In an environment where data breaches are common and invasive tracking is the norm, standard email has become a significant liability. Your inbox, once a simple communication tool, is now a primary target for sophisticated phishing attacks, intrusive advertising, and relentless data mining. Treating it with a casual, outdated approach is no longer a viable option. Effective and professional correspondence now depends entirely on a foundation of robust security and uncompromising privacy.
This guide moves past generic advice to provide a comprehensive roundup of essential email communication best practices designed for the modern, privacy-conscious user. We will provide actionable steps that transform your email from a point of vulnerability into a secure, efficient, and reliable asset. The focus is squarely on practical implementation, covering everything from foundational security protocols like SPF and DKIM to advanced strategies for inbox organization and user management within a secure ecosystem.
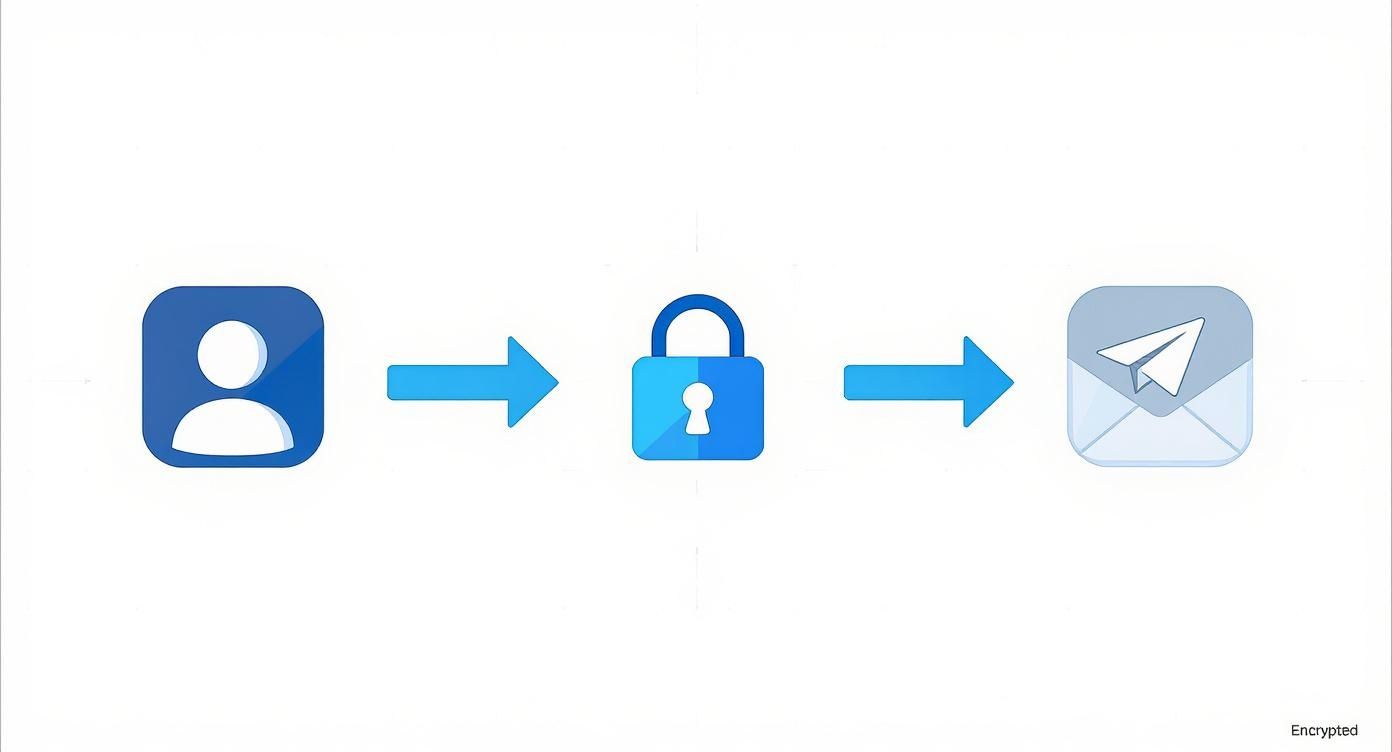
You will learn how to leverage hosted email platforms to enforce strong privacy controls, enhance message deliverability to avoid spam filters, and master the art of secure, professional correspondence. For individuals and businesses committed to protecting their data, especially those using privacy-first services like Typewire, these practices are not just helpful tips. They represent a fundamental framework for building trustworthy, confidential, and effective communication channels. Each point in this listicle is crafted to be immediately applicable, helping you secure your digital conversations and reclaim control over your inbox.
