In today's data-driven environment, email is more than a communication tool; it's a vast, searchable archive of your most sensitive information. Left unmanaged, this archive becomes a significant liability, exposing you to privacy breaches, legal risks, and security threats. A well-crafted email retention policy is no longer an optional IT task but a foundational element of modern data governance and a crucial security measure. It's about systematically controlling what you keep, for how long, and why, turning a potential vulnerability into a structured, defensible asset.
This guide moves beyond generic advice to provide a detailed roundup of 10 essential email retention policy best practices, with a specific focus on the critical intersection of privacy, security, and the unique challenges of hosted email platforms. We will explore actionable strategies designed to protect your data, ensure compliance with Canadian regulations like the Personal Information Protection and Electronic Documents Act (PIPEDA), and empower you to take definitive control of your digital communications.
By implementing these practices, you can minimise your attack surface, reduce storage costs, and simplify legal discovery processes. Whether you are a privacy-conscious individual, a small business owner utilising a hosted email service, or an IT professional managing corporate infrastructure, the insights in this article will help you build a secure, compliant, and efficient email management framework. You will learn precisely how to define retention schedules, implement automated controls, handle legal holds, and train users effectively, creating a robust policy that truly protects your organisation.
1. Establish Clear Retention Schedules Based on Regulatory Requirements
The foundation of any effective email retention policy is a set of clear, documented retention schedules. These schedules are not arbitrary; they are precise timelines dictating how long different categories of email communications must be stored to satisfy legal, regulatory, and operational requirements. Creating these schedules is a critical first step in balancing compliance obligations with data minimisation principles, which is a core tenet of modern data privacy.
A well-defined schedule ensures your organisation retains crucial information for the required duration, protecting you from penalties and legal challenges. At the same time, it mandates the timely and defensible disposal of data that is no longer needed. This systematic deletion reduces storage costs, minimises your data breach attack surface, and lowers the risk associated with holding onto sensitive information indefinitely, directly enhancing your email security and privacy posture.
Practical Implementation Examples
- Financial Services: A brokerage firm in Ontario must retain client transaction confirmations and advisory communications for seven years to comply with IIROC (Investment Industry Regulatory Organization of Canada) rules.
- Healthcare Providers: A clinic in Alberta must maintain patient-related email communications for a period defined by provincial health information acts, often 10 years or more past the last patient interaction.
- Legal Practices: A law firm handling litigation must preserve all client emails related to an active case under a legal hold, superseding standard retention periods until the matter is fully resolved.
Actionable Tips for Implementation
To create robust and compliant retention schedules, follow these key steps:
- Conduct a Data Audit: Before defining rules, you must understand what you have. Audit your current email archives to categorise existing content, identify data types (e.g., contracts, HR records, client communications), and map data locations.
- Consult Legal and Compliance Experts: Retention periods are dictated by complex laws. Work with legal counsel to identify all applicable regulations for your industry and jurisdiction, including privacy laws like PIPEDA. You can learn more about Canadian data privacy laws here to get started.
- Document and Distribute: Formalise your retention schedules in a written policy. This document should be easily accessible to all employees and integrated into staff training programs.
- Automate and Integrate: To ensure your email retention schedules meet strict regulatory requirements and integrate smoothly with compliance tools, consider solutions like GDPR compliant HR software with Microsoft Purview integration which can help automate policy enforcement across your organisation's data ecosystem.
- Schedule Regular Reviews: Laws and business needs change. Review and update your retention schedules at least annually, or whenever significant regulatory changes occur.
2. Implement Automated Deletion Policies with Safeguards
Relying on manual deletion is inefficient and prone to human error, creating significant compliance and email privacy risks. Implementing automated deletion policies is a cornerstone of modern email retention policy best practices. This approach uses rule-based systems within your hosted email platform to systematically and defensibly dispose of emails once their defined retention period expires, ensuring consistent policy enforcement without manual intervention.
By automating the process, your organisation can drastically reduce data liability, lower storage costs, and minimise its digital footprint. This is especially crucial for email security and privacy, as it ensures that sensitive data isn't kept longer than necessary, thereby reducing the potential impact of a data breach. Automation turns your retention schedule from a passive document into an active, enforceable control.
Practical Implementation Examples
- Marketing Teams: Automatically delete promotional email chains and campaign planning messages after 90 days to keep mailboxes clean and focused on current initiatives.
- HR Departments: Systematically archive recruitment-related emails (e.g., resumes, interview notes) for a set period after a hiring decision is finalised to comply with employment regulations, then delete them.
- Support Teams: Configure helpdesk systems to auto-purge resolved customer ticket correspondence after two years, balancing the need for historical context with data minimisation principles.
- Finance Departments: Set a rule to delete transitory financial documents like draft invoices and internal planning memos after 180 days, while retaining official records according to longer-term schedules.
Actionable Tips for Implementation
To implement automated deletion safely and effectively, follow these critical steps:
- Start with Low-Risk Categories: Begin your rollout with non-critical email categories, such as newsletters, automated system alerts, or junk mail, to test and refine the process before applying it to more sensitive data.
- Implement Litigation Hold Capabilities: Your system must have a robust legal hold function that can override any automated deletion rule. This is essential to preserve evidence during legal proceedings or investigations.
- Test Rules in a Staging Environment: Never deploy a new deletion rule directly into production. First, test it thoroughly in a staging or sandboxed environment using sample data to confirm it functions as expected and doesn't cause unintended data loss.
- Maintain Detailed Audit Logs: Ensure your email platform or archiving solution maintains a comprehensive, immutable audit log of all automated deletions. This log is crucial for demonstrating compliance and defensible disposal.
- Educate Users on Timelines: Communicate clearly with staff about the new auto-deletion timelines. Proper training ensures they understand when and how to manually archive any specific emails that fall outside standard categories but are vital for business operations.
