Why Your Privacy Demands Encrypted Email

Email remains a cornerstone of communication. However, standard emails offer minimal privacy. They're akin to postcards, easily read by anyone handling them. This leaves your sensitive information vulnerable to prying eyes and cyberattacks. Understanding encrypted email is now vital for protecting your privacy.
The Risks of Unprotected Email
Sending sensitive information via unencrypted email is risky. Without encryption, your messages are open to interception. This includes personal conversations, financial details, business documents, and intellectual property. A competitor could access your strategic plans, or a hacker could steal your login credentials.
The sheer volume of email traffic also presents a tempting target for cybercriminals. The growing use of email for personal and professional matters, combined with the rise of e-commerce, exacerbates this risk. In 2025, there were 4.83 billion email users globally. This figure is projected to climb to 5.61 billion by 2030. Daily email traffic is expected to surge from 392 billion to 523 billion emails between 2025 and 2030. This massive volume underscores the need for robust email security. For more detailed statistics, see the Email Encryption Global Strategic Business Report.
The Benefits of Encryption
Email encryption safeguards your messages. It acts like a digital lock and key, scrambling your data so only the recipient with the correct key can decrypt it. This prevents unauthorized access, even if the email is intercepted. This is particularly critical for protecting confidential data.
- Financial Data: Bank account details, credit card numbers, and investment information.
- Medical Records: Health history, diagnoses, and treatment plans.
- Legal Documents: Contracts, agreements, and sensitive correspondence.
- Business Secrets: Proprietary information, strategic plans, and research data.
Compliance and Encryption
Many industries now require encryption to comply with data privacy regulations. These regulations mandate the protection of sensitive customer data, and email encryption is essential for compliance. Failure to meet these requirements can result in hefty fines and reputational damage. Sending an encrypted email is not just good practice; it's often a legal obligation. This growing need for secure communication makes encryption a critical step in safeguarding your privacy and ensuring compliance.
Encryption Fundamentals: What You Actually Need to Know
This section breaks down encryption into easy-to-understand concepts. We'll explain core ideas like public and private keys, end-to-end encryption, and digital signatures, using insights from security professionals. Grasping these basics is essential for sending encrypted emails effectively.
Public and Private Keys: How They Work
Think of a mailbox with two slots: one for incoming mail (public key) and one for outgoing mail (private key). Anyone can drop a letter into the incoming slot, but only the person with the unique outgoing key can open the mailbox and read the letters.
In the same way, with public key cryptography, anyone can encrypt a message using your public key. However, only you can decrypt it using your private key. This system ensures that even if someone intercepts the message, only the intended recipient can read it.
End-to-End Encryption: Full Message Protection
End-to-end encryption (E2EE) adds an extra layer of security. Imagine sealing the letter in an envelope before placing it in the mailbox. The message is encrypted on the sender's device and stays encrypted until it reaches the recipient's device. This means no one, not even the email provider, can read the message during transmission.
Digital Signatures: Ensuring Authenticity
Digital signatures act like a wax seal on a letter, verifying its origin. They use your private key to generate a unique digital fingerprint attached to the message. The recipient uses your public key to verify the signature, confirming the message is truly from you and hasn't been altered.
Content vs. Transport Encryption: Double the Security
It's important to understand the difference between content encryption and transport encryption. Transport encryption secures the connection between email servers, like protecting a mail truck from being hijacked. However, the message itself might still be readable on the server. Content encryption, conversely, encrypts the message itself. This ensures only the recipient can read it, even if the connection is compromised. Using both methods provides comprehensive protection. For more information on securing your data, check out these data privacy best practices.
The Increasing Importance of Encryption
Our growing reliance on digital communication, coupled with stricter data protection regulations, is fueling the email encryption market's expansion. The global email encryption market was valued at $6.4 billion in 2025 and is projected to reach $31.1 billion by 2034. This highlights the growing need to send encrypted emails. You can learn more about this growth in the email encryption market. The escalating threat of cyberattacks further emphasizes the need for strong security measures like E2EE and cloud-based encryption solutions.