1. Master Hosted Email Platforms for Ultimate Control
The single most impactful step in establishing secure and private email communication best practices is moving away from free, ad-supported services. Choosing a premium hosted email platform places you in complete control of your data, establishing a secure foundation for all other privacy measures. Unlike free services that often treat your data as the product through tracking and ad-targeting, a hosted platform operates on private infrastructure dedicated to protecting your information.
Why Hosted Email is Non-Negotiable for Privacy
A hosted email solution means your communications are not scanned to build advertising profiles or sold to data brokers. This model is fundamentally aligned with user privacy. The provider’s business is to protect your data, not monetize it. This separation is critical for maintaining confidentiality and security, especially when handling sensitive information.
For example, a law firm using a platform like Typewire can guarantee attorney-client privilege, as communications are stored on secure, private servers inaccessible to third parties. Similarly, a healthcare provider can manage patient correspondence in a HIPAA-compliant environment, a feat nearly impossible with standard free email accounts.
Key Insight: With a hosted email platform, you are the customer, not the product. Your privacy is a feature you pay for, not a commodity to be traded.
Actionable Steps for Implementation
Making the switch to a hosted platform is straightforward. Follow these tips to ensure a successful transition and maximize your control:
- Prioritize Full-Stack Providers: Select a provider that owns and operates its own hardware and data centers, like Typewire. This model eliminates the risks associated with third-party data handlers and gives you a single point of accountability for security.
- Leverage User Management Tools: Once set up, use the platform's administrative controls to create custom roles and permissions for your team. This ensures that employees only access the information necessary for their jobs, minimizing internal data exposure.
- Utilize Free Trials: Before committing, take advantage of trial periods to test the platform’s security features, user interface, and overall performance. Confirm it meets your specific workflow and compliance needs.
- Confirm 24/7 Support: Ensure your chosen provider offers robust, around-the-clock support. Immediate access to expert help is crucial for resolving any potential security or deliverability issues.
2. Personalize Email Content Without Sacrificing Privacy
True personalization in email communication best practices goes far beyond a simple [First Name] merge tag. It involves creating a tailored experience by leveraging recipient-specific information, but it must be done within a secure, privacy-first framework. This dynamic approach transforms generic broadcasts into relevant, one-to-one conversations that build trust, all while respecting user privacy and avoiding invasive data collection.

Why Advanced Personalization is a Privacy-First Strategy
When executed responsibly, advanced personalization strengthens the user relationship because it is based on consent and delivered value. Unlike invasive tracking, this strategy relies on voluntarily provided or first-party engagement data to enhance the user experience, not exploit it for third-party advertising. The goal is to deliver content so relevant that it feels like a service, not a sales pitch, all within the secure confines of your hosted email platform.
For example, a project management tool might send a user an email with tips specifically for a feature they frequently use, enhancing their workflow. A privacy-focused platform like Typewire could use onboarding data to send customized security checklists, helping new teams configure their accounts for maximum protection from day one. This level of detail demonstrates that you understand and respect the user’s needs without compromising their data.
Key Insight: Meaningful personalization is a sign of respect for your audience's time and privacy. It proves you are listening and shifts your communication from being intrusive to being indispensable.
Actionable Steps for Implementation
Implementing advanced personalization requires a strategic approach that prioritizes data privacy and relevance. Follow these steps to create emails that resonate deeply with your audience:
- Segment Audiences Meaningfully: Move beyond basic demographics. Create segments based on engagement levels (e.g., active users, inactive users), feature usage, or content preferences to send highly targeted messages.
- Utilize Dynamic Content: Implement conditional content blocks within your emails. This allows you to show or hide specific sections based on a recipient's segment, so a single campaign can deliver multiple personalized versions.
- Implement Progressive Profiling: Use forms to gradually collect more information over time instead of asking for everything at once. This builds a richer user profile in a non-intrusive way, respecting the user's comfort level.
- Prioritize Consent and Transparency: Always be clear about what data you are collecting and how it will be used to personalize their experience. Provide easy-to-find opt-out options for all types of communication.