3. Separate Personal and Business Email for Retention Purposes
A fundamental practice for effective and privacy-conscious email management is to maintain a strict separation between business and personal communications. Blurring these lines on a hosted email platform creates significant compliance risks, as personal emails can inadvertently become subject to business retention rules, legal holds, or eDiscovery requests. This over-retention of personal data not only infringes on employee privacy but also unnecessarily expands your organisation's data footprint and attack surface.
By establishing a clear policy that designates company-provided accounts exclusively for business use, you simplify the application of your email retention policy. This ensures that only relevant business records are archived, retained, and eventually disposed of according to your defined schedules. This separation is a critical component of a robust data governance framework, protecting both the organisation from legal entanglements and employees from undue privacy intrusions.
Practical Implementation Examples
- Freelancers and Consultants: A freelance graphic designer uses a custom domain email (e.g., clientA@designbyjane.ca) for each major client project, keeping all project-related correspondence separate from their personal Gmail account used for non-work matters.
- Small Business Operations: A local bakery uses a company-wide email system for all official orders, supplier communications, and staff scheduling, while employees use their personal accounts for private conversations, ensuring personal chats are not captured in business archives.
- Remote Teams: A distributed software company provides each team member with a business email alias specifically for project-related collaboration, while personal communications are explicitly kept on separate, non-company platforms.
Actionable Tips for Implementation
To successfully enforce the separation of personal and business email, follow these key steps:
- Establish a Clear Policy: Draft and circulate a formal policy defining what constitutes "business" versus "personal" communication. Clearly state that company email systems are for business purposes only and that employees should have no expectation of privacy for communications on these platforms.
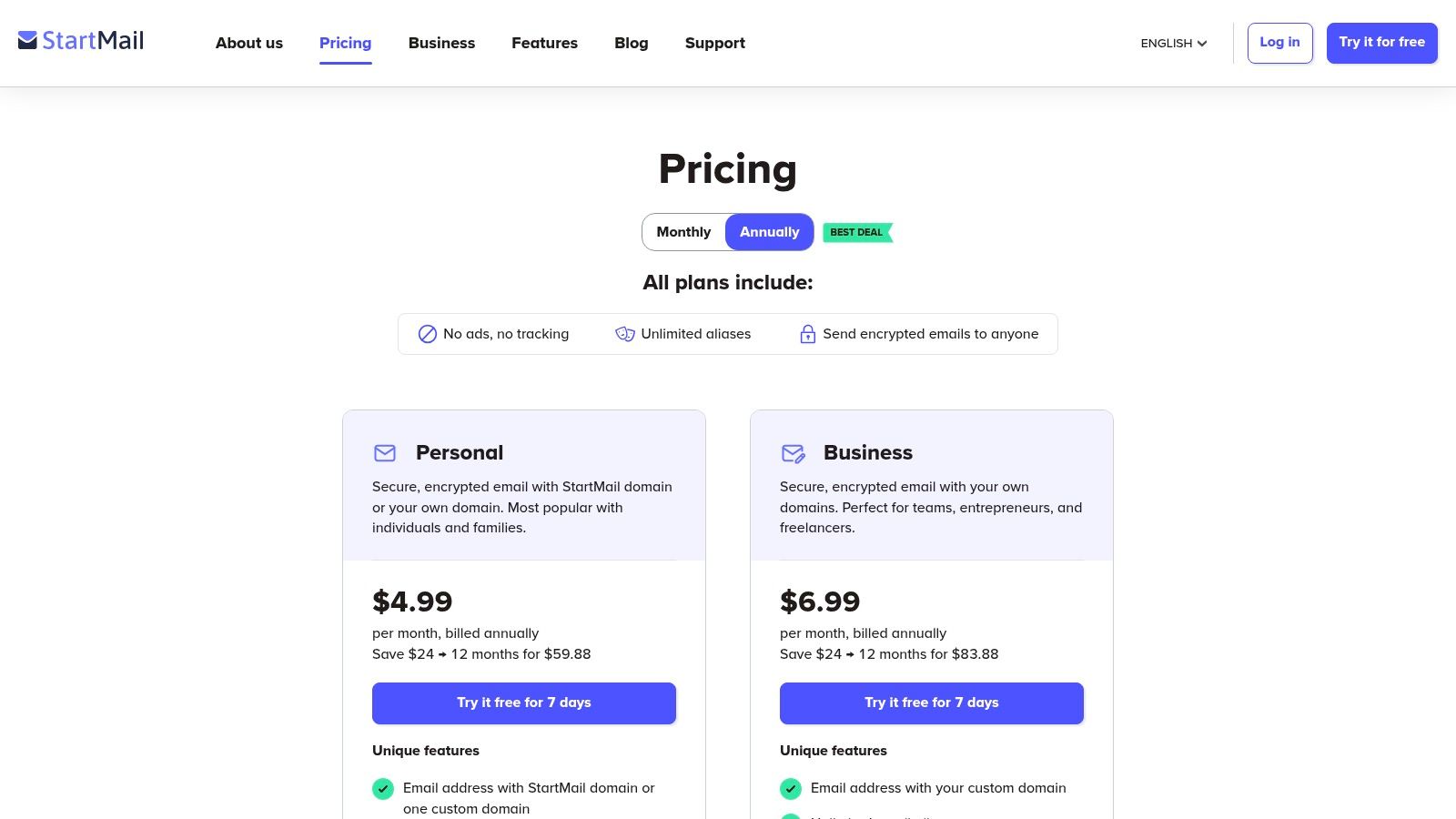
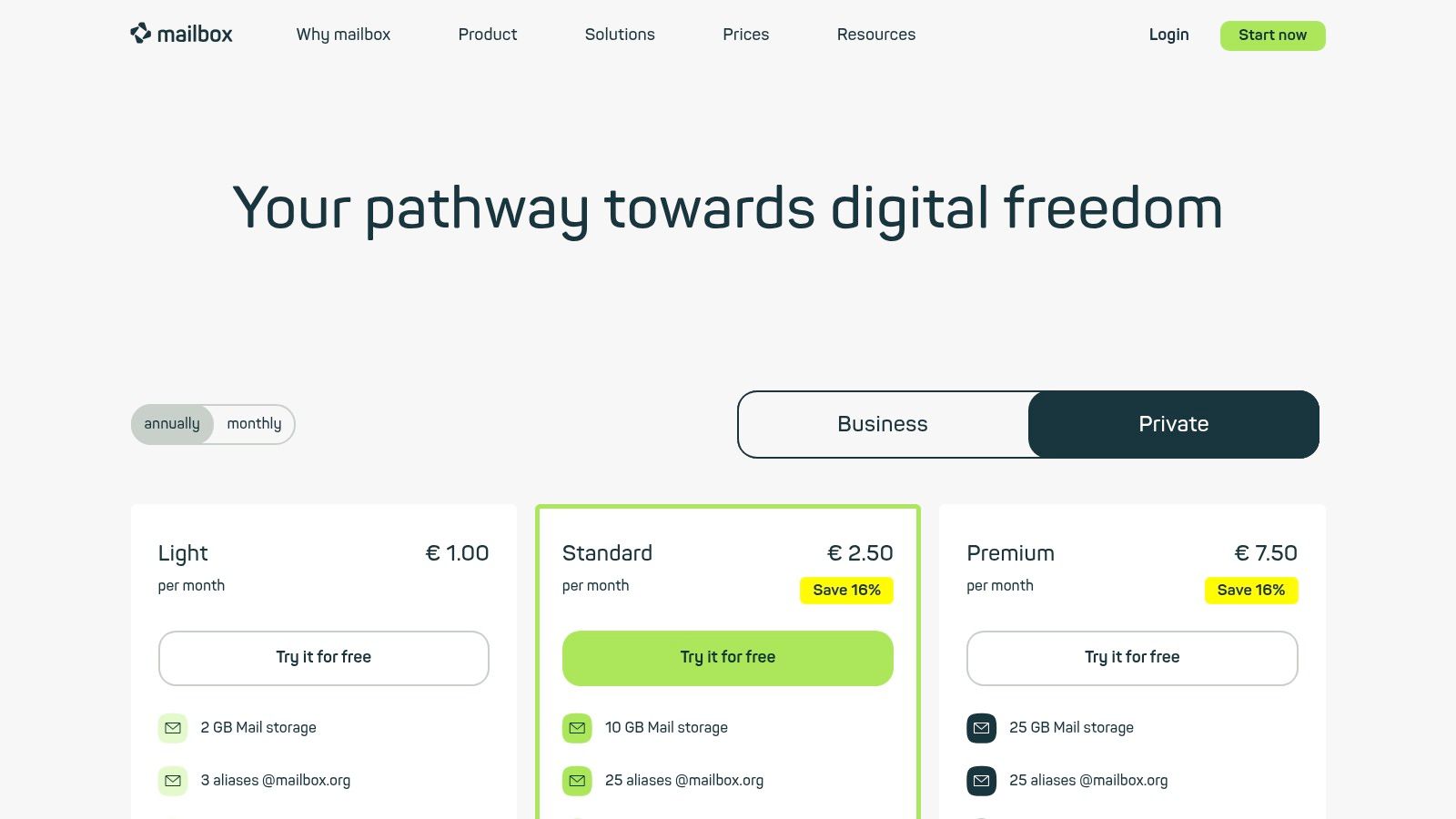
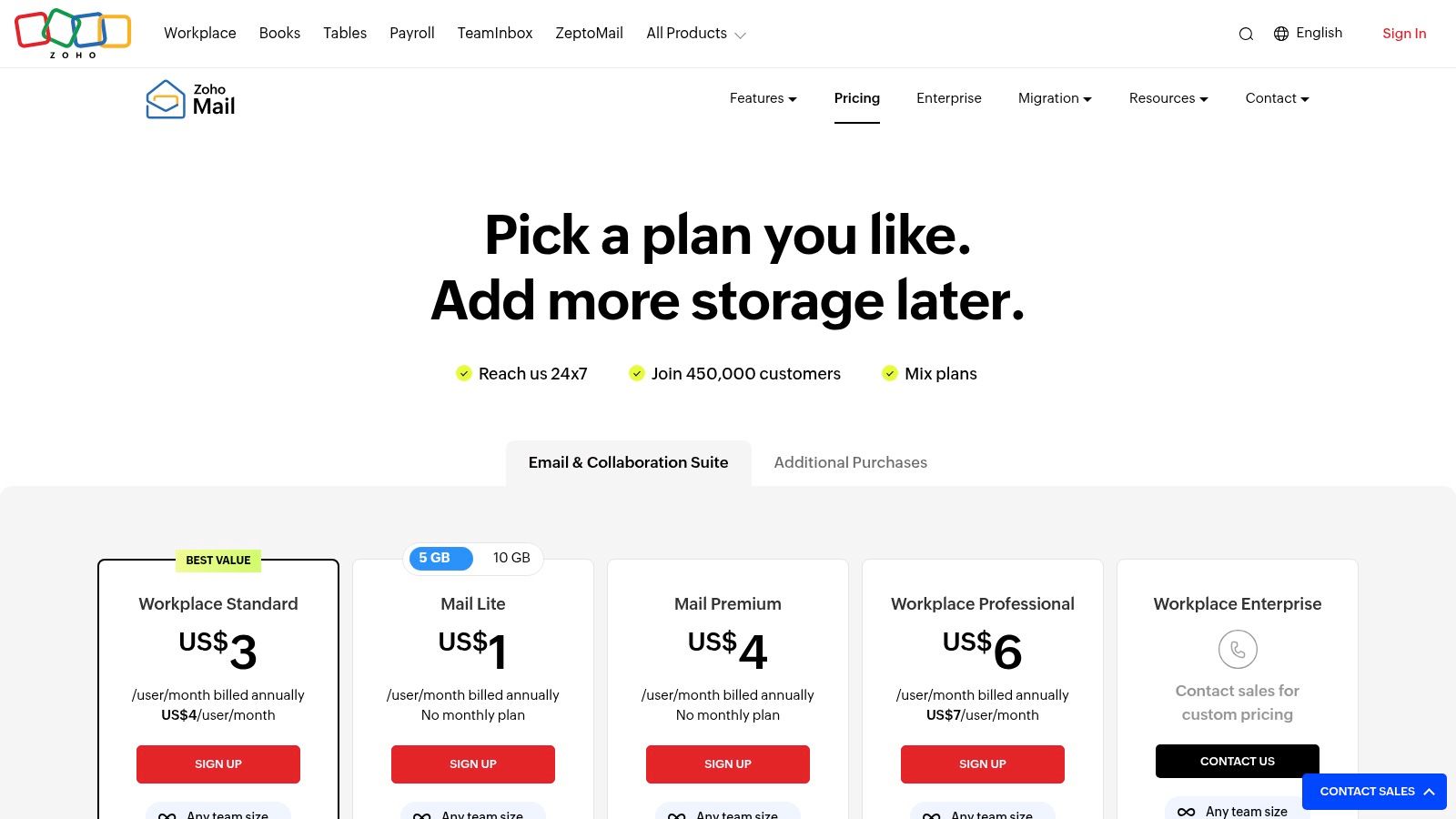
- Leverage Custom Domains: Use a hosted email platform with custom domains for all official business communications. This reinforces professionalism and makes it easy to apply organisation-wide retention and security policies.