Finding Your Perfect Encryption Solution
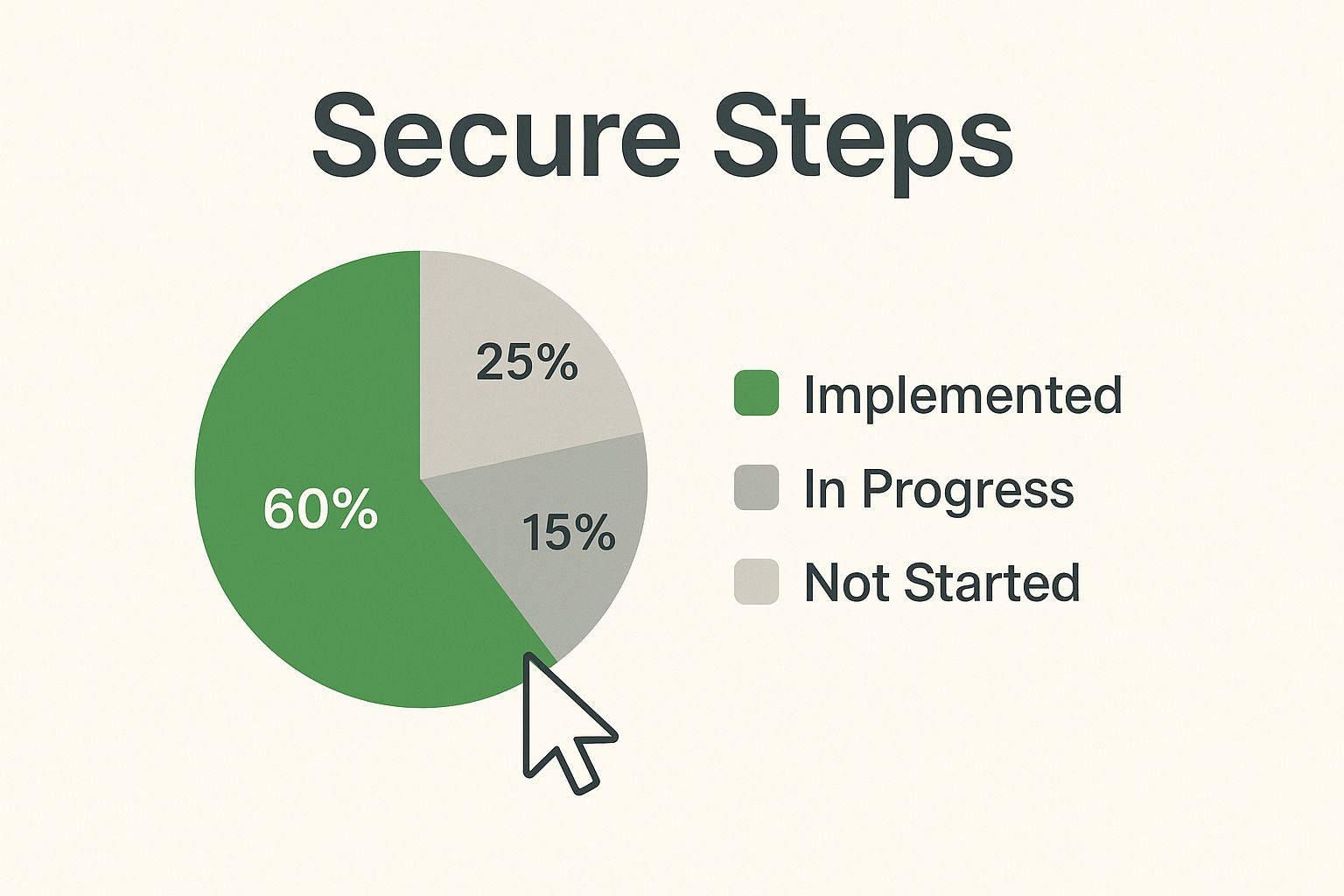
The infographic above illustrates how simple sending an encrypted email can be. With a focus on "Secure Steps," it visually represents the process, emphasizing the ease and accessibility of secure communication with just a click of a button. The lock icon provides visual reassurance, effectively communicating that encrypted email is a straightforward process.
Finding the right encryption solution depends on your specific needs and technical comfort. A large corporation and an individual user likely have very different requirements. For example, a dedicated secure email provider offers a complete platform with robust security but often comes with a higher price tag.
Browser extensions like Mailvelope offer a free and user-friendly alternative for encrypting emails through existing webmail services like Gmail. For further insights on pricing strategies, you can check out this article: How to master pricing decisions. Email plugins offer another option, integrating with your current email client for added convenience.
Evaluating Your Options
Choosing the right encryption tool hinges on several factors: ease of use, compatibility with existing systems, the strength of its encryption, and overall cost. Some tools prioritize a simple user experience, while others offer advanced features and customization options.
-
Dedicated Secure Email Providers: Offer comprehensive security but can be more expensive.
-
Browser Extensions: Free and user-friendly, but may have limited features.
-
Email Plugins: Integrate with your current email client, offering a balance of convenience and security.
Key Features To Consider
When evaluating encryption tools, prioritize key features like strong encryption protocols, effective key management, and easy mobile access. Balancing robust security with user-friendliness is essential, especially for team implementation.