3. Maintain Consistent Sending to Boost Sender Reputation
Establishing a predictable sending schedule is a core component of effective email communication best practices, building trust with both your audience and email service providers. Irregular sending patterns, such as long periods of silence followed by a sudden burst of messages, can trigger spam filters and damage your sender reputation. A consistent cadence signals to inbox providers that you are a legitimate, reliable sender, which is crucial for email security and deliverability.
Why Consistency Builds Trust and Deliverability
A regular email schedule conditions your audience to expect your communications, reducing the likelihood of spam complaints. From a technical security perspective, email platforms like Typewire analyze sending volume and frequency to assess sender reputation. Consistency demonstrates responsible email behavior, preventing your messages from being flagged as suspicious or part of a potential spam attack. This is a key factor in passing through modern, AI-driven security filters.
For example, a security-focused newsletter arriving at the same time each week builds a powerful reader habit and reinforces its legitimacy. This predictability helps email servers differentiate your planned communications from anomalous, potentially malicious activity, ensuring your important security updates or account notifications are not mistakenly filtered.
Key Insight: Consistency is not just about marketing; it’s a security and deliverability signal. Predictable sending patterns are a hallmark of a trustworthy sender, reducing the risk of being flagged by spam filters.
Actionable Steps for Implementation
Creating a reliable schedule is a strategic process that enhances your security posture. Use these steps to build a consistent and effective sending rhythm:
- Analyze Engagement Metrics: Dive into your email analytics to identify the days and times when your audience is most active. Use this data to establish a baseline for your sending schedule, optimizing for secure and reliable delivery.
- Create an Editorial Calendar: Plan your content in advance. An editorial calendar removes the pressure of last-minute content creation and ensures a steady, predictable stream of communication that email servers recognize as legitimate.
- Offer Frequency Preferences: Empower your subscribers by allowing them to choose how often they hear from you (e.g., daily, weekly, or monthly). This respects user preference and reduces the chance of spam complaints that harm your reputation.
- Secure Your Foundation: Ensure your scheduling efforts are supported by robust security. For a comprehensive approach to securing your digital identities, refer to these credential management best practices for secure accounts.
4. Implement Clear Call-to-Action (CTA) Buttons to Prevent Phishing
Effective email communication guides the recipient toward a specific, safe action. Implementing prominent, unambiguous call-to-action (CTA) buttons is a critical component of secure email communication best practices. Clear CTAs provide a trusted, low-friction path for your audience, helping them distinguish legitimate requests from the deceptive links often found in phishing attacks.

Why Clear CTAs Enhance Security
In an era of sophisticated phishing, a well-designed CTA builds user confidence. When your emails consistently use a clear, branded button for primary actions, users learn to recognize it as a legitimate signal. This makes them less likely to click on rogue text links or suspicious attachments. A clear CTA removes ambiguity and trains recipients to look for trusted visual cues before acting, reinforcing secure online behavior.
For example, a bank that always uses a distinct, blue 'Login to Your Account' button trains its customers to be wary of emails that use generic text links for the same action. This simple design consistency becomes a subtle but powerful security feature, helping users spot fraudulent attempts to steal their credentials.
Key Insight: A call-to-action button is not just a link; it's a visual and psychological cue that directs user behavior and can be a key part of your anti-phishing strategy.
Actionable Steps for Implementation
Creating high-performing, secure CTAs involves a blend of design principles and strategic placement. Use these tips to craft buttons that get results:
- Use First-Person Action Verbs: Frame the CTA from the user’s perspective to create a sense of ownership. Text like 'Access My Secure Portal' or 'Verify My Account' clearly communicates the action and intent.
- Ensure Mobile Accessibility: Design buttons with a minimum height of 40-60 pixels to make them easy to tap on mobile devices. A frustrating mobile experience can lead users to seek alternative, less secure methods.
- Prioritize Color Contrast: To meet accessibility standards and ensure visibility, aim for a color contrast ratio of at least 4.5:1 between the button and its background. Use a prominent, on-brand color that stands out.
- Place CTAs Strategically: Position your primary CTA "above the fold" so it is visible without scrolling. Ensure the destination URL is clear and directs to your secure, HTTPS-enabled domain.