- Implement Smart Filtering: Encourage employees to use inbox rules and filters to automatically sort and organise communications, although the primary goal should be to prevent personal emails from arriving in business inboxes in the first place.
- Provide Comprehensive Training: Integrate email separation expectations into employee handbooks and conduct mandatory training during onboarding. You can learn more about the security implications of mixing business and personal email here to enhance your training materials.
- Conduct Periodic Audits: Perform occasional, policy-driven audits of email usage to ensure the separation is being maintained, reinforcing the importance of the policy and identifying areas for further training.
4. Utilize Advanced Search and Categorization for Efficient Retention Management
A modern email retention policy is more than just a set of timelines; it requires the technical capability to find, classify, and act on specific data efficiently. Utilizing advanced search and categorization features within your hosted email platform transforms retention management from a daunting manual task into a precise, automated process. This capability is essential for applying nuanced policies, responding to legal requests, and ensuring data privacy is respected throughout its lifecycle.
By leveraging tools like full-text search, labels, and sophisticated filters, administrators can quickly isolate specific datasets based on content, sender, date, or other metadata. This granular control allows for the consistent application of retention rules, reducing the risk of human error and significantly cutting down the time spent on manual review. This approach is fundamental to creating an agile and defensible email management strategy that supports both compliance and operational efficiency.
Practical Implementation Examples
- Human Resources: An HR team can create a saved search for all communications containing the term "severance agreement" to automatically apply a specific, longer-term retention rule distinct from general employee correspondence.
- Finance Departments: Using advanced date-range and keyword searches, a finance team can easily isolate all emails related to a specific fiscal year for year-end auditing and subsequent archiving according to financial regulations.
- Legal and Compliance: In response to a subject access request under PIPEDA, a compliance officer can use advanced queries to locate all emails pertaining to a specific individual across the entire organisation, ensuring a complete and timely response.
Actionable Tips for Implementation
To effectively integrate search and categorization into your email retention policy, follow these steps:
- Establish Naming Conventions: Create and enforce a clear, organisation-wide standard for folder structures and email labels (e.g.,
[ProjectName]-Contracts,HR-Recruitment). This structural consistency is foundational to effective searching. - Create Saved Searches: Build a library of saved search queries for common retention and compliance tasks, such as identifying emails older than seven years or locating messages related to ongoing litigation. This saves time and ensures consistency.
- Train Staff on Search Operators: Educate employees and administrators on how to use advanced search operators (e.g.,
AND,OR,NOT, date ranges). Proper training empowers users to find information quickly and accurately. - Use Batch Operations: Leverage your email platform’s ability to apply retention tags or deletion commands to entire sets of search results. This allows for the efficient management of thousands of emails at once.
- Leverage Full-Text Search: Platforms like Typewire offer powerful full-text search capabilities. Use this feature to create data-driven retention strategies that can identify and manage emails based on their actual content, not just metadata.
5. Create Litigation Holds and Legal Hold Procedures
A standard email retention policy best practice involves routine data disposal, but there are critical exceptions. When litigation or a regulatory investigation is reasonably anticipated, your organisation must suspend its normal deletion schedules and preserve all relevant electronically stored information (ESI), including emails. This process, known as a litigation hold or legal hold, is a formal directive to prevent spoliation, which is the intentional or negligent destruction of evidence.
Implementing a clear legal hold procedure is not just a recommendation; it is a legal requirement. Failure to do so can result in severe consequences, including sanctions, adverse inference rulings where a court assumes the destroyed evidence was unfavourable, and significant financial penalties. A robust hold process ensures that your email security framework can adapt to legal demands without compromising its core data management principles.

Practical Implementation Examples
- Employment Dispute: An HR manager receives a letter from an ex-employee's lawyer alleging wrongful dismissal. The company’s legal team immediately issues a hold on all emails belonging to the employee, their direct manager, and relevant HR staff.
- Regulatory Investigation: A financial services firm is notified of an inquiry by the Ontario Securities Commission (OSC). A legal hold is placed on all communications related to the specific trading activities under investigation for all involved traders and compliance officers.