-
Key Management: Consider how easy it is to generate, store, and manage encryption keys.
-
Attachment Encryption: Ensure the solution encrypts both the email body and any attachments.
-
Mobile Access: Check for a user-friendly mobile app or a responsive web interface for access on the go.
Free Vs. Premium: Where To Invest
Free encryption solutions often provide adequate protection for individual users. However, businesses or organizations handling sensitive data may require the advanced features and dedicated support offered by premium services. This support becomes invaluable if technical issues arise.
To help you make an informed decision, here's a comparison of free and premium encryption options:
Encryption Tools Compared: Real-World Performance
This comparison reveals how today's top encryption solutions perform across security strength, user experience, and practical implementation factors.
| Tool/Service | Encryption Type | Ease of Setup | Free Version | Premium Cost | Compatibility | Best For |
|---|---|---|---|---|---|---|
| Mailvelope | PGP | Easy | Yes | N/A | Chrome, Firefox, Edge | Individuals, casual users |
| ProtonMail | End-to-end | Easy | Yes, limited | Paid plans available | Web, Mobile apps | Privacy-conscious users, businesses |
| Tutanota | End-to-end | Easy | Yes, limited | Paid plans available | Web, Mobile apps | Security-focused users, businesses |
This table highlights the key differences between popular encryption solutions, showcasing the varied options available for distinct needs. While free options are suitable for basic encryption, premium services provide enhanced security and support for sensitive data.
Enhance your email security further by implementing two-factor authentication (2FA). This adds an extra layer of protection, preventing unauthorized access even if your password is compromised. The ideal encryption solution depends on your specific security requirements, budget, and technical expertise. By carefully considering these factors and evaluating available options, you can confidently choose the right tool to protect your email communications.
How to Send an Encrypted Email Across Any Platform
Sending an encrypted email is simpler than you might imagine. This guide provides practical steps for encrypting your emails on various platforms, from common webmail services like Gmail and Outlook to dedicated secure email providers. Whether you're new to encryption or a seasoned pro, these instructions will help you safeguard your sensitive data.
Encrypting With Gmail
Gmail offers built-in options for sending encrypted emails. While not end-to-end encrypted by default, you can boost security with browser extensions like Mailvelope.
- Install Mailvelope: Add the Mailvelope extension to your Chrome browser.
- Generate Keys: Create your public and private keys using Mailvelope.
- Compose and Encrypt: Write and encrypt your message in the Mailvelope compose window using the recipient's public key.
- Send Securely: The recipient can then decrypt the message using their private key.
This makes it straightforward to send encrypted email to both Gmail and non-Gmail users.
Encrypting With Outlook
Outlook supports encryption, primarily through S/MIME. This requires a bit more setup but offers robust security.
- Obtain a Digital Certificate: You'll need a digital certificate from a trusted Certificate Authority (CA).
- Configure S/MIME in Outlook: Set up S/MIME in your Outlook settings, linking it to your digital certificate.
- Compose and Encrypt: Select the encryption option when sending an email to protect it with S/MIME.
- Decrypting: Recipients will also need S/MIME configured or compatible software to decrypt the message.
While slightly more technical, S/MIME provides solid email encryption within Outlook.
Using Secure Email Providers
Services like Typewire, ProtonMail, and Tutanota offer built-in end-to-end encryption, simplifying the process considerably.
- Choose a Provider: Select a provider that meets your security needs and budget. Typewire, for example, offers various plans.
- Create an Account: Set up an account with your chosen provider.
- Compose and Send: Create and send emails as usual. The encryption and decryption are handled automatically.
This provides a streamlined way to manage secure communications.
Encrypting on Mobile Devices
Protecting your emails on mobile is essential. Most secure email providers offer dedicated mobile apps with integrated encryption.
- Download the App: Install your provider's app on your phone or tablet.
- Log In: Sign in to your account on the app.
- Send and Receive Securely: Send and receive encrypted messages seamlessly within the app.
This ensures secure email access even when you're on the move.
Verifying Your Encryption
After setting up encryption, it's crucial to confirm it's working correctly.
-
Check for Visual Indicators: Watch for lock icons or other visual cues within your email client or provider’s interface. This usually signals successful encryption.
-
Test with a Trusted Contact: Send a test encrypted email to a trusted contact to ensure they can decrypt and read it without issues.
-
Review Message Headers: Examining message headers can offer technical details about the applied encryption.
Troubleshooting Encryption Issues
Occasionally, problems can arise with encryption.
- Compatibility Problems: Recipients may lack the necessary software or settings to decrypt messages. Providing clear instructions or alternative secure methods can be helpful.
