Think of standard email as a postcard – anyone handling it can read the message. Secure email for small business is like a letter sealed in a tamper-proof envelope, delivered directly into the right hands. This shift from open to protected communication isn’t optional; it’s a business necessity.
With 43% of all cyberattacks in 2023 targeting small businesses and 95% of cybersecurity breaches caused by human error, choosing the right secure email solution is critical. This guide provides a practical framework for evaluating providers, comparing features, and implementing a solution that protects your business without overwhelming your team.
For a comprehensive understanding of email security threats and defense strategies, see our detailed guide: Email Security for Small Business: Protect Your Data Now

Understanding Must-Have Security Features
Choosing a secure email service requires understanding core concepts beyond the marketing jargon. These aren’t buzzwords – they’re the actual tools that build a digital fortress around your business communications.
End-to-End Encryption: The Foundation
At the heart of any secure email for small business is end-to-end encryption (E2EE). Think of it as sending a message in a locked box. When you hit “send,” your email is scrambled, and only your intended recipient has the unique key to unscramble it. Nobody in between – not even your email provider – can peek inside.
How it works:
- Message encrypts on your device before sending
- Travels as unreadable code across the internet
- Only decrypts on recipient’s device with their unique key
- Provider has no access to message content
Beyond Basic Encryption: Essential Layered Defenses
While encryption is the bedrock, genuinely secure services build multiple protection layers:
Two-Factor Authentication (2FA): Requires a second verification factor beyond your password. Even if hackers steal credentials, they can’t access your account without the second factor (usually a code from your phone or authenticator app).
Advanced Threat Protection: Specifically designed to spot sophisticated attacks like Business Email Compromise (BEC). Organizations with under 1,000 employees face a 70% chance of being targeted by at least one BEC attack weekly, with average costs per incident reaching $4.89 million.
Spam and Malware Filtering: Automatically identifies and blocks malicious emails before they reach employee inboxes.
Data Loss Prevention (DLP): Prevents sensitive information from leaving your network, either accidentally or maliciously.
Access Controls and Permissions: Restricts data access based on employee roles, minimizing damage if one account is compromised.
Essential Secure Email Features Comparison
| Feature | Purpose | Business Impact | Priority Level |
| End-to-End Encryption | Protects message content | Ensures only sender/recipient can read emails | Critical |
| Two-Factor Authentication | Adds account access layer | Prevents unauthorized access even with stolen passwords | Critical |
| Advanced Threat Protection | Detects sophisticated attacks | Blocks BEC, phishing, impersonation attempts | High |
| Spam/Malware Filtering | Blocks malicious emails | Reduces employee exposure to threats | High |
| Data Loss Prevention | Prevents data leaks | Stops sensitive info from leaving network | Medium-High |
| Mobile App Security | Protects remote access | Secures email on smartphones/tablets | Medium |
| Audit Logs | Tracks all email activity | Provides visibility for investigations | Medium |
| Email Archiving | Preserves communications | Supports compliance and legal requirements | Medium |
Evaluating Providers: Your Decision Framework
Picking the right provider comes down to matching the service to what your business actually does day-to-day. A law firm handling privileged client information has completely different needs than a creative agency sending large design files.
Step 1: Assess Your Core Security and Compliance Needs
Industry Regulations: Start by identifying your compliance requirements. Different industries have specific mandates:
- Healthcare: HIPAA requires encryption of Protected Health Information (PHI)
- Financial Services: Gramm-Leach-Bliley Act (GLBA) mandates customer data protection
- Legal: Attorney-client privilege requires confidential communication channels
- EU Data Handling: GDPR compliance for any European customer data
Data Sensitivity: What information flows through your emails?
- Financial statements and banking information
- Customer personal data (names, addresses, payment info)
- Proprietary business plans and trade secrets
- Employee personal information
- Contracts and legal documents
Your answer determines whether you need basic encryption or advanced features like DLP and custom retention policies.
Step 2: Evaluate Usability and Integration Requirements
A secure email platform can’t exist in isolation – it must integrate seamlessly with existing tools.
Integration Checklist:
- Works with current productivity suite (Microsoft 365, Google Workspace)
- Supports calendar and contact synchronization
- Integrates with CRM and project management tools
- Offers API access for custom integrations
- Supports single sign-on (SSO) if you use it
User Experience Considerations:
- Clean, intuitive interface that doesn’t require extensive training
- Consistent experience across desktop, web, and mobile
- Simple email composition and encryption process
- Easy contact management and search functionality
- Mobile apps that work offline
Red flag: If the mobile app is clunky or difficult to use, team members will find workarounds – and those workarounds are rarely secure.