- Patent Infringement Claim: A technology company receives a cease-and-desist letter threatening a patent infringement suit. A hold is initiated to preserve all emails and documents from engineers and executives involved in the development of the disputed product.
Actionable Tips for Implementation
To build a defensible legal hold process, your organisation should:
- Formalise Written Procedures: Develop a clear, documented legal hold policy. This document should detail the triggers for a hold, the roles and responsibilities of legal and IT teams, and the precise steps for implementation and release.
- Use Standardised Templates: Create pre-approved legal hold notice templates to ensure prompt, clear, and consistent communication with custodians (the employees whose data is on hold).
- Establish Rapid Notification: Create a streamlined communication channel between your legal department and IT administrators. This ensures holds can be implemented swiftly on your hosted email platform as soon as the legal trigger is identified.
- Suspend Automated Deletion: Work with your IT team or email provider to ensure that accounts or messages under a legal hold are flagged and exempted from automated deletion policies. This is a crucial technical control.
- Document Everything: Maintain meticulous records of when each hold was initiated, who it applies to, the reason for the hold, and when it was released. This documentation is vital for demonstrating compliance.
- Consult Legal Counsel: Regularly review your legal hold procedures with legal counsel to ensure they align with the rules of civil procedure in your jurisdiction and meet current legal standards.
6. Establish Data Residency and Secure Storage Requirements
An essential component of modern email retention policy best practices involves defining where your data lives. Data residency requirements mandate that specific types of information, particularly personal and sensitive data, must be stored, processed, and managed within a particular geographical jurisdiction, such as Canada. This isn't merely a logistical preference; it's a critical legal and security measure to ensure compliance with privacy laws like PIPEDA and to protect data from foreign access requests.
By clearly documenting and enforcing data residency via your chosen hosted email platform, your organisation gains control over its data sovereignty. This ensures that your email archives are subject only to Canadian laws, shielding them from foreign jurisdictions with different privacy standards. Furthermore, pairing residency with secure storage requirements, like end-to-end encryption and robust access controls, creates a formidable defence for your most sensitive communications, building trust with clients and stakeholders.
Practical Implementation Examples
- Financial Services: A wealth management firm in British Columbia chooses a Canadian-owned and operated email hosting provider to ensure all client financial data remains within Canada, fulfilling its obligations under provincial privacy laws and industry regulations.
- Healthcare Organisations: A telehealth provider in Ontario maintains all patient email communications on servers located exclusively within the country to comply with the Personal Health Information Protection Act (PHIPA) and safeguard patient confidentiality.
- Government Contractors: An engineering firm working on federal infrastructure projects requires its email provider to guarantee all project-related data is hosted on Canadian soil to meet strict contractual and security clearance requirements.
Actionable Tips for Implementation
To effectively establish and maintain data residency and security, follow these key steps:
- Verify Provider Infrastructure: When selecting a hosted email platform, demand proof that their entire infrastructure, including primary and backup data centres, is located within Canada. This verification is crucial for true data sovereignty.
- Confirm Encryption Protocols: Ensure the provider uses strong, end-to-end encryption for data both in transit and at rest. The encryption keys should be managed in a way that prevents even the provider from accessing the content of your emails.
- Review Legal and Privacy Policies: Scrutinise the provider's terms of service and privacy policy to confirm they do not share data with non-Canadian entities and explicitly commit to Canadian legal jurisdiction.
- Include Residency in RFPs: Make Canadian data residency a mandatory, non-negotiable requirement in any Request for Proposal (RFP) or vendor selection process for email and archiving services.
- Document and Audit: Keep detailed records of your provider's compliance with data residency rules. You can learn more about data residency requirements for secure hosted email to strengthen your auditing process.
7. Implement Role-Based Access Controls for Retention Administration
To safeguard the integrity of your email retention policy, it is crucial to control who can create, modify, or enforce it. Implementing Role-Based Access Controls (RBAC) on your hosted email platform ensures that only authorised personnel can manage these critical settings. This principle of least privilege is a cornerstone of both strong email security and effective governance, preventing accidental misconfigurations or malicious changes that could compromise your compliance and data privacy.
By assigning specific permissions based on job function, you create a clear separation of duties. This prevents a single user from having unchecked power over the organisation's data lifecycle management. A well-defined RBAC structure makes your email retention policy more defensible during audits or legal proceedings, as it demonstrates a controlled and deliberate approach to data governance. It also enhances overall email security by limiting the number of high-privilege accounts that could be targeted by attackers.
Practical Implementation Examples
- Corporate IT: Only three designated IT administrators have permissions to modify company-wide email retention policies, while help desk staff can only view settings for troubleshooting.
- Human Resources: The HR department manages a separate, more stringent retention policy for employee-related emails, and any changes to this policy require approval from both the HR Director and the IT Director.
- Legal Department: The legal team is granted the authority to place specific mailboxes or email threads on a legal hold, but they cannot alter the underlying retention schedules for other departments.
Actionable Tips for Implementation
To effectively implement RBAC for your email retention policy, follow these key steps:
- Define Clear Roles: Establish distinct roles with specific permissions. Key roles include Policy Creators (who can define schedules), Policy Enforcers (who apply policies), Auditors (who have read-only access to verify compliance), and Regular Users (who have no administrative rights).
- Require Strong Authentication: Enforce multi-factor authentication (MFA) for all administrator accounts with access to retention policy settings. This adds a critical layer of security against unauthorised access.
- Maintain Detailed Audit Logs: Ensure your system, such as a secure hosted email platform, logs all administrative actions related to retention policies. These logs should record who made a change, what was changed, and the exact timestamp.
- Conduct Quarterly Access Reviews: Regularly review who has which permissions. This practice ensures that access rights remain appropriate as employee roles change and prevents the accumulation of unnecessary privileges.
