending spam.
If you're already feeling buried under a mountain of junk mail, we have a more in-depth guide that can help. Check out our article on how to block unwanted emails for more powerful solutions.
Got More Questions About Dealing With Spam?
Even after you've started clearing out the junk, a few questions always seem to pop up. Let's tackle some of the most common ones so you can manage your inbox with total confidence.
Does Just Deleting Spam Actually Stop More of It?
Here's the short answer: no. When you just hit the delete key, the spammer on the other end has no idea. Your action doesn't get you off their list or stop them from trying again.
The real power move is to mark the message as "spam" or "junk" before you delete it. This is crucial because it acts as a feedback signal for your email provider. You're essentially teaching the system, "Hey, I don't want to see messages like this anymore." Over time, this makes the automatic filters much smarter at catching similar junk before it even hits your inbox.
Think of it this way: by marking something as spam, you're not just tidying up your own space. You're helping improve the spam filter for everyone. It's a tiny click that makes a huge difference.
Should I Ever Click the "Unsubscribe" Link?
This is a tricky one, and the right answer really depends on who sent the email. If it's a newsletter from a brand you know and trust, then yes, the unsubscribe link is almost always safe. Reputable companies are legally required to honor those requests and want to keep their mailing lists healthy.
But what about those random, bizarre emails from senders you've never heard of? In those cases, clicking "unsubscribe" can actually backfire. It tells the spammers that your email address is live and being checked, which ironically makes your address more valuable to them. They might just sell it to other spammers.
When in doubt, if you don't recognize the sender, don't click anything. Just mark it as spam and delete it.
What's the Real Difference Between Blocking and Filtering?
It's all about precision.
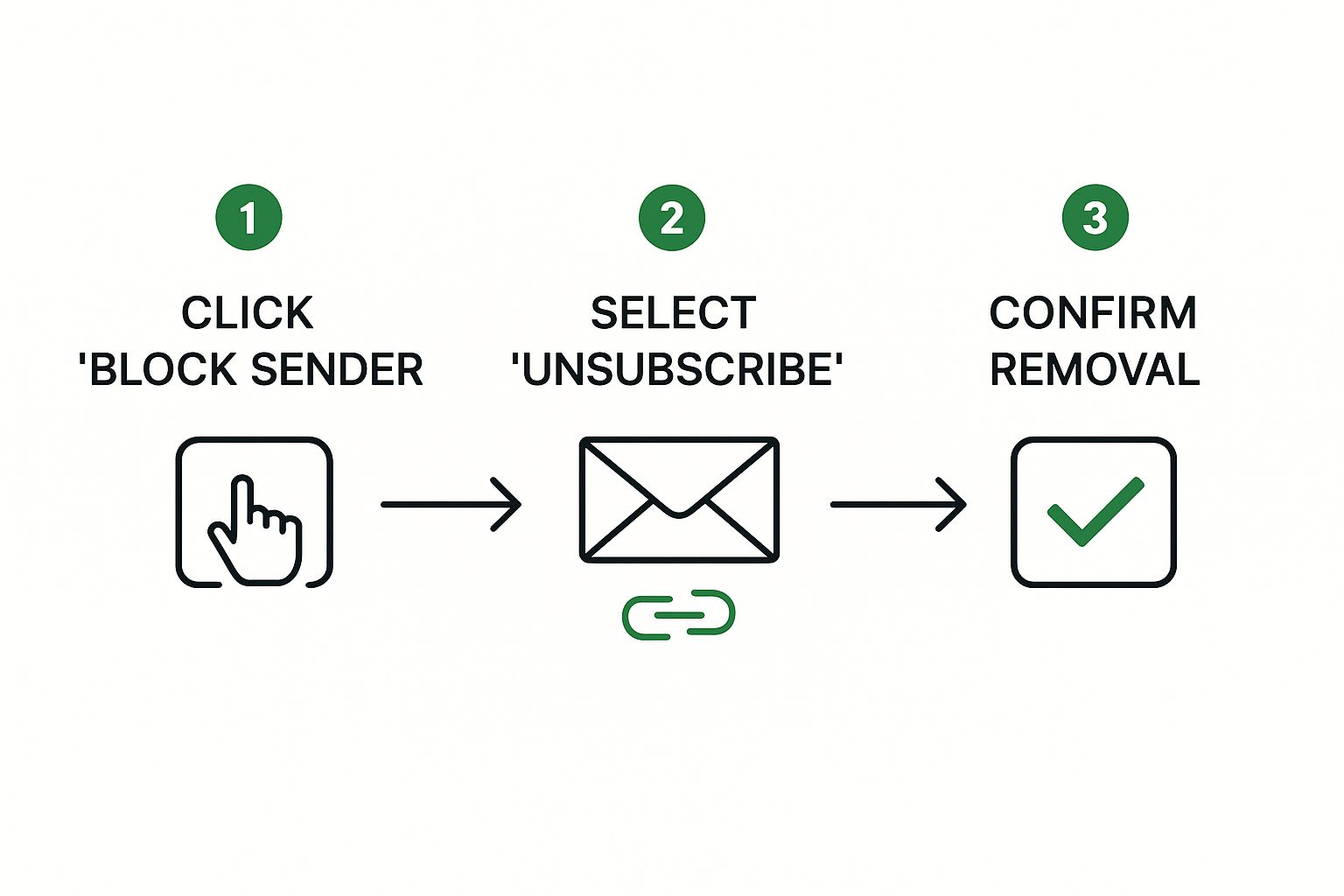
- Blocking a sender is like putting up a "no trespassing" sign for one specific person. It tells your email client to send every single future email from that one email address directly to the junk folder. It's simple, direct, and great for that one persistent pest.
- Creating a filter (or a "rule") is far more strategic. Instead of just looking at the sender, a filter can hunt for keywords in the subject line, specific phrases in the email body, or other patterns. This lets you automatically catch and delete whole categories of junk mail, no matter who sends it. It’s your go-to tool for more advanced inbox control.
Tired of constantly playing defense against spam? Typewire moves beyond simple management to provide serious prevention with advanced anti-spam and virus protection. We keep your inbox clean so you can focus on what matters.
Give our private, ad-free email a try with a free trial and see the difference for yourself.