Step 3: Analyze Scalability and Pricing Models
Your business will grow, and your email service should grow with you.
Scalability Questions:
- How easy is it to add new team members?
- Can you upgrade plans for more storage or features?
- Are there user limits on different plan tiers?
- Can you customize plans as needs change?
- What’s the process for enterprise upgrades?
Common Pricing Models:
| Pricing Structure | How It Works | Best For | Watch Out For |
| Per-User Monthly | Fixed price per user/month | Predictable budgeting, teams 5-50 | Annual commitments may be required |
| Tiered Plans | Different feature sets at price points | Growing businesses needing flexibility | Feature restrictions on lower tiers |
| Storage-Based | Price varies by data storage | Organizations with varying email volume | Unexpected overage charges |
| Enterprise Custom | Negotiated based on needs | Large organizations 50+ users | Complex pricing, longer sales cycles |
Hidden Costs to Investigate:
- Email archiving and compliance features
- Priority customer support
- Additional storage beyond base allocation
- Mobile device management (MDM) integration
- Advanced reporting and analytics
- User training and onboarding assistance
Provider Feature Comparison Framework
Use this framework to evaluate and compare potential providers systematically.
Security Features Deep Dive
| Feature Category | Questions to Ask | What to Look For |
|---|---|---|
| Encryption | What encryption standards are used? Is it end-to-end? | AES-256 or higher, zero-access architecture |
| Authentication | What 2FA options are supported? | Authenticator apps, hardware keys (not just SMS) |
| Threat Protection | How are sophisticated attacks detected? | AI-powered analysis, behavioral detection |
| Compliance | What certifications does the provider hold? | SOC 2, ISO 27001, industry-specific (HIPAA, etc.) |
| Data Residency | Where are servers located? Can you choose? | Privacy-friendly jurisdictions, data location control |
| Audit Capabilities | What logs are available? How long are they retained? | Detailed access logs, configurable retention |
Provider Comparison Table
| Provider Type | Typical Features | Price Range | Implementation Time | Best For |
|---|---|---|---|---|