- Use Centralised User Management: Employ platforms that offer centralised user management to enforce RBAC consistently across your email environment. This simplifies administration and reduces the chance of misconfiguration.
8. Conduct Regular Audits and Maintain Detailed Audit Trails
An email retention policy is only effective if it is consistently enforced. Regular audits and detailed, immutable audit trails are essential mechanisms for verifying that your policy is functioning as intended. This practice involves systematically reviewing your hosted email platform's archives and processes to ensure compliance, identify gaps, and prove that data is being managed according to your documented schedules. It is a critical component of any robust data governance framework.
Maintaining a comprehensive audit trail provides an irrefutable record of all actions taken on your email data, from creation and retention to eventual deletion. This log is your primary evidence for demonstrating compliance to regulators and defending against legal claims of spoliation. For organisations prioritising email security, these trails are also invaluable for investigating potential data breaches or unauthorised access, making them a cornerstone of modern email retention policy best practices.

Practical Implementation Examples
- Quarterly Compliance Checks: An IT team conducts quarterly audits by randomly sampling 5% of user mailboxes to verify that automated retention and deletion rules are being applied correctly.
- Third-Party Verification: A financial technology company undergoes an annual third-party audit of its email retention program to maintain its SOC 2 compliance certification.
- Litigation Readiness: During a legal dispute, a corporation provides its audit trail to prove that specific emails were deleted automatically as part of its standard, pre-existing policy, not with malicious intent.
Actionable Tips for Implementation
To build a strong audit and logging program for your email retention policy, follow these steps:
- Establish a Formal Audit Schedule: Define a regular cadence for audits, such as quarterly internal reviews and annual external assessments, and document this schedule in your policy.
- Create Standardised Audit Procedures: Develop detailed checklists for auditors to follow. These should cover mailbox sampling, review of audit logs for exceptions, and verification of active legal holds.
- Implement Immutable Logging: Ensure your email hosting platform or archiving solution generates immutable audit logs that cannot be altered or deleted. These logs must be stored securely and separately from the primary email infrastructure.
- Capture Comprehensive Log Details: Your audit trails must capture critical data for each action: a precise timestamp, the user identity or system process involved, the specific action taken (e.g., deleted, archived), a unique email identifier, and the policy that was applied.
- Track and Remediate Findings: Document all audit findings, including areas of non-compliance. Assign responsibility and set clear timelines for remediating any identified gaps, then track them to completion.
- Report Results to Leadership: Summarise audit results and remediation progress in reports for senior management and compliance committees to ensure visibility and accountability.
9. Develop Clear Email Retention Training and User Communication
An email retention policy is only effective if employees understand and adhere to it. Therefore, developing a comprehensive training and communication program is not just an administrative task; it is a critical component of your email privacy and security framework. This program bridges the gap between policy documentation and daily practice, ensuring that users know precisely what is expected of them regarding email management.
Clear, consistent communication and training empower employees to become active participants in protecting organisational data. When staff understand the "why" behind the rules, such as enhancing email security and respecting customer privacy, they are more likely to comply. This proactive approach minimises the risk of accidental non-compliance, reduces the likelihood of data spillage, and fosters a culture of security-consciousness across the entire organisation.
Practical Implementation Examples
- Financial Services: A credit union conducts mandatory annual retention compliance training for all staff, with a quiz to verify comprehension of policies related to client financial data and anti-money laundering (AML) record-keeping.
- Healthcare Organisation: A hospital distributes updated HIPAA-compliant retention guidelines whenever there are changes to provincial privacy laws, requiring all clinical and administrative staff to sign an acknowledgement form.
- Technology Company: A software-as-a-service (SaaS) provider sends monthly 'Data Governance Tips' emails to all employees, reminding them of key retention policies, especially concerning the handling of sensitive customer data on their hosted email platform.
Actionable Tips for Implementation
To build an effective training and communication strategy, follow these key steps:
- Integrate into Onboarding: Include a dedicated module on the email retention policy in your new hire onboarding process. This ensures that every employee understands their responsibilities from day one.
- Create Department-Specific Guidance: Different departments handle different types of data. Develop tailored training materials for teams like HR, finance, and legal that address their unique retention requirements and common scenarios.
- Use Multiple Formats: Cater to diverse learning styles by offering training in various formats, such as written guides in the employee handbook, live webinars, interactive e-learning modules, and short video tutorials for remote teams.
- Communicate Policy Importance: Have leadership, particularly from legal or IT security, communicate the importance of the policy. Endorsement from senior management significantly increases employee buy-in and perceived importance.
- Emphasise Privacy and Security Benefits: Frame the policy not just as a rule to follow but as a crucial practice for protecting customer privacy and strengthening the organisation's overall email security posture against breaches.
10. Establish Exception Procedures for Important and Litigation-Related Communications
While standardised retention schedules are crucial, a robust policy must also account for exceptions. Certain communications will invariably require preservation beyond their scheduled deletion date due to their strategic importance or connection to legal matters. An exception procedure provides a formal, documented workflow to identify, preserve, and manage these critical emails without undermining the entire policy.
This process ensures that vital information, such as regulatory correspondence or emails relevant to a lawsuit, is not inadvertently destroyed by automated systems. By creating a clear framework for exceptions, your organisation can meet its legal obligations for preservation while still adhering to the principle of data minimisation for all other communications. It formalises the "when and why" of extended retention, making the process defensible, auditable, and integral to a comprehensive email security strategy.
Practical Implementation Examples
- Legal Department: Emails from external counsel concerning an ongoing intellectual property dispute are placed under a specific litigation hold, flagging them for indefinite retention until the case is officially closed.
- Customer Service: A series of emails detailing a significant customer service failure and potential dispute are flagged by a manager for a 12-month extended retention period, anticipating a potential claim.