- Key Management Errors: Lost or damaged keys can prevent decryption. Maintaining secure key backups is essential.
Addressing these potential issues will enhance your encrypted email experience. The optimal method depends on your technical comfort level, budget, and specific security requirements. Exploring these options will allow you to integrate email encryption effectively into your communications. For business-focused secure email information, Typewire’s business plans may be a valuable resource.
Encryption Habits That Actually Stick

Knowing how to send an encrypted email is only the first step. Truly securing your communications depends on building consistent encryption habits. This section explores practical and sustainable habits for maintaining your privacy over time, incorporating insights from security professionals and experienced users. For businesses seeking secure email solutions, consider exploring Typewire's business plans.
Mastering Password Management for Encryption
Strong passwords form the foundation of secure encryption. A weak or easily guessed password can compromise your entire system. Using robust, unique passwords for your email accounts and encryption keys is therefore critical.
-
Use a Password Manager: Password managers generate and securely store complex passwords, eliminating the need to remember them all.
-
Enable Two-Factor Authentication (2FA): 2FA adds an extra layer of security. It requires a second verification method—such as a code sent to your phone—in addition to your password.
-
Regularly Update Passwords: Change your passwords frequently, especially for accounts handling sensitive information.
These practices are essential for maintaining strong security.
Effective Key Storage and Rotation
Properly managing your encryption keys is vital. Losing your private key can make encrypted messages inaccessible. Similarly, infrequent key rotation increases vulnerability to compromise.
-
Secure Key Storage: Store private keys securely, such as in a password manager or on a dedicated hardware security key.
-
Key Rotation: Rotate your encryption keys on a regular basis. This limits potential damage if a key becomes compromised.
-
Back Up Your Keys: Create secure backups of your keys in case of loss or damage. Store these backups separately from your primary key storage location.
These practices help ensure your keys remain secure and effective.
Deciding When to Encrypt
Not all emails require encryption. Over-encrypting can disrupt workflow and frustrate recipients. Developing a clear protocol for when to encrypt is therefore essential.
-
Sensitivity of Information: Encrypt emails containing sensitive data, including financial details, medical records, or confidential business documents.
-
Recipient's Security Practices: Consider the recipient's security practices. If they are unfamiliar with encryption or lack the necessary tools, explore alternative secure methods.
-
Legal and Regulatory Requirements: Be aware of legal or regulatory requirements for encrypting specific types of information.
This helps streamline your workflow and focus encryption efforts where they are most needed.
Educating Your Recipients
Introducing recipients to encrypted email can be challenging. Many are unfamiliar with the process. However, clear communication can simplify things and encourage adoption.
-
Provide Clear Instructions: Give simple, step-by-step instructions for decrypting messages.
-
Offer Alternative Methods: If recipients struggle with traditional encryption, consider secure file-sharing options.
-
Explain the Benefits: Emphasize the importance of encryption for protecting sensitive information and building trust.
By addressing these challenges proactively, you can foster a secure communication environment. These habits shift encryption from a technical process to a sustainable practice, providing long-term protection for your sensitive data. Learn more about effective security strategies in our article, how to master….
Overcoming Real-World Encryption Challenges
Even with robust tools, sending an encrypted email isn't always straightforward. Practical challenges can hinder your security efforts. This section offers solutions to common obstacles, ensuring your encrypted email practices remain effective.
Compatibility Issues: Bridging Different Email Systems
One common hurdle is compatibility. Not all email systems support the same encryption methods. Sending an encrypted email to someone using a different system can lead to decryption issues. For example, if you are using PGP encryption Pretty Good Privacy and the recipient's email client doesn't support it, they will not be able to read your message.
-
Communicate with Recipients: Discuss encryption methods beforehand. This ensures they have compatible software.
-
Provide Clear Instructions: Offer step-by-step guides for decrypting messages, tailored to their email client.
-
Consider Alternative Solutions: If compatibility proves insurmountable, explore secure file-sharing services as a backup.
These steps mitigate frustration and maintain secure communication flow.
Key Management Across Multiple Devices
Managing encryption keys across multiple devices presents another challenge. Losing a private key renders corresponding encrypted emails unreadable. Additionally, using the same key across all devices increases the risk of compromise.
-
Use a Password Manager: Store your private keys securely in a password manager. This simplifies management and facilitates secure access across devices.
-
Consider Hardware Security Keys: Hardware security keys offer an extra layer of protection for your keys, shielding them from software vulnerabilities.
-
Implement Key Rotation: Periodically change your encryption keys. This limits the potential impact of any single key compromise.
This simplifies key management while maintaining robust security.