5. Optimize Email Layout for a Secure Mobile Experience
With over half of all emails now opened on mobile devices, optimizing your layout for smaller screens is a core tenet of secure email communication best practices. A mobile-first approach ensures your messages are readable and professional, but more importantly, it helps prevent user error that can lead to security risks. A poorly rendered email can cause users to misclick on malicious links or struggle to identify legitimate sender details.

Why Mobile-First Design is Crucial for Security
A responsive email design automatically adapts its layout to fit the screen, ensuring a seamless and secure experience. When an email is difficult to read, users may rush through it, missing subtle signs of a phishing attempt. Clear, legible text and properly sized buttons reduce the chance of accidental clicks on malicious content disguised to look like legitimate links.
For instance, a responsive design ensures that the sender's email address is fully visible, not truncated, allowing the recipient to verify its authenticity. For internal communications on a secure platform like Typewire, a responsive layout ensures that team members on the go can quickly read and act on important security alerts without the risk of misinterpretation caused by a broken layout.
Key Insight: Mobile optimization is a security feature. A clean, responsive design reduces user error and makes it easier for recipients to identify and avoid phishing threats.
Actionable Steps for Implementation
Ensuring your emails are secure and readable on every device is a technical but achievable goal. Use these strategies to create a consistently safe viewing experience:
- Adopt a Single-Column Layout: Use a single-column structure that stacks content vertically. This is the most reliable way to ensure readability and prevent elements from overlapping or becoming unclickable on narrow screens.
- Utilize CSS Media Queries: Implement media queries in your email’s code to apply different styles based on screen width. This allows you to adjust font sizes and reformat layouts to maintain clarity on mobile devices.
- Compress Images: Large image files can slow down loading times, especially on mobile data connections. Compress all images to ensure the email loads quickly and completely.
- Test Extensively: Before sending, use tools to preview your email across dozens of mobile clients and devices. This helps you confirm that all links are correctly rendered and that there are no layout issues that could obscure important security information.
6. Build and Maintain a Clean Email List for Security
A core component of effective email communication best practices involves prioritizing list quality over quantity. Maintaining a clean email list is not just about deliverability; it's a security and privacy fundamental. A bloated list filled with inactive, invalid, or disengaged subscribers increases your risk profile, wastes resources, and damages your sender reputation, making it harder for your legitimate communications to reach their intended recipients.
Why List Hygiene is a Security Imperative
A clean, engaged email list is a direct reflection of a healthy sender reputation. Internet Service Providers (ISPs) and secure email platforms like Typewire analyze engagement metrics to filter spam and malicious content. High bounce rates from sending to non-existent addresses can signal that your system may be compromised and used for spamming. This hygiene practice ensures your critical communications are not mistakenly flagged as threats.
For instance, a financial services firm sending quarterly statements must ensure its list is pristine. Removing hard bounces immediately prevents repeated attempts to send sensitive information to non-existent or compromised addresses, closing a potential security loophole. Regularly purging unengaged users also reduces the data footprint, minimizing the impact of a potential data breach.
Key Insight: A clean email list is your first line of defense in protecting sender reputation. It tells receiving servers that you are a legitimate, responsible communicator, ensuring critical emails are delivered securely.
Actionable Steps for Implementation
Implementing a consistent list hygiene strategy is crucial for maintaining both deliverability and security. Follow these steps to build and maintain a high-quality email list:
- Implement Double Opt-In: Require new subscribers to confirm their email address via a confirmation link. This validates every address from the start and prevents malicious bots from flooding your list with fake accounts.
- Remove Hard Bounces Immediately: Configure your sending platform to automatically remove email addresses that result in a hard bounce (a permanent delivery failure). This is a critical signal to ISPs that you manage your list responsibly.
- Create Re-Engagement Campaigns: For subscribers who have been inactive for a set period, such as 90 days, launch an automated re-engagement campaign. If they do not interact, remove them from your active sending list to reduce your attack surface.
- Monitor Spam Complaint Rates: Pay close attention to your spam complaint rate. Immediately remove any user who marks your email as spam to prevent further damage to your domain’s reputation.
7. Use Authentication Protocols (SPF, DKIM, DMARC)
Implementing modern email authentication protocols is a non-negotiable step for establishing trust and security. Standards like SPF, DKIM, and DMARC are technical safeguards that verify a sender's identity, effectively preventing domain spoofing and phishing attacks. These protocols are the bedrock of secure email communication best practices, as they signal to receiving mail servers that your messages are legitimate and trustworthy.