- Executive Team: Communications and materials related to a major merger or acquisition are placed in a special archive with an extended retention period to satisfy corporate governance and regulatory review requirements.
Actionable Tips for Implementation
To build an effective exception process into your email retention policy best practices, follow these key steps:
- Define Clear Criteria: Develop and document specific guidelines detailing what qualifies for an exception, such as regulatory inquiries, active litigation, or critical project documentation.
- Implement Technical Flags: Use your email platform’s features, like labels in private email hosting services or specific folders, to visibly mark communications subject to an exception. This provides a clear visual cue to both users and automated systems.
- Establish an Approval Workflow: Require managerial or legal department approval before an email can be designated as an exception. This prevents misuse and ensures that only genuinely critical data is over-retained.
- Set Expiration Dates: No exception should be indefinite. Assign a review or expiration date to every hold to prevent a "keep forever" mentality, which reintroduces privacy and security risks.
- Integrate with Legal Hold Processes: Ensure your exception procedures are fully integrated with your official litigation hold notification system. When Legal issues a hold, the relevant emails should be automatically flagged for preservation.
- Document and Audit: Maintain a clear audit trail for every exception, documenting who requested it, the justification, the approval, and the expiration date. Regularly review all active exceptions to release holds that are no longer necessary.
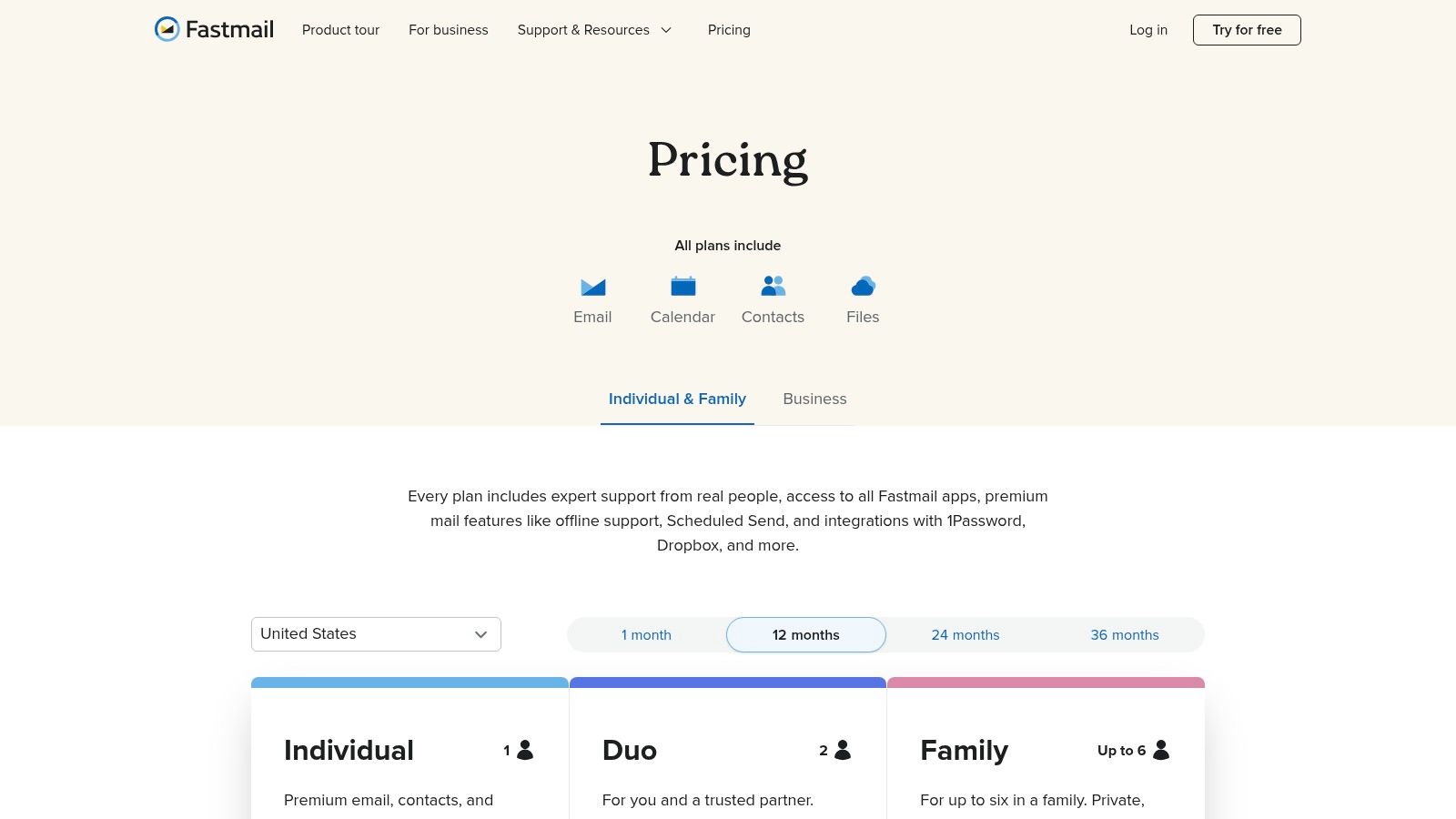
10-Point Email Retention Best Practices Comparison
| Policy / Practice | 🔄 Complexity (Implementation) | ⚡ Resources (Requirements) | 📊 Expected outcomes | 💡 Ideal use cases | ⭐ Key advantages |
|---|---|---|---|---|---|
| Establish Clear Retention Schedules Based on Regulatory Requirements | Medium — policy drafting, legal review, periodic updates | Moderate — legal counsel, compliance owners, documentation effort | Ensures regulatory compliance; consistent disposal; reduced storage costs | Regulated industries (finance, healthcare, legal); PIPEDA-bound orgs | Strong compliance posture; audit defensibility; predictable retention |
| Implement Automated Deletion Policies with Safeguards | Medium — rule configuration, testing, exception handling | Moderate — engineering, backup/archival integration, audit logging | Consistent enforcement; reduced manual work and storage overhead | High-volume/low-risk streams (marketing, alerts, resolved tickets) | Automates retention; minimizes human error; scalable |
| Separate Personal and Business Email for Retention Purposes | Low — policy plus aliases/filters; relies on user discipline | Low — domain/alias setup, training, periodic audits | Clear privacy boundaries; reduced accidental personal data retention | BYOD environments; remote teams; freelancers and consultants | Protects personal privacy; simplifies compliance scope |
| Utilize Advanced Search and Categorization for Efficient Retention Management | Medium — taxonomy design, saved searches, admin training | Moderate — search tooling, maintenance, user training | Faster discovery; precise policy targeting; improved audit support | Legal discovery, audits, finance/HR investigations | High accuracy in locating/classifying emails; reduces manual review |
| Create Litigation Holds and Legal Hold Procedures | High — rapid legal‑IT coordination, strict documentation | High — legal oversight, storage overhead, tracking systems | Preserves evidence; reduces spoliation risk; supports discovery | Any pending litigation or regulatory investigation | Critical for legal defensibility; prevents sanctions |
| Establish Data Residency and Secure Storage Requirements | Medium — vendor assessment, contractual & audit work | High — secure domestic infrastructure, regular audits, higher costs | Ensures data sovereignty; mitigates foreign access risk; regulatory alignment | Organizations subject to national residency rules (e.g., Canada/PIPEDA) | Strong privacy guarantees; customer trust; legal compliance |
| Implement Role-Based Access Controls for Retention Administration | Medium — role definitions, approval workflows, reviews | Moderate — IAM tooling, admin effort, MFA, periodic audits | Limits unauthorized changes; increases accountability and auditability | Medium–large orgs with multiple departments or compliance teams | Enforces separation of duties; prevents misuse; provides audit trails |