| Built-in Provider Security (Gmail, Outlook with basic settings) | Basic spam filtering, TLS encryption, limited 2FA | $6-12/user/month | 1-2 days | Very small teams (1-5), low sensitivity data |
| Enhanced Provider Plans (Microsoft 365 E3/E5, Google Workspace Enterprise) | Advanced threat protection, DLP, some compliance tools | $20-35/user/month | 1-2 weeks | Growing businesses (10-50), moderate compliance needs |
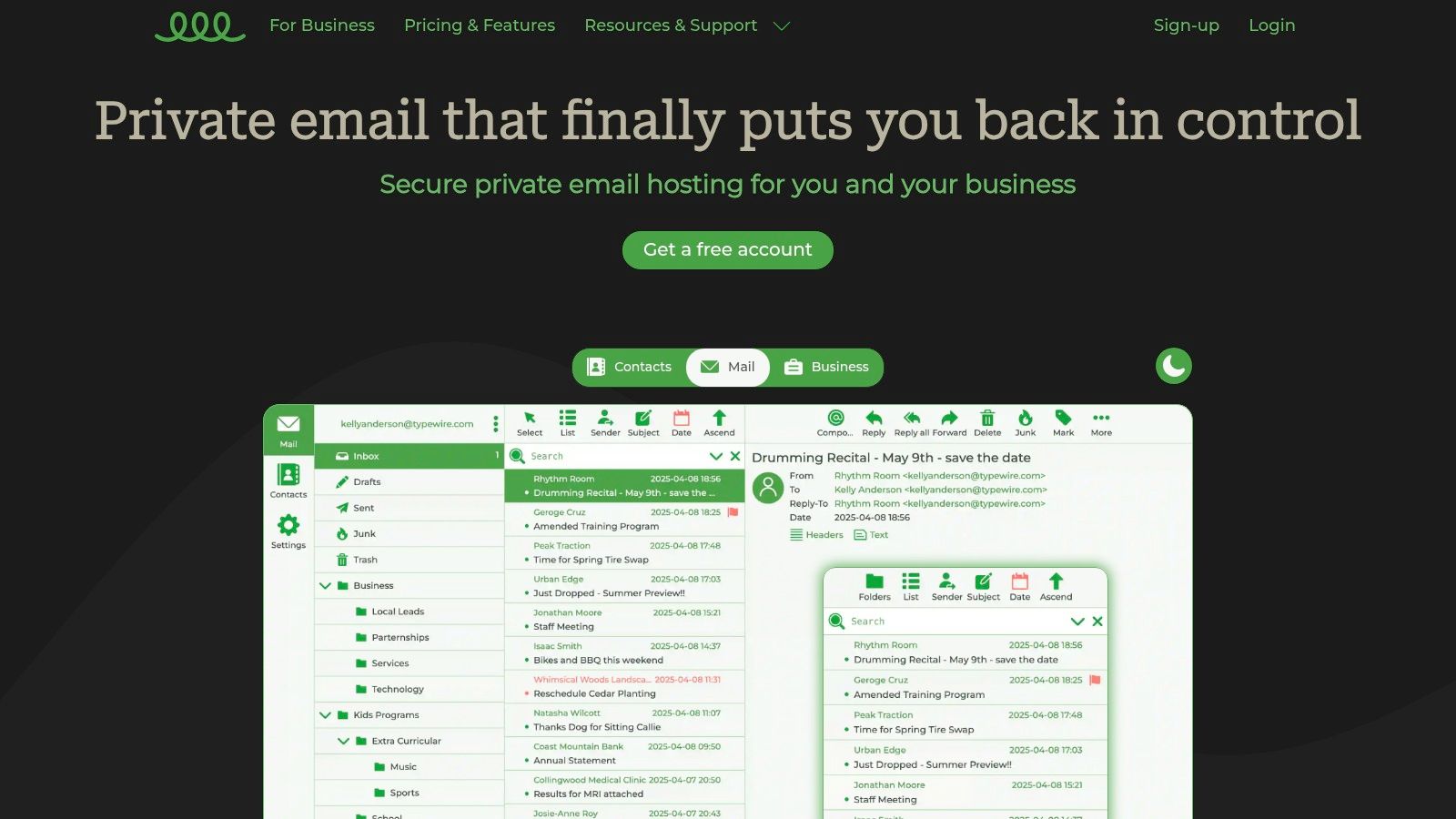
| Dedicated Secure Email (ProtonMail Business, Tutanota Business) | End-to-end encryption, zero-access, strong privacy | $8-30/user/month | 1-2 weeks | Privacy-focused businesses, strict data protection |
| Email Security Gateway (Proofpoint, Mimecast add-on to existing email) | Advanced threat detection, URL rewriting, sandboxing | $3-10/user/month (additional) | 2-4 weeks | Businesses keeping current email, need added protection |
| Full Enterprise Platform (Custom solutions) | All features, custom integration, dedicated support | $50+/user/month | 1-3 months | Large organizations (50+), complex requirements |
Feature Checklist for Provider Evaluation
Must-Have Features:
- End-to-end encryption or equivalent strong encryption
- Two-factor authentication (2FA/MFA)
- Spam and malware filtering
- Mobile access (iOS and Android apps)
- Custom domain support (yourcompany.com)
- Standard email features (calendar, contacts)
- Data backup and recovery
- Basic compliance features for your industry
Nice-to-Have Features:
- Advanced threat protection (anti-phishing, anti-spoofing)
- Data loss prevention (DLP)
- Email archiving with search
- Detailed audit logs and reporting
- Single sign-on (SSO) support
- Integration with productivity tools
- Priority customer support
- Custom retention policies
Enterprise Features (50+ users):
- Advanced admin controls and policies
- Role-based access control (RBAC)
- Dedicated account manager
- Service level agreement (SLA)
- API access for custom integrations
- Advanced compliance (eDiscovery, legal hold)
- Unlimited email aliases
- White-label options
Implementation Roadmap
A successful transition to secure email follows a structured approach that minimizes disruption while maximizing security benefits.
Phase 1: Assessment and Provider Selection (Week 1-2)
Define Your Security Needs:
- List all sensitive data types you handle via email
- Identify applicable compliance requirements (HIPAA, GDPR, etc.)