Why Authentication is Critical for Security and Deliverability
Email authentication acts as a digital passport for your domain, confirming to providers like Gmail and Microsoft that messages sent from your address are authorized. Without these records, your emails can be easily impersonated by malicious actors who can send phishing emails from your domain. A strong DMARC policy tells receiving servers to reject such fraudulent emails, protecting your brand reputation and your customers.
For instance, after implementing a strict DMARC policy, a financial services firm can prevent scammers from sending fraudulent invoices using its domain, protecting both its reputation and its clients. This is a foundational security measure for any organization. Learn more about how these protocols work together in our complete security guide to email authentication.
Key Insight: Email authentication transforms your domain's reputation from a question mark into an undeniable statement of legitimacy, directly improving security and deliverability.
Actionable Steps for Implementation
Configuring these protocols involves adding specific DNS records for your domain. Here’s how to get started:
- Start with an SPF Record: Create a TXT record in your DNS settings that lists all authorized mail servers for your domain. This tells receiving servers which IP addresses are permitted to send email on your behalf.
- Implement DKIM Signing: Enable DKIM within your email provider’s settings, like Typewire. This adds a unique digital signature to your emails, which receiving servers can verify using a public key published in your DNS.
- Deploy DMARC Gradually: Begin with a monitoring-only policy (
p=none). This allows you to receive reports on who is sending email from your domain without affecting mail flow. - Enforce Your DMARC Policy: Once you confirm all legitimate mail is authenticated, move to a
p=quarantinepolicy to send unverified emails to spam, and finally top=rejectto block them entirely.
8. Segment Email Lists for Privacy and Relevance
Sending generic, one-size-fits-all emails is one of the fastest ways to land in the spam folder. A core component of modern email communication best practices is segmentation—dividing subscribers into smaller groups. From a privacy perspective, this ensures you only send information relevant to a specific user group, adhering to the principle of data minimization and purpose limitation.
Why Segmentation is Crucial for Privacy and Security
Segmentation moves your email strategy from a broadcast to a secure, targeted conversation. Instead of sending sensitive information to your entire list, you can restrict it to only the relevant audience, reducing the risk of accidental data exposure. This targeted approach minimizes the likelihood of users marking your emails as spam, which is vital for maintaining a strong sender reputation.
For example, a SaaS company using a secure platform like Typewire can segment its users by account type. An email containing a security update relevant only to enterprise customers can be sent exclusively to that segment, preventing unnecessary notifications and potential confusion for other users. This ensures every communication is valuable and respects the recipient's context, reinforcing trust.
Key Insight: Segmentation is a privacy-enhancing tool. Sending relevant content reduces data exposure, builds trust, and protects your sender reputation.
Actionable Steps for Implementation
Implementing a powerful segmentation strategy is more accessible than it seems. Start with a few core groups and expand as you gather more data.
- Define Foundational Segments: Begin by grouping your audience based on clear, consent-based criteria. Common starting points include new subscribers (for welcome series) or product usage levels (for feature updates).
- Use Behavioral Triggers: Set up automated campaigns based on user actions within your application. Send a security tip to a user who just enabled a new feature. This real-time relevance is highly effective.
- Combine Criteria for Micro-Targeting: Create granular segments by combining multiple data points. For instance, target "administrators of enterprise accounts" for a specific security policy update.
- Regularly Clean Your Lists: Create a segment of inactive or unengaged subscribers. Send them a re-engagement campaign and remove those who don’t respond to keep your list healthy and minimize your data footprint.
9. Create Valuable Content that Reinforces Security
One of the most powerful email communication best practices involves shifting your focus from selling to serving, particularly by providing content that reinforces security and privacy awareness. Instead of sending purely promotional messages, you build trust by offering genuine value that also helps protect your users. This approach transforms your email into a welcome resource that strengthens your security posture.
Why Value-Driven Content Enhances Security
A value-first content strategy respects your subscribers' time and reinforces your commitment to their privacy and security. When your audience expects helpful security tips or privacy updates, they are more likely to engage with your messages and trust your brand. This positive engagement improves your sender reputation and ensures critical communications reliably reach the inbox.