| Conduct Regular Audits and Maintain Detailed Audit Trails | High — scheduling, log management, forensic capability | High — audit teams, long‑term log storage, tooling, possible 3rd‑party audits | Detects non‑compliance early; documents remediation; supports legal defense | Highly regulated industries (finance, healthcare, legal) | Essential for compliance verification; proactive risk reduction |
| Develop Clear Email Retention Training and User Communication | Low — create materials and rollout, periodic refreshers | Moderate — L&D resources, communications channels, time | Increased voluntary compliance; fewer accidental retention errors | All organizations, especially during policy changes or rollouts | Improves user behavior; scalable compliance through education |
| Establish Exception Procedures for Important and Litigation‑Related Communications | Medium — criteria, approval flows, expiration management | Moderate — workflow tooling, legal/admin review, tracking | Preserves critical communications while avoiding indefinite retention | Organizations with frequent disputes, board communications, regulatory matters | Flexible targeted preservation with controls; reduces accidental loss |
Building a Resilient and Privacy-Focused Email Strategy
Implementing robust email retention policy best practices transforms your inbox from a compliance challenge into a strategic asset. By uniting clear schedules, automation, privacy-first platform choices and ongoing training, you ensure every message lifecycle is managed with confidence and care.
Key Insights from These Email Retention Policy Best Practices
• Define retention schedules aligned to industry and provincial regulations
• Automate deletion policies with safeguards to prevent accidental data loss
• Segment personal and business mailboxes for tailored retention rules
• Use legal holds and incident procedures to freeze critical records
• Enforce Canadian data residency and encrypted storage for privacy
• Apply role-based access controls and detailed audit trails
• Deliver engaging, concise user training on policy requirements
• Document exception workflows for litigation or strategic communications
Each insight reinforces how automation, structure and privacy-conscious controls work together. Adopting these measures ensures your organisation meets regulatory obligations and respects user privacy.
Actionable Next Steps
- Appoint a retention policy owner to oversee schedules and exceptions.
- Map your email categories against federal and provincial retention mandates.
- Configure your hosted email platform—ideally a privacy-first solution—to enforce automated deletion cycles.
- Enable legal hold toggles in your archive centre to capture litigation-related threads.
- Schedule quarterly audits to verify data residency, encryption standards and access logs.
- Roll out bite-sized training modules on recognising retention triggers and exceptions.
- Review exception reports monthly and refine criteria for important communications.
Tackle each step methodically to embed best practices into daily operations and maintain continuous compliance.
Sustaining Continuous Improvement
Organisations grow more resilient when they treat email retention as an evolving practice not a one-off project. Regularly revisit your policies in light of new privacy guidelines, platform updates and feedback from your IT and legal teams. Use feedback loops—such as post-audit reviews and user surveys—to refine schedules, automation rules and training materials. This iterative approach cements a culture of accountability and proactivity.
The Value of Mastering These Concepts
“An email retention policy is only as strong as the systems and people enforcing it.”
Mastering these retention principles shields your organisation from legal risks, minimises storage costs and bolsters trust with clients and regulators. A well-executed policy elevates your security posture, demonstrating commitment to privacy and compliance.
Broader Impact and Final Thought
When you align email retention policy best practices with a privacy-first ethos, you create more than just a compliance framework—you cultivate a secure communication environment that supports growth. Privacy-conscious individuals, SMB owners and IT administrators gain peace of mind knowing every email has a clear lifecycle and robust protections.
Embrace this strategic approach today and position your organisation for stronger security, streamlined operations and enhanced regulatory readiness. Your next email could be the one that matters most—make sure it’s managed with care.
Ready to take your email retention policy best practices to the next level? Discover how Typewire can help you enforce clear retention schedules, automated deletion, Canadian data residency and advanced security controls in one privacy-first platform.
Explore more at Typewire to start building a compliant, secure and resilient email strategy.