- Document current pain points with existing email
- Determine budget constraints (per-user, total budget)
- Assess technical expertise available (IT staff, managed services)
Evaluate Potential Providers:
- Create shortlist of 3-5 providers meeting minimum requirements
- Request demos or trial accounts
- Test mobile apps and user experience
- Verify integration capabilities with current tools
- Review pricing for your team size and growth projections
Make Your Decision:
- Compare providers using evaluation framework above
- Check references from similar-sized businesses
- Clarify any pricing or feature questions
- Confirm compliance certifications
- Select provider and plan tier
Phase 2: Implementation and Team Onboarding (Week 3-4)
Technical Setup:
- Configure custom domain and DNS records
- Set up administrative accounts and policies
- Enable two-factor authentication for all accounts
- Configure spam filtering and threat protection
- Test email sending/receiving functionality
- Set up mobile device access
- Configure integrations with existing tools
User Migration:
- Create user accounts in batches
- Import contacts and calendar data
- Migrate existing emails (if required)
- Test each user’s setup before rollout
- Provide login credentials securely
Team Training:
- Schedule onboarding sessions (15-30 minutes per user)
- Demonstrate basic email functions
- Show how encryption works (if applicable)
- Explain 2FA setup and usage
- Distribute quick-reference guides
- Set up support channel for questions
Phase 3: Ongoing Training and Policy Review (Ongoing)
Regular Security Training:
- Conduct quarterly phishing simulations
- Share monthly security tips and updates
- Review and update email policies annually
- Train new employees during onboarding
- Provide advanced training for administrators
Continuous Improvement:
- Monitor security alerts and incidents
- Review access logs for unusual activity
- Update email policies as threats evolve
- Gather user feedback on pain points
- Evaluate additional features or upgrades
- Conduct annual provider review
Common Implementation Mistakes to Avoid
Mistake 1: Assuming Default Settings Are Sufficient
Many businesses deploy secure email but never configure critical security features.
The Fix:
- Enable multi-factor authentication (MFA) immediately – non-negotiable
- Review and adjust user permissions based on actual roles
- Configure spam filtering to appropriate sensitivity
- Set up automated security alerts
- Enable audit logging for compliance
Mistake 2: Neglecting Employee Training
The most secure system fails if employees don’t know how to use it properly. Over 60% of small businesses hit with cyberattacks close within six months, often due to human error.
The Fix:
- Build security training into company culture
- Run bite-sized training sessions regularly
- Send simulated phishing tests quarterly
- Make reporting suspicious emails easy and praised
- Turn security awareness into a reflex, not a chore
Mistake 3: Choosing Based on Price Alone
The cheapest option often lacks critical features or support needed for your business.
The Fix:
- Calculate total cost of ownership (licensing + implementation + training + support)
- Factor in cost of potential breach ($4.89M average for BEC incidents)
- Consider hidden costs like add-on features or overage charges
- Evaluate support quality – good support prevents costly mistakes
- Think long-term: can the solution grow with you?
Your Secure Email Selection Checklist
Use this final checklist to ensure you’ve covered all critical decision points:
Security Requirements:
- Identified all compliance requirements (HIPAA, GDPR, etc.)
- Determined required encryption level (TLS vs. E2EE)
- Assessed need for advanced threat protection
- Evaluated data residency requirements
Provider Evaluation:
- Created shortlist of 3-5 qualified providers
- Tested user interface and mobile apps
- Verified integration with existing tools
- Checked references from similar businesses
- Confirmed transparent, predictable pricing
Implementation Planning:
- Assigned implementation lead and timeline
- Planned technical setup steps
- Scheduled user training sessions
- Prepared communication for team
- Identified success metrics
Ongoing Management:
- Established regular security training schedule
- Set up process for reporting suspicious emails
- Created policy for adding new users
- Planned quarterly security reviews
- Defined escalation process for incidents
Ready to Secure Your Business Email?
Choosing secure email for your small business is a critical decision that impacts data protection, compliance, and operational efficiency. By following this buyer’s guide framework, you can systematically evaluate providers, compare features, and implement a solution that protects your business without overwhelming your team.
Key Takeaways:
- Match security features to your specific compliance and data sensitivity needs
- Prioritize usability – the best security fails if employees won’t use it
- Consider total cost of ownership, not just monthly per-user pricing
- Plan for growth – choose a scalable solution
- Invest in employee training alongside technology
For comprehensive information on email security threats, defense strategies, and team training: Email Security for Small Business: Protect Your Data Now
Ready to take control of your business communications? Typewire offers secure, private email hosting with end-to-end encryption, advanced spam protection, and zero data mining. Start your free 7-day trial today and experience true email privacy.