For instance, a cybersecurity firm could send a weekly digest of emerging threats and protection tips, establishing itself as a trusted authority. Similarly, a hosted email provider like Typewire can educate users on enabling two-factor authentication or recognizing phishing attempts. This content model provides tangible value while actively contributing to a more secure ecosystem for your users.
Key Insight: Treat your subscribers' inbox as a privileged space. Earning your place there requires consistently delivering content that solves their problems, educates them, and helps keep them safe.
Actionable Steps for Implementation
Creating valuable, security-focused content is a systematic process. Use these tips to build a content strategy that serves your audience and strengthens your brand:
- Follow the 80/20 Rule: Dedicate 80% of your content to providing value—security education, privacy insights, or best practice guides—and reserve only 20% for direct promotional messages.
- Share Original Security Insights: Develop and distribute unique content like case studies on resolved security incidents (anonymized) or data-driven analyses of phishing trends.
- Tell Authentic Stories: Share lessons learned about security challenges and successes. Authentic storytelling builds a human connection and makes your security advice more relatable.
- Create Educational Content: Develop an email series that teaches users how to use your platform's security features. To streamline your messaging, explore these effective business email templates to structure your communications clearly.
10. Monitor Key Email Metrics and Continuously Test
To master a secure communication strategy, you must analyze performance. Monitoring key metrics and continuously testing different elements are essential email communication best practices that transform guesswork into a data-driven process. This allows you to systematically improve engagement and deliverability without compromising user privacy.
Why Data-Driven Optimization is a Privacy-Conscious Approach
A data-driven approach ensures your communication efforts are not wasted. By tracking metrics like open rates, click-through rates, and bounce rates within your own platform, you gain direct insight into audience behavior without sharing data with third-party trackers. Unlike ad-based platforms that track users across the web, your internal analytics focus solely on improving communication effectiveness within your secure environment.
For instance, A/B testing a subject line about a new security feature can reveal which wording encourages more users to adopt it. Analyzing bounce rates can help you identify list hygiene issues before they damage your sender reputation. A hosted platform like Typewire provides these analytics in a private environment, ensuring your optimization efforts do not come at the cost of user privacy.
Key Insight: Data-driven testing provides empirical evidence of what works. It replaces assumptions with facts, allowing you to optimize every element of your email for maximum impact and security.
Actionable Steps for Implementation
Implementing a testing framework is a powerful way to enhance your email strategy. Use these steps to build a continuous improvement cycle:
- Isolate a Single Variable: To get clear results, test only one element at a time (A/B testing). For example, test two different subject lines while keeping the email body and send time identical.
- Ensure Statistical Significance: Test with a large enough sample size to ensure your results are reliable. Most secure email platforms can help you determine the right audience size.
- Track Key Performance Indicators (KPIs): Monitor core metrics such as open rate and click-through rate (CTR). Also, track negative security indicators like hard bounces and spam complaints, which are critical for maintaining a healthy sender reputation. For a deeper dive, learn more about email deliverability best practices on typewire.com.
- Document and Iterate: Keep a record of your hypotheses, test results, and key learnings. This documentation becomes an invaluable playbook for creating more effective and secure email communications in the future.