Balancing Security With Workflow Efficiency
Strong encryption can sometimes feel cumbersome, impacting workflow efficiency. Finding the right balance between security and usability is key to sustained encryption practices.
-
Automate Where Possible: Utilize email clients or extensions that automate encryption and decryption. This minimizes manual steps. For example, using extensions like Mailvelope for Gmail simplifies key management.
-
Integrate with Existing Tools: Choose encryption solutions that integrate seamlessly with your current email client. Avoid standalone applications that create extra steps.
-
Train Your Team: Invest in training for team members on sending and receiving encrypted emails and handling the complexities of public and private keys.
This allows you to maintain security without sacrificing productivity.
To help illustrate common encryption roadblocks and their solutions, let's look at the following table:
Encryption Roadblocks and Proven Solutions
This table outlines the most common obstacles users face when implementing email encryption and provides field-tested solutions for each challenge.
| Problem | Cause | Solution | Prevention Tips |
|---|---|---|---|
| Decryption Failure | Recipient's email system lacks support for the sender's encryption method. | Communicate with recipients beforehand to ensure compatible software or explore alternative secure file-sharing services. | Discuss encryption methods with recipients in advance and offer clear decryption instructions. |
| Lost Encryption Keys | Misplaced or forgotten private keys. | Securely store private keys in a password manager or on a hardware security key. | Implement key rotation and use strong, unique passphrases for key protection. |
| Cumbersome Encryption Process | Manual encryption/decryption steps slow down workflow. | Use email clients/extensions that automate these processes and integrate with existing tools. | Train your team on efficient encryption practices. |
| Mobile Encryption Challenges | Limited screen space and varying operating systems complicate key management and decryption. | Choose mobile-friendly solutions, simplify key management with password manager apps, and consider cloud-based key storage. | Opt for encryption providers with dedicated mobile apps and streamline key access on mobile devices. |
| Inconsistent Team Practices | Lack of clear guidelines for when and how to use encryption within the team. | Establish and document clear encryption protocols and provide thorough training. | Develop and communicate team-wide encryption best practices and ensure everyone understands key exchange methods. |
This table summarizes practical solutions and preventative measures to address common encryption challenges.
Team Communication and Encryption Practices
Managing encrypted communications within a team requires careful planning and coordination. Ensuring consistent practices and addressing individual needs are crucial.
-
Establish Clear Encryption Protocols: Develop and document clear guidelines for when and how to use encryption within the team.
-
Provide Training and Support: Offer comprehensive training to all team members on encryption best practices.
-
Facilitate Key Exchange: Implement secure methods for team members to share public keys with each other.
This creates a collaborative and secure communication environment.
By anticipating and addressing these practical challenges, you can establish resilient encryption practices that genuinely protect your email communications. For additional insights into secure email practices, especially for businesses, explore Typewire's robust features. They offer solutions designed to integrate seamlessly with your current workflow.
The Evolution of Email Privacy: What's Next
Privacy technologies are constantly changing. This begs the question: how will these changes affect your current email encryption strategy? By understanding the future of secure communication, you can make informed decisions about your current encryption investments and adapt to the challenges ahead. You might be interested in learning more about the platform Typewire.
Quantum Computing: A New Era of Encryption
The rise of quantum computing presents both a risk and an opportunity for email encryption. Quantum computers could potentially break current encryption algorithms, making them obsolete. However, they also open doors to new, quantum-resistant encryption methods.
This means that while established methods like RSA and ECC (Elliptic Curve Cryptography) might become vulnerable, new algorithms designed to resist quantum attacks are being developed. Staying up-to-date on these advancements is critical for ensuring your email security in the future.
AI and The Future of Email Security
Artificial intelligence (AI) is becoming increasingly important in both offensive and defensive cybersecurity. AI can be used to create more advanced phishing attacks. At the same time, AI is also being employed to create more intelligent anti-spam and anti-phishing filters.
This constant arms race highlights the need for adaptive security measures that can keep pace with these developing technologies.
Regulatory Changes: Adapting to New Standards
Data privacy regulations are becoming more and more demanding. These regulations often require the use of encryption for sensitive data, making robust email encryption essential for compliance.
Staying informed about these regulatory changes and adapting your encryption strategies is vital to avoid penalties and maintain a strong security posture. For instance, implementing client-side encryption in platforms like Gmail gives companies more control over their encryption keys. This helps meet regulatory requirements by keeping sensitive data encrypted and under the customer’s control.
Staying ahead of these developments is critical for effective email encryption. Adapting your strategy as standards evolve ensures your private information remains protected. Explore how Typewire prepares you for the future of email privacy.