10-Point Email Best Practices Comparison
| Strategy | 🔄 Implementation Complexity | ⚡ Resource Requirements | 📊 Expected Outcomes | 💡 Ideal Use Cases | ⭐ Key Advantages |
|---|---|---|---|---|---|
| Craft Clear and Compelling Subject Lines | Low — copywriting + A/B testing | Low — writer time, testing tool | Higher open rates; improved engagement | Announcements, promos, newsletters | Fast, measurable lift in opens |
| Personalize Email Content Beyond Name Insertion | High — data integration & dynamic logic | High — CRM/MA platform, data ops, privacy controls | Higher CTRs, conversion, LTV lift | E‑commerce, SaaS lifecycle, retention | Greatly increases relevance and revenue |
| Maintain Consistent Email Sending Schedule | Medium — editorial planning & cadence control | Medium — scheduling tools, content pipeline | Better deliverability; predictable engagement | Newsletters, daily/weekly digests, drip series | Builds trust and reduces spam flags |
| Implement Clear Call-to-Action (CTA) Buttons | Low–Medium — design + cross-client QA | Low — design assets, QA across clients | Higher click-through and conversion rates | Promotional offers, onboarding, product pages | Directs user action; reduces friction |
| Optimize Email Layout for Mobile Devices | High — responsive coding & extensive testing | Medium–High — developers, builders, testing tools | Improved mobile engagement and conversions | Mobile-first audiences, B2C, retail | Improves usability and accessibility on devices |
| Build and Maintain a Clean Email List | Medium — ongoing hygiene processes | Medium — validation tools, re-engagement workflows | Better deliverability; lower costs; accurate metrics | Any sender prioritizing deliverability | Protects sender reputation; increases ROI |
| Use Authentication Protocols (SPF, DKIM, DMARC) | High — DNS configuration + monitoring | Low–Medium — IT support, monitoring tools | Significantly improved deliverability and security | All bulk senders; brands facing spoofing risk | Prevents spoofing and improves inbox placement |
| Segment Email Lists for Targeted Campaigns | Medium–High — segmentation rules & maintenance | Medium — analytics, automation platform | Higher open/click rates; better conversions | E‑commerce, SaaS, targeted promotions | Enables highly relevant messaging and ROI lift |
| Create Valuable Content That Serves Subscribers | Medium–High — content strategy & production | High — writers, designers, editorial calendar | Stronger retention, shares, brand authority | Thought leadership, retention-focused newsletters | Builds trust and long-term engagement |
| Monitor Key Email Metrics and Continuously Test | Medium — analytics and test design | Medium — analytics tools, testing cadence | Incremental performance gains; data-driven choices | Any program seeking optimization at scale | Enables measurable, continual improvement |
Securing Your Digital Dialogue: The Way Forward
Navigating the landscape of digital communication requires more than just knowing how to compose a message. It demands a deliberate, security-first mindset. Throughout this guide, we've explored a comprehensive suite of email communication best practices, moving far beyond generic advice to provide actionable strategies that fortify your digital perimeter. We've deconstructed everything from the foundational necessity of authentication protocols like SPF, DKIM, and DMARC to the privacy-enhancing benefits of list segmentation. Each practice, whether technical or strategic, serves as a crucial building block in constructing a resilient and effective email framework.
The central theme is clear: true mastery of email communication hinges on a commitment to privacy and security. It's about recognizing that a clean email list is as vital to your security posture as a strong password policy. It’s understanding that a mobile-optimized layout isn't just about aesthetics; it's about preventing user error that can lead to security breaches. These are not isolated tasks to check off a list but interconnected components of a holistic communication strategy built on a secure, hosted email platform.
From Theory to Action: Your Next Steps
The value of these principles lies in their application. Merely understanding the importance of DMARC or list segmentation is not enough. The real transformation begins when you translate this knowledge into tangible action. Your immediate priority should be to conduct a thorough audit of your current email practices against the security and privacy benchmarks outlined in this article.
Here is a simple, actionable plan to get you started:
- Technical Audit: Begin with the non-negotiables. Verify your domain’s SPF, DKIM, and DMARC records immediately. These are not advanced features but the fundamental price of entry for secure, deliverable email in the modern era. Use online tools to check your configuration and address any gaps.
- Platform Review: If you are not already using a hosted email platform, evaluate your options. Prioritize providers that offer end-to-end encryption, own their infrastructure, and have a clear, privacy-focused business model.
- List Hygiene Protocol: Commit to a regular schedule for cleaning your email list. Don't wait until your bounce rates skyrocket. Establish a process for removing inactive subscribers and verifying new ones to maintain both high deliverability and compliance with privacy standards.
The Lasting Impact of a Security-First Approach
Adopting these email communication best practices yields benefits that extend far beyond improved open rates. When you prioritize security and privacy, you build trust. Your subscribers, clients, and team members learn that communication from you is legitimate, safe, and respectful of their data. This trust is the bedrock of strong professional relationships and a reputable brand identity.
By embracing a secure, hosted email platform as your foundation, you empower yourself to implement these practices effectively. You move away from consumer-grade services that mine your data and into an environment where you control the security settings, manage users with precision, and communicate with the confidence that your conversations remain private. This isn't just about sending better emails; it's about building a better, more secure, and more professional way to communicate. The journey requires commitment, but the rewards of a secure, private, and powerful digital dialogue are well worth the effort.
Ready to build your communication on a foundation of privacy and security? Typewire provides the secure, ad-free hosted email platform you need to implement these best practices with confidence. Take control of your data and elevate your professional communications by exploring our private email solutions at Typewire